Everyone knows that there’s no such thing as free lunch. The same goes for freely distributed pirated content online.
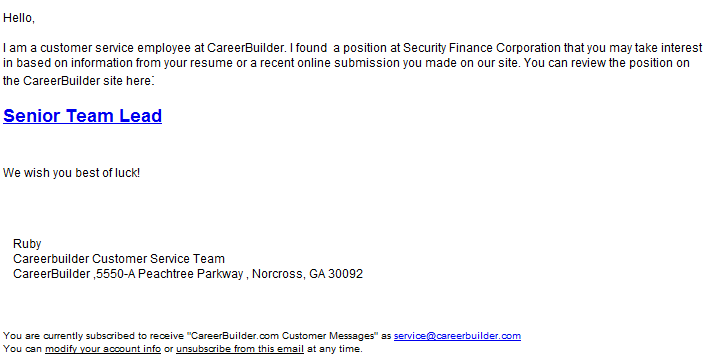
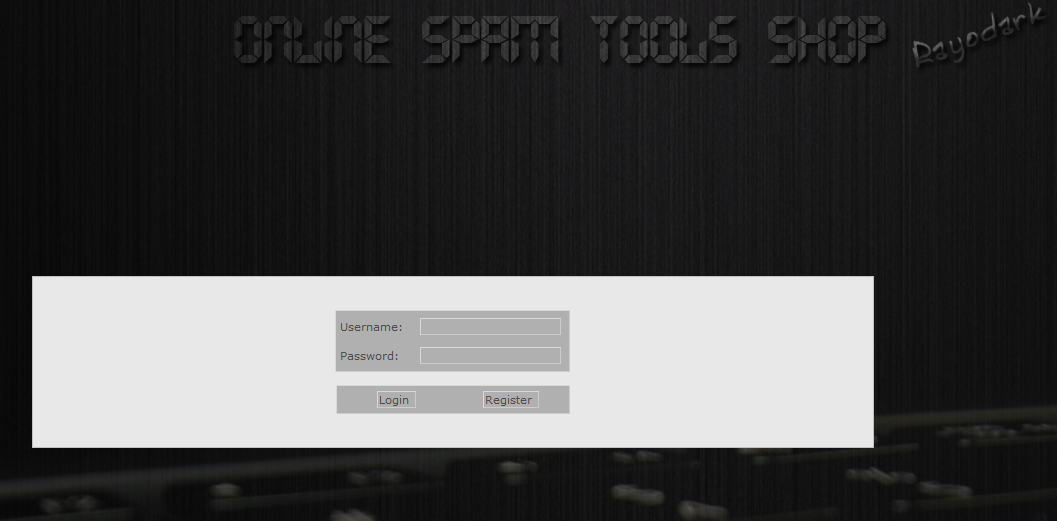
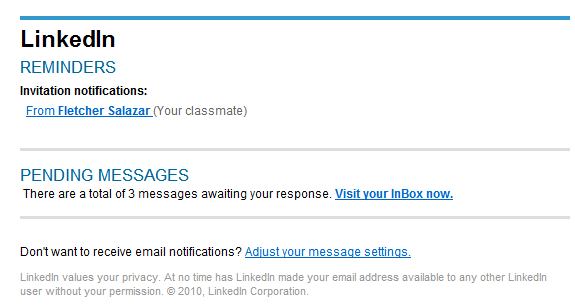
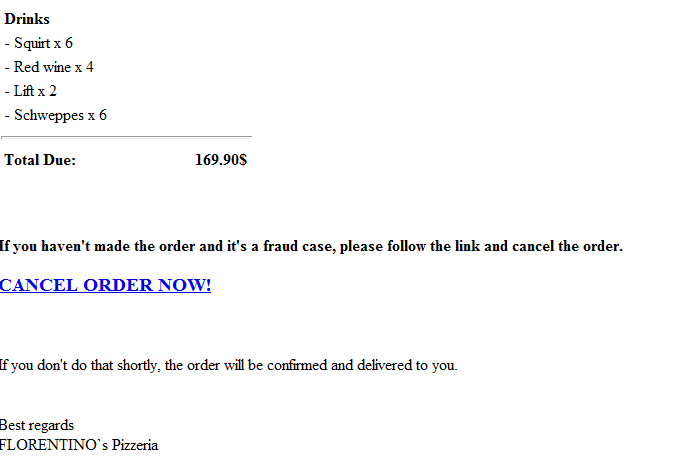
Recently, Webroot decided to sample malicious activity within some of the most popular Eastern European torrent trackers, based in Bulgaria, Ukraine, and Romania for starters. The results? Countless backdoored key generators and cracks for popular games and software, and most interestingly, monetization of the huge traffic by delivering pop-ups promoting the ubiquitous W32/Casonline adware, which in case you remember was recently spamvertised to millions of end and corporate users.
More details: