American Airlines customers, watch where you click! Cybercriminals are currently spamvertising millions of emails impersonating the company in an attempt to trick end and corporate users into clicking on the malicious links found in the spamvertised email.
Upon execution, the campaign redirects users to a Black Hole exploit kit landing URL, where client-side exploits are served against outdated third-party software and browser plugins.
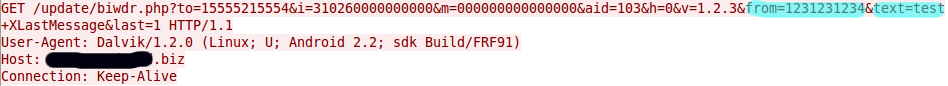
More details: