Cyber threats come from a wide array of sources, but can be grouped into three categories:
Hacktivists
These are tech-savvy individuals who are normally motivated by morality. These individuals are also classed by many (including the FBI) as terrorists. One of the main hactivist groups out there is anonymous. This group rose from one of the most popular image boards on the internet, 4chan, where users could post anonymously. Many of the influential figures in 4chan have now left, including the board founder moot (Christopher Poole). 4chan is no longer the entity it used to be. One of the most infamous attacks conducted by anonymous was Project Chanology, where the group targeted scientology. Famously anonymous retrieved a video of Tom Cruise from the scientology group that was not intended to be seen by the general public: https://www.youtube.com/watch?v=UFBZ_uAbxS0
Cyber Criminals
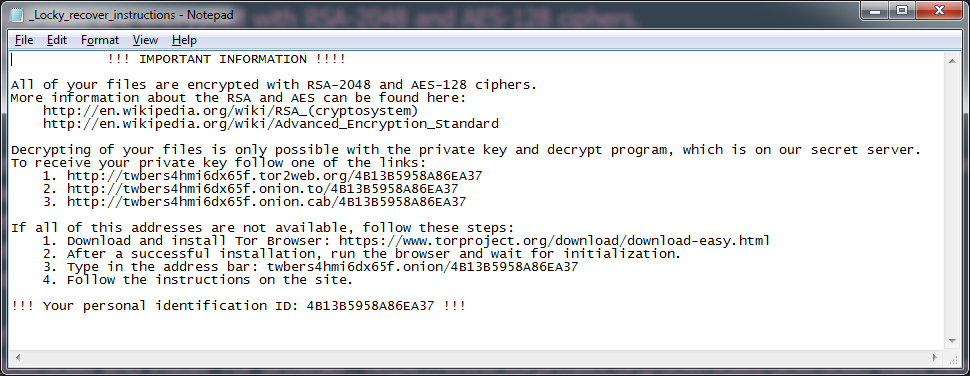
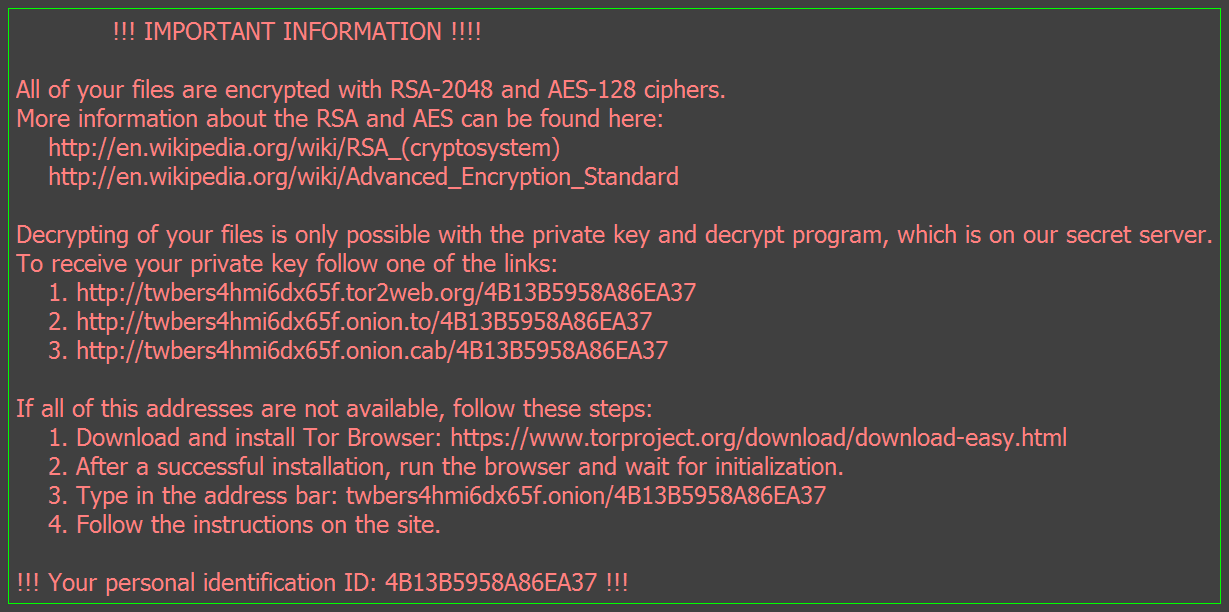
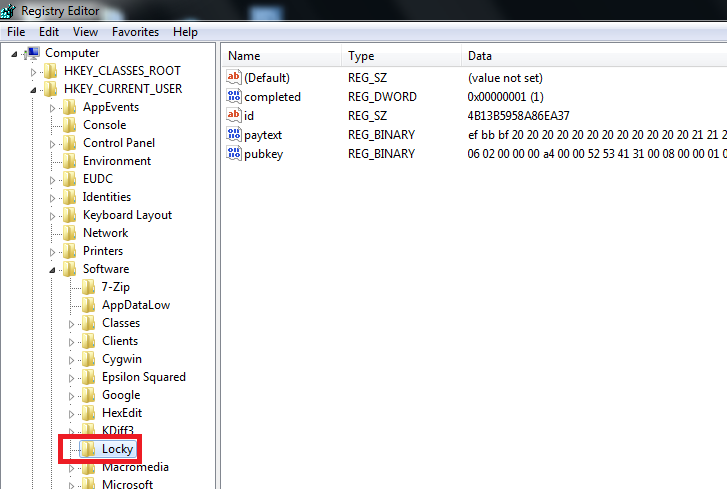
These are individuals who are motivated by money. These are the people who are responsible for the distribution of ransomware. This is a very lucrative business. It was reported in 2013 that cryptolocker made over $30 million in 100 days. Politcal borders make it appealing for criminals to employ these tactics of making money as it is very hard to prosecute them. The encryption that ransomware hits these machines with is normally unbreakable, with the FBI encrouraging individuals to pay the ransom: http://uk.businessinsider.com/fbi-recommends-paying-ransom-for-infected-computer-2015-10?r=US&IR=T .
It has been observed that some ransomware variants have holes and can be cracked (most notably the linux encoder variant which was targeting web servers). Ransomware isn’t the only tactic cyber criminals employ. Another tactic they employ are botnets. This is where a criminal infects your computer, unknowingly to the individual. The criminal can then take control of the victims computer at any time for whatever purpose they see fit. Normally the attacker will either extract information from the victim, monitor the victim or use the victims computer to attack other systems. A recent case to note in relation to botnets is the arrest of one of the administrators of the Dridex botnet, Andrey Ghinkul. This arrest shows that law enforcement are making a good effort to tackle this problem.
State-Sponsored Threat Actors
These are individuals who are sponsored by a government. They act in political interest of the government sponsoring them. It has been reported by FireEye that China has over 20 APT (advanced persistent threat) groups. APT1 (dubbed by Mandiant) is linked with China’s PLA Unit 61398. It is believed this unit occupies a 12 story building employing hundreds of hackers. These groups pose a particular threat to the US, with the FBI putting some of the people involved on their most wanted list: https://www.fbi.gov/news/news_blog/five-chinese-military-hackers-charged-with-cyber-espionage-against-u.s . China isn’t the only country known for sponsoring cyber attacks. The revelations of Edward Snowden reveals much on the NSA’s antics. Another example of a state sponsored cyber attack is where Turkeys internet servers were attacked a couple of months ago, with the blame being pointed at Russia: http://www.todayszaman.com/anasayfa_political-hackers-suspected-as-turkey-suffers-intense-cyber-attack_407781.html