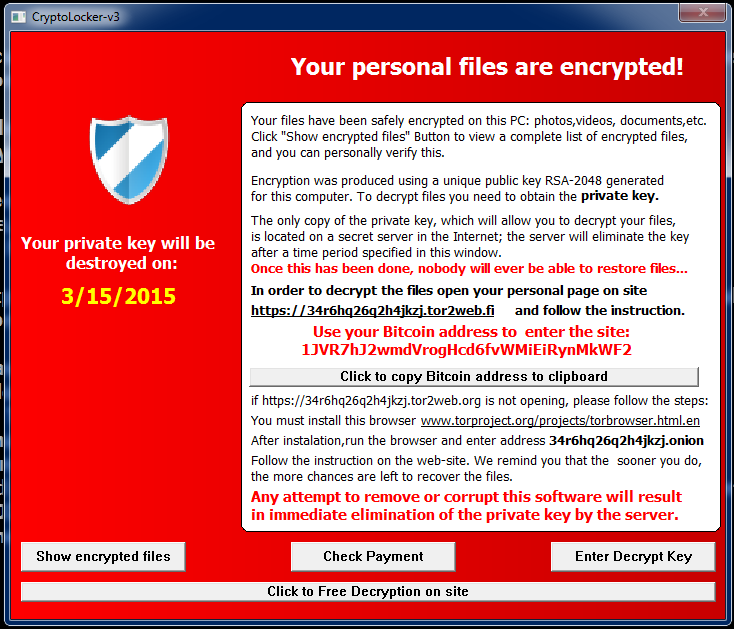
Breaches big and small have been in the news, from small organizations losing banking files to global groups like Sony losing seemingly everything to hackers. But with the recent Office of Personnel Management (OPM) hack that was revealed recently, with anywhere between 18 and 32 billion individual records stolen by digital infiltrators, we have not seen a breach to this scale.
The scary, and somewhat disappointing aspect, is that the breach was probably inevitable.
Encryption Not Present
While OPM Director Katherine Archuleta had noted the need for an upgrade in the technology and implementation of encryption on all the data 18 months prior, the need was dismissed due to the age of the networks. During testimony today with the House Oversight and Government Reform Committee, she said “It is not feasible to implement on networks that are too old.”
Contractors Credentials
On the other side, would encryption had helped as the breach all started with compromised contractors credentials? Dr. Andy Ozment, assistant secretary, Office of Cybersecurity and Communications stated during the same hearing that encryption would “not have helped in this case” as the attackers would have had the data encrypted once they accessed the machine.
Previously Breached
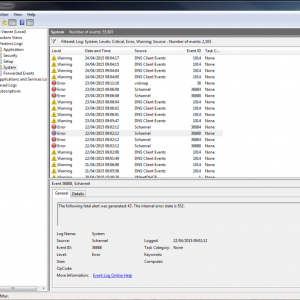
In July of 2014, the OPM had a breach of its networks, apparently with the breach being traced back to China. OPM downplayed the breach stating that no personal data was stolen but provided credit monitoring to employees. Following this breach, the Office of the Inspector General completed an audit of the whole department, finding significant failures in the security layers. The full investigation also found that there was no inventory of the endpoints, devices, databases, and investigators were not able to see if OPM was scanning for breach and vulnerabilities.
Two-Factor Authentication
During the same audit “We believe that the volume and sensitivity of OPM systems that are operating without an active Authorization represents a material weakness in the internal control structure of the agency’s IT security program,” the report concluded. In a day and age when two-factor has become a standard recommendation from the local IT friend to even the CIO of the US Department of Energy (http://energy.gov/cio/two-factor-authentication), this is one of the biggest failures within the OPM’s security layer. Lacking a physical CAC card or even phone authentication for login into the local machines and thus into the network could have saved the data from falling into the wrong hands.
These are just four of the issues leading up to this breach, areas often and exhaustively preached by security companies and professionals worldwide as the biggest and most vulnerable areas of attack. Beyond this, the audit itself not only highlighted the areas in need of immense improvement and increased security, but essentially laid the groundwork for the hackers, exposing all the weaknesses that have since been exploited, resulting in this breach.
For the full Inspector General report cited above from 2014, please click here: https://www.opm.gov/our-inspector-general/reports/2014/federal-information-security-management-act-audit-fy-2014-4a-ci-00-14-016.pdf











 Released: Webroot’s 2015 Threat Brief
Released: Webroot’s 2015 Threat Brief