A portion of the internet went down after suffering a crippling blow from a series of global attacks on a cloud-based Internet Performance Management (IPM) company, called Dyn. Major websites including Twitter, Reddit, Spotify and even game servers for Battle Field 1 have been affected.
This was all made possible by an unknown group of malicious actors that targeted a DDoS attack on a company called Dyn. Dyn provides an internet DNS system which allows users to connect to websites by routing a human readable internet address to their corresponding IP addresses. For example, http://webroot.com becomes: 66.35.53.194.
Dyn was being overloaded by requests from tens of millions of IP addresses all at once, causing their service to go down. Imagine a one-lane highway designed to handle the traffic flow of about 100 cars per hour. Then imagine that the same highway was suddenly riddled with over 10,000 cars. This would cause a bottleneck so severe, that the traffic would just stop. That’s essentially what happened Friday morning with Dyn.
The internet is a superhighway with destinations to a number of IP addresses rather than the actual domains of the websites. The issue is that there has to be a record of what websites and domains translate to what IP addresses. A Top Level Domain (TLD) provides that service, and they are the answer to the question of which name belongs to each IP address.
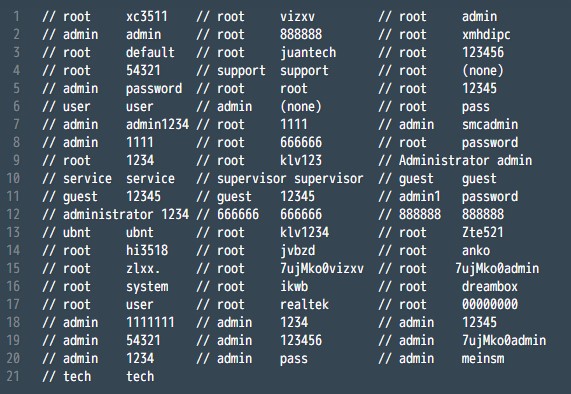
In this case, it’s been confirmed that an Internet of Things botnet, called Mirai, has been identified as a participant in the well planned and sophisticated attacks. The motive for this attack is only being speculated, given that the actual actors for the attacks have not yet surfaced or explained their intent.
Dyn has released an update on the DDoS event here, and you can subscribe for real-time updates on the status of the attack.