When you sign up for a credit card — even with one of those pre-approved applications — you still have to provide the bank with your name, address, mother’s maiden name, social security number, and a host of other personally identifiable information. Once the bank issues the card, it shouldn’t ever need to ask you for all of that information again. But a phishing scam making the rounds this week — one that appears to be targeted at holiday shoppers who buy gifts online — aims to fool victims into doing just that.
When you sign up for a credit card — even with one of those pre-approved applications — you still have to provide the bank with your name, address, mother’s maiden name, social security number, and a host of other personally identifiable information. Once the bank issues the card, it shouldn’t ever need to ask you for all of that information again. But a phishing scam making the rounds this week — one that appears to be targeted at holiday shoppers who buy gifts online — aims to fool victims into doing just that.
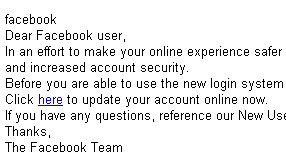
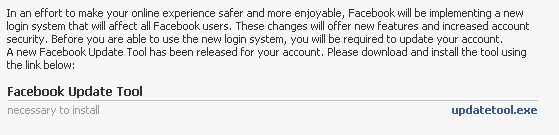
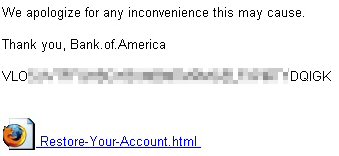
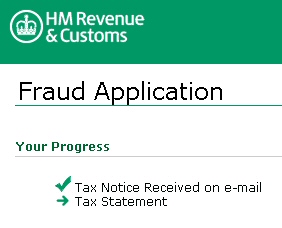
The scam begins with an email, informing the recipient that they can sign up for Verified by Visa, a real program offered by the eponymous credit card company. The email links to a bogus page (part of which is shown at left) designed to lure an unsuspecting online shopper into the trap. (And this is only one of several scams you should watch for, leading up to Black Friday, Cyber Monday, or whenever it is you decide to go online for deals on that fruit basket for Grandma. Webroot released findings today on additional data-stealing malware, and the larger pool of online shoppers this year which it appears to be targeting.)
Once you register with the (real) Verified by Visa service, participating merchants permit you to enter a password in addition to your card information. In addition to providing the purchaser with an additional layer of safety, the password also gives the merchant some assurance that larger-than-normal transactions (like the ones you make during holiday shopping season) will be approved quickly, without triggering fraud alerts.
The thing is, you don’t have to go to a special Web page to sign up for Verified by Visa. You are supposed to be offered the chance to sign up while you’re completing your purchase on the participating merchant’s Web site, as you’re entering your billing details. The Visa Web site spells this out in a simple graphic (though there have been some interesting problems with the way the system works).
In the phishing scam, you’re sent to a Web page that asks you for, essentially, all the information you gave the card-issuing bank at the time you first signed up for the credit card. That’s Red Flag #1, but it’s worth repeating: In a real sign-up form for Verified by Visa, you won’t be asked to provide your mother’s maiden name, social security number, birthdate, or any other sensitive details that you wouldn’t otherwise enter into a Web-based order form while shopping online.