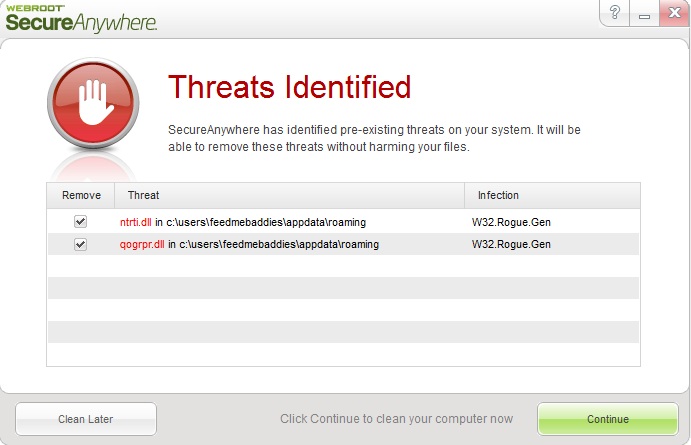
Following last week’s profile of yet another InstallCore Potentially Unwanted Application (PUA) campaign, we detected another rogue ad campaign this week. This time enticing E.U based users into downloading and installing a fake “Free Codec Pack”, with the users sacrificing their privacy in the process due to the additional toolbars that will be installed on their PCs.
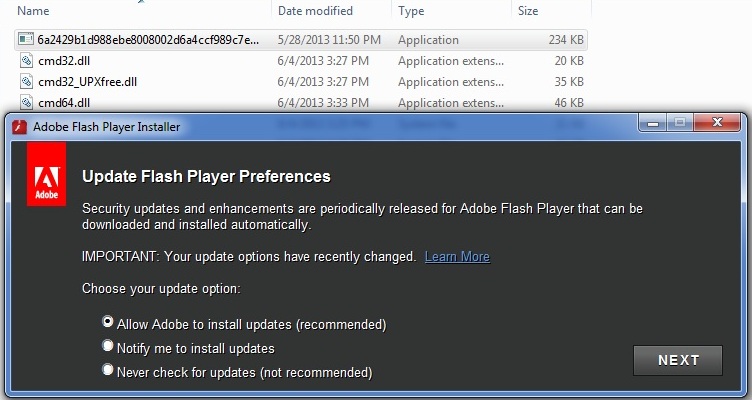
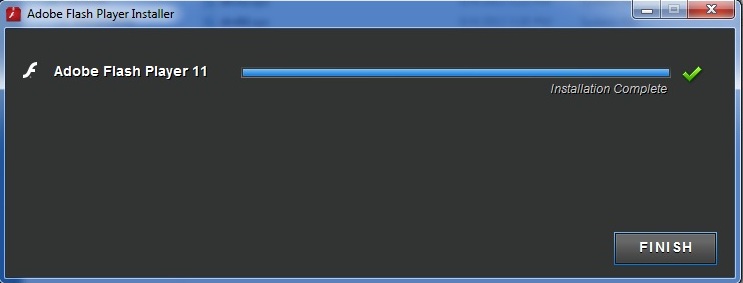
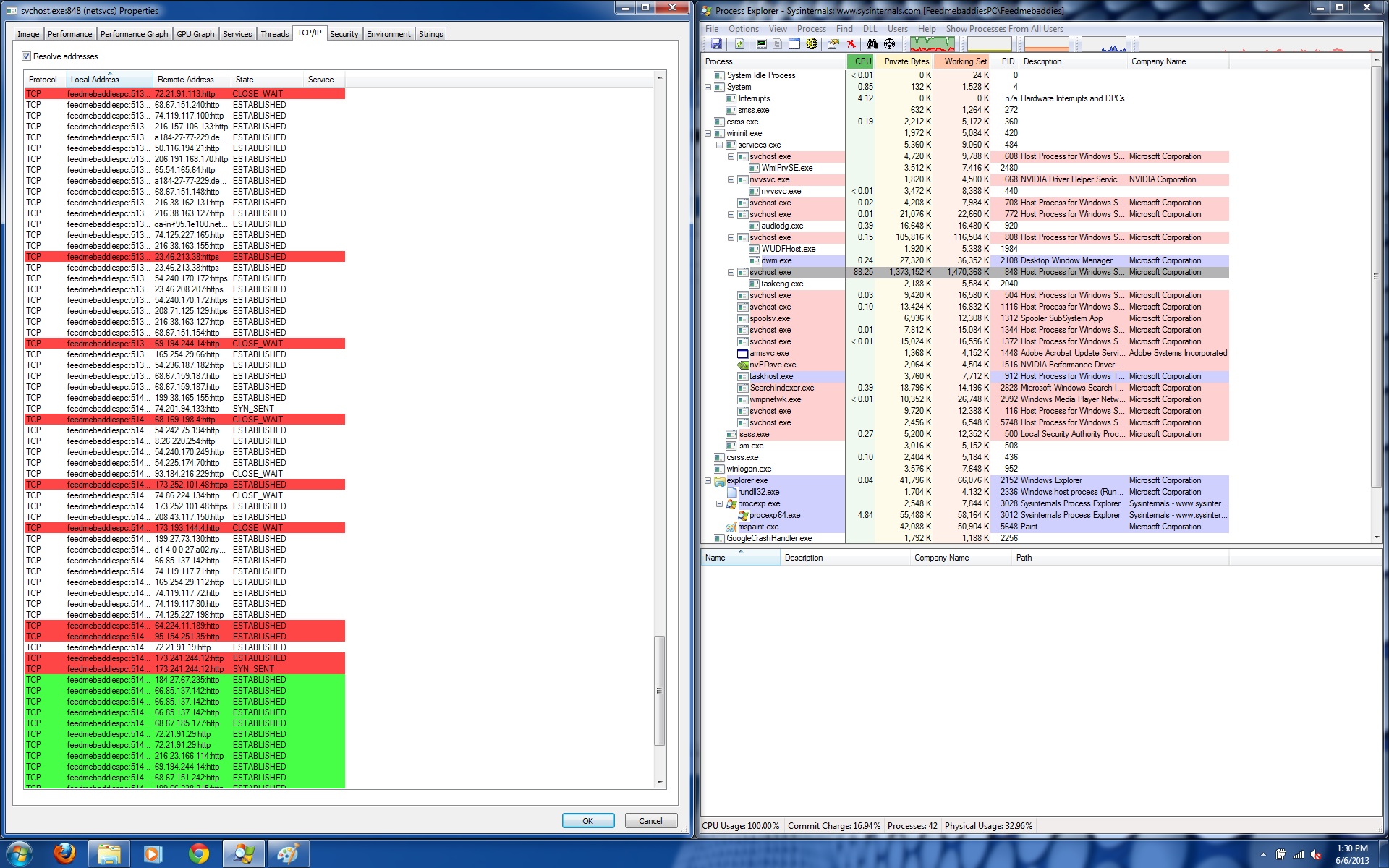
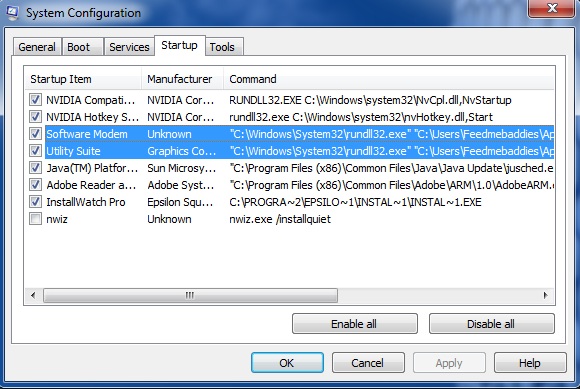
More details: