Cybercriminals continue to systematically release DIY (do-it-yourself)type of cybercrime-friendly offerings, in an effort to achieve a ‘malicious economies of scale’ type of fraudulent model, which is a concept that directly intersects with our ‘Cybercrime Trends – 2013‘ observations.
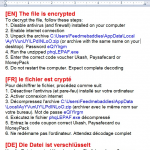
We’ve recently spotted yet another subscription-based, DIY keylogging based botnet/malware generating tool. Let’s take a peek inside its Web based interface, and expose the cybercrime-friendly infrastructure behind it.
More details: