A lot happens in the security world and many stories get lost in the mix. In an effort to keep our readers informed and updated, we present the Webroot Threat Recap, highlighting 5 major security news stories of the week.
Quicktime for Windows No Longer Supported
This week, Microsoft announced they would no longer be supporting the Quicktime media player and strongly recommended to completely uninstall it in order to avoid any malicious attack through the software, which will no longer receive patches. Several flaws have been found that could leave users open for attackers to access and infect the system. At present, the Mac version of Quicktime is still being supported with security updates.
http://n4bb.com/uninstall-quicktime-windows-microsoft-stops-support/
Security Flaw Leaves Phone Users Vulnerable
Most telecom companies around the world use the same routing protocol, SS7, for allowing users to contact others around the globe. However, SS7 also allows access to an individual phone and can even be maliciously aimed at gaining call recordings, geographical locations, and other personal information. This flaw, while dangerous in the hands of cyber criminals, is also used by the NSA and other intelligence agencies for data gathering and monitoring for suspicious activities.
Cyber Security Lacking in Majority of Companies
In a recent threat intelligence report, it was discovered that over 75% of business organizations have no method of response for cyber attacks, and only obtain these critical services after they have been targeted. While individual sectors are seeing a steady rise in malware attacks on their systems, it’s difficult to believe that a large portion are still unprepared for the attacks being reported in the news on a daily basis. And yet, here we are.
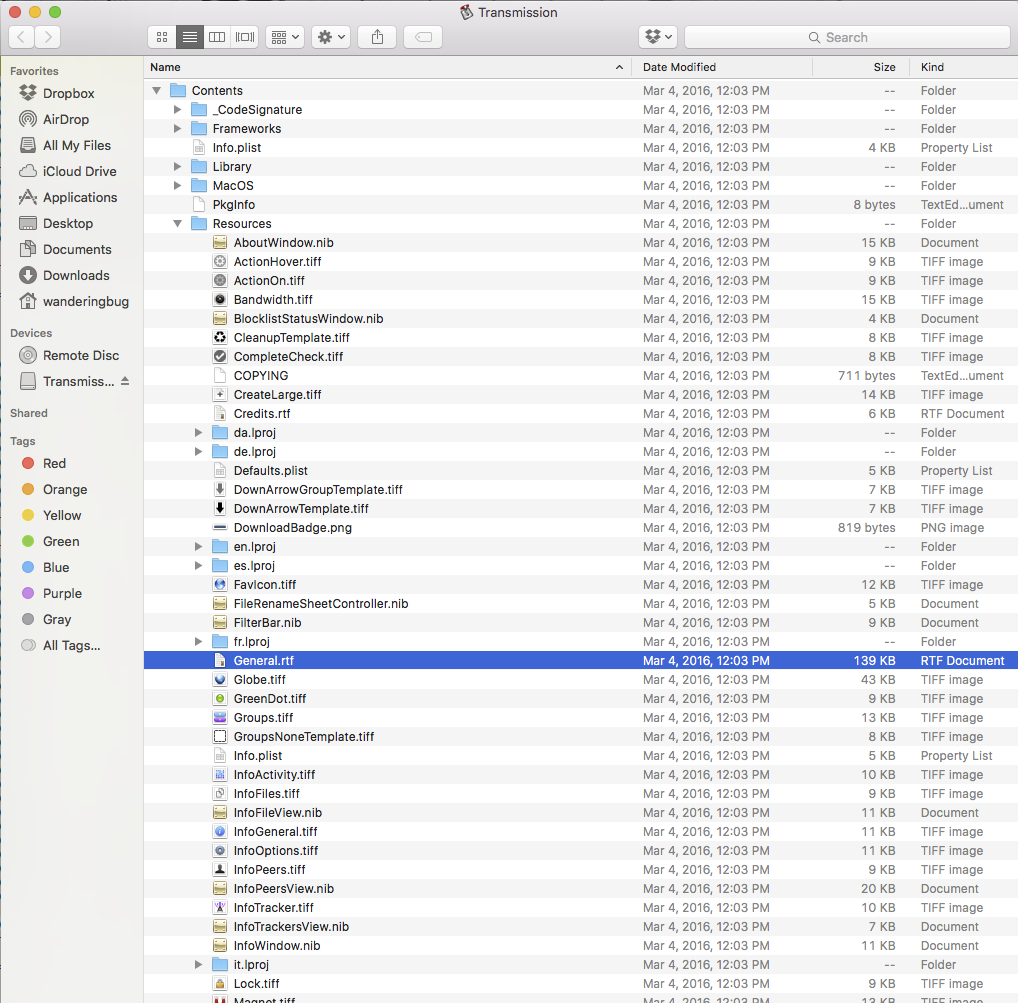
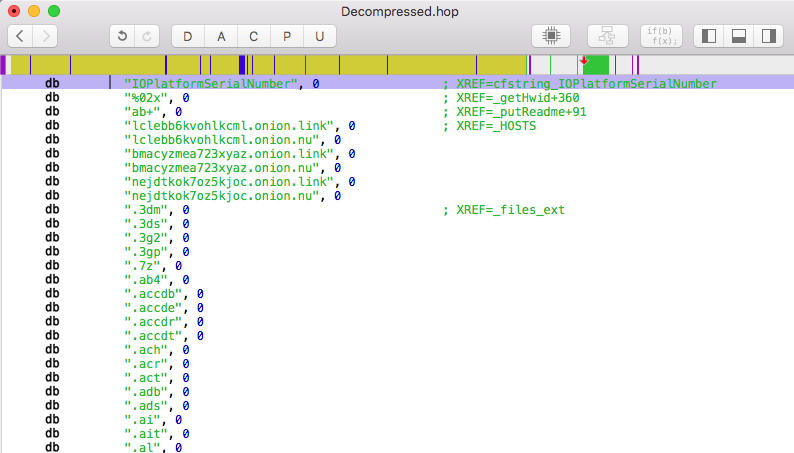
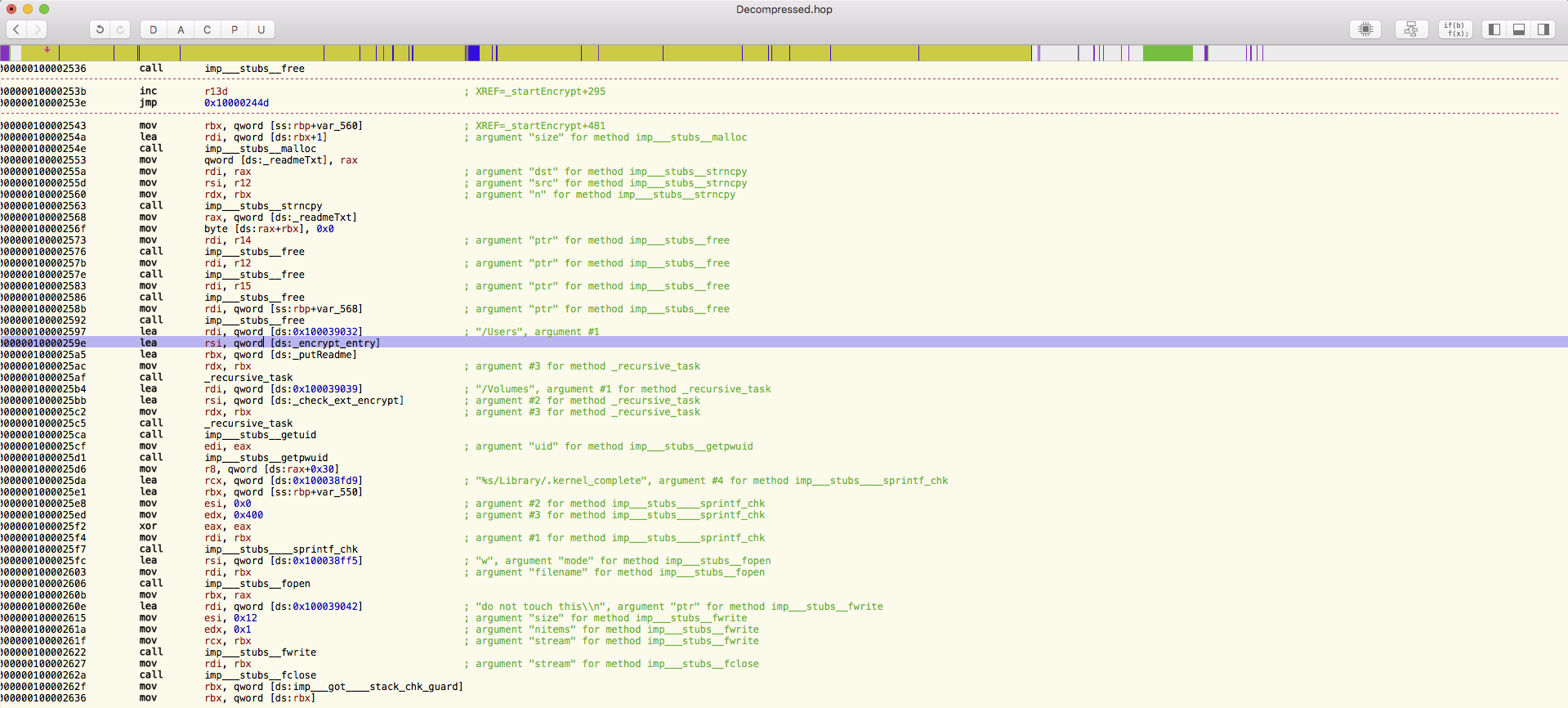
Latest Encrypting Ransomware Aims at Bitcoin
In the past week, a new ransomware variant known as CryptXXX has been spotted in the wild that will both encrypt your data and steal bitcoins and other sensitive information located on the system. It appears to be from the same creators as Reveton, an older variant of encrypting ransomware, but with several advances that help it access stored passwords and lock users out of the system.
http://bravenewcoin.com/news/cryptxxx-set-to-become-the-worst-bitcoin-stealing-ransomware-yet/
End-to-End Message Encryption On the Rise
With the recent news about the FBI breaking Apple’s encryption to access sensitive information, more and more companies are working towards enhancing their current encryption standards. Viber, which makes the popular messaging app, has just announced they will be providing full end-to-end encryption for any and all data sent in messages, though it will take some time for all of its 700 million users to update to the latest version. Moreover, with Viber being an Israel-based company, they will not be directly affected by any US Congress decisions regarding encryption and the governments ability to access encrypted information.