By Dancho Danchev
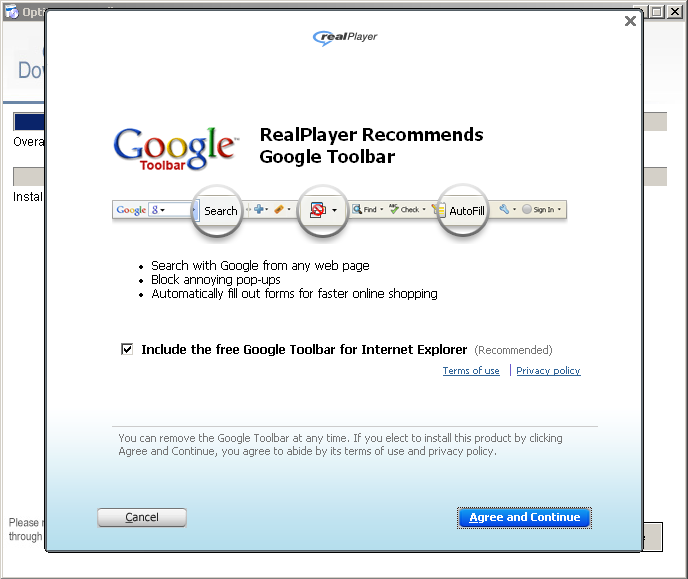
Fraudsters are currently spamvertising tens of thousands of emails enticing users into installing rogue, potentially unwanted (PUAs) casino software. Most commonly known as W32/Casonline, this scam earns revenue through the rogue online gambling software’s affiliate network.
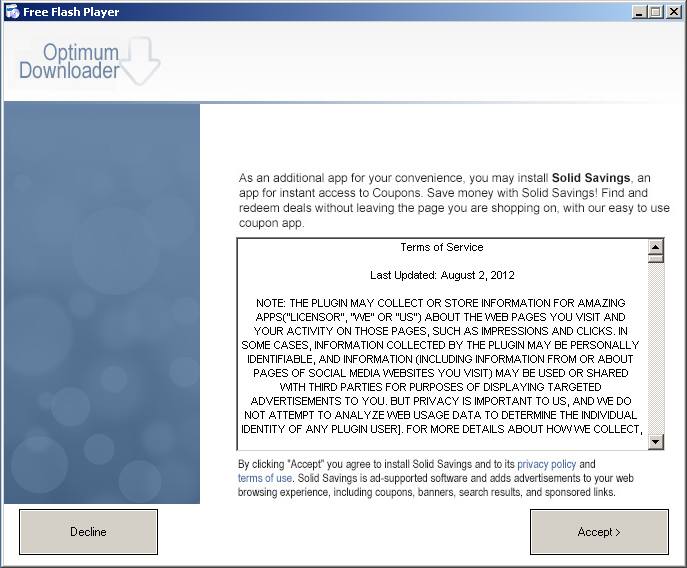
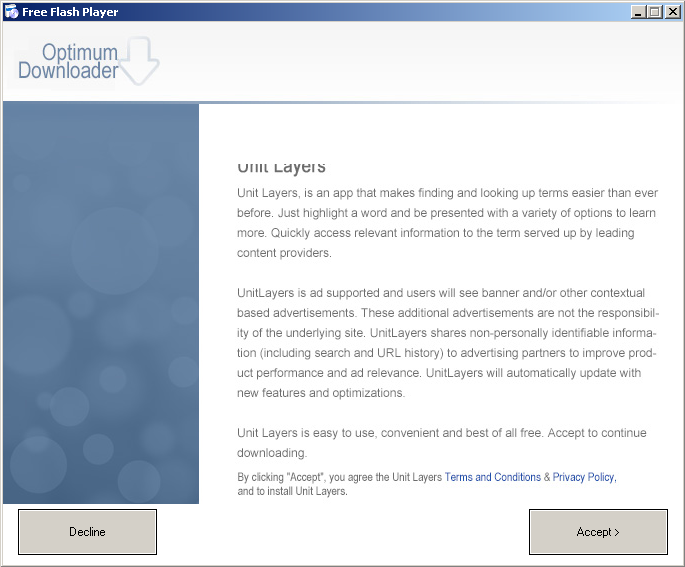
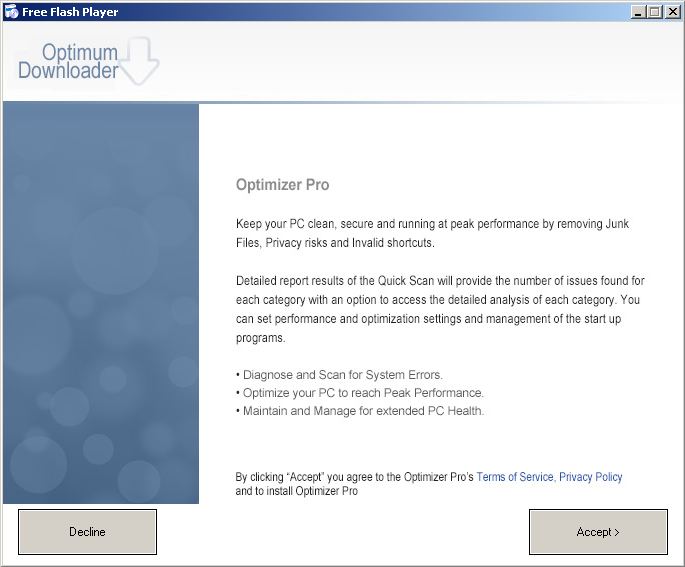
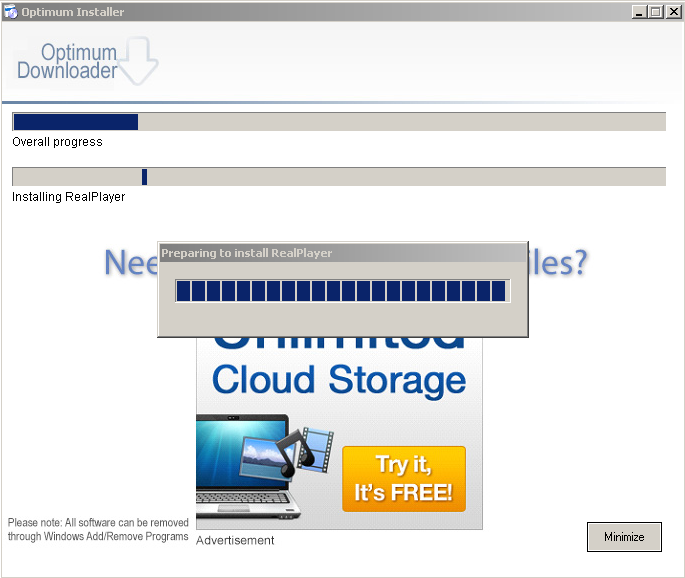
More details: