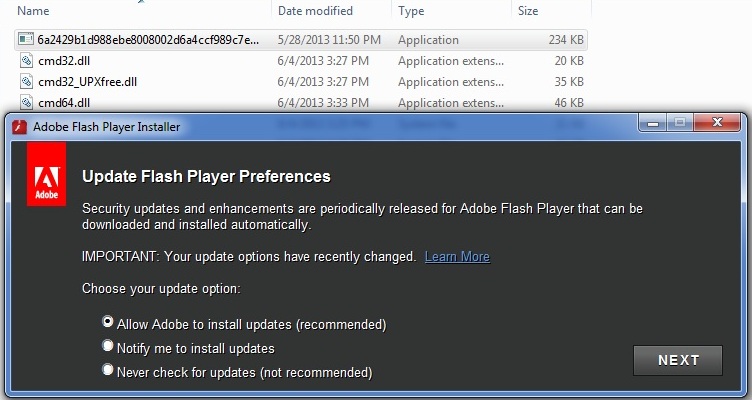
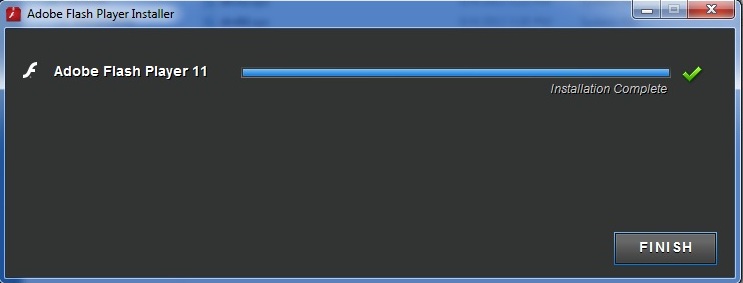
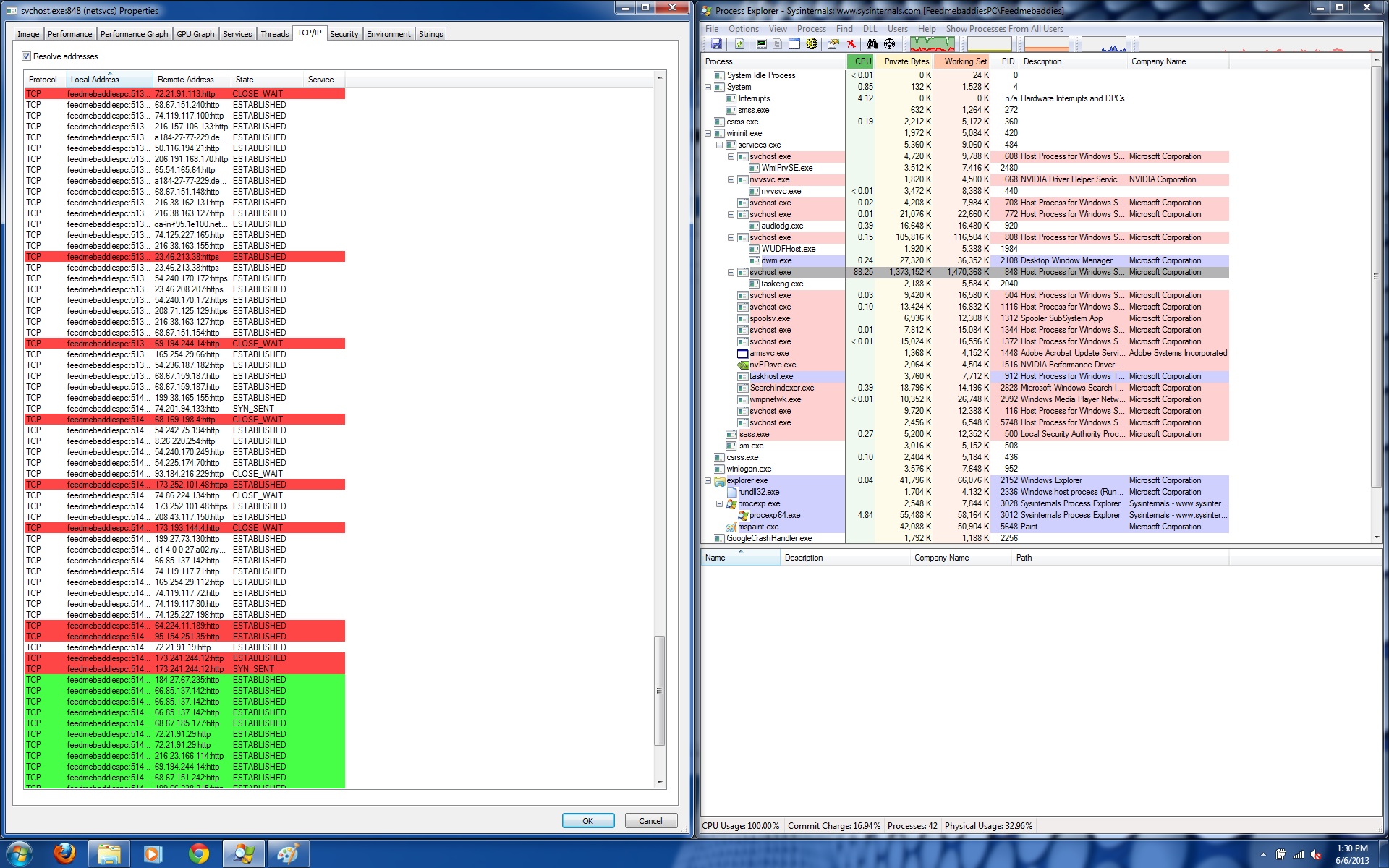
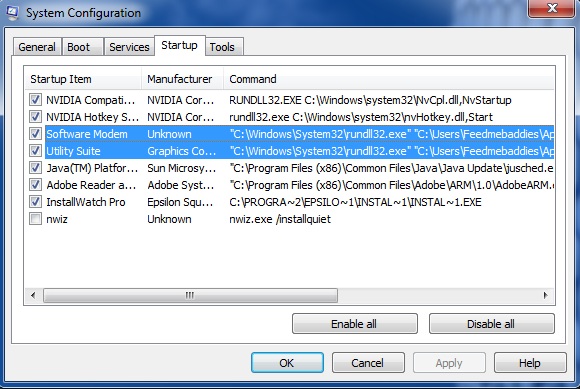
We’ve just intercepted yet another campaign serving deceptive ads, this time targeting German-speaking users into downloading and installing the privacy-invading ‘FLV Player’ Potentially Unwanted Application (PUA), part of Somoto’s pay-per-install network.
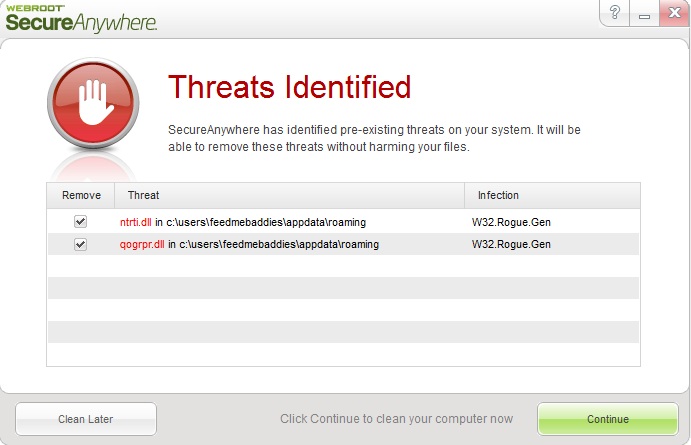
More details: