by Nathan Collier
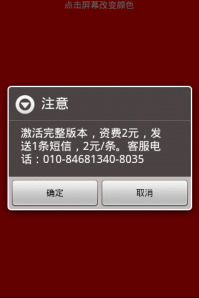
Recently we found new apps in alternative Chinese markets that we are considering a Potentially Unwanted Application (PUA). We are calling these apps Android.PUA.SMS.QuickPay. Lets look at a sample of this app. The sample we will look at is an app called “Screen Detection” which is an app that helps find dead pixels on your screen by displaying the colors red, green, blue, black, and white making it easy to see the dead pixel in contrast to these colors. Pretty simple app. Within a few seconds of opening the app this message pops up:
“Activate the full version, charges 2 Yuan, sending an SMS, 2 /. Customer Service Phone :010 -84681340-8035”
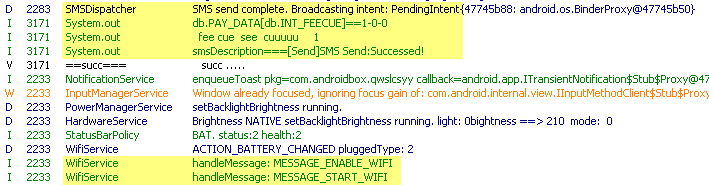
This app has limited functionality before requesting a premium SMS be sent for the full version, and that limited functionality only lasts a few seconds. If you do not agree to sending the premium SMS the app will just keep asking you to activate the full version whenever you click. Once you agree to the message it turns on your Wifi if not already on (Okay, that’s a little fishy), and sends a premium text message. After that the app works. Two Yuan is about 32 US cents, so people may just pay the small fee instead of spending the time to find a free version; which with a simple app that only shows four different colors as it’s functionality you would think there is something out there in the Chinese android market that will do the same for free.
It may not seem like much, but two Yuan at a time these guys are making a fortune off of apps that should be free. This is only one sample, there are several more very simple apps that we found that do various things, but all ask for a payment for it to function. Although there are legitimate Android Box apps out there, these apps are different in that they have very limited functionality, are signed by a different developer, and exploits simple apps that should be free by requesting payment for full versions before you even have a chance to see what it does.
Remember to always download from apps from a trusted source and be weary of messages asking to pay money for the full version so quick on the draw.