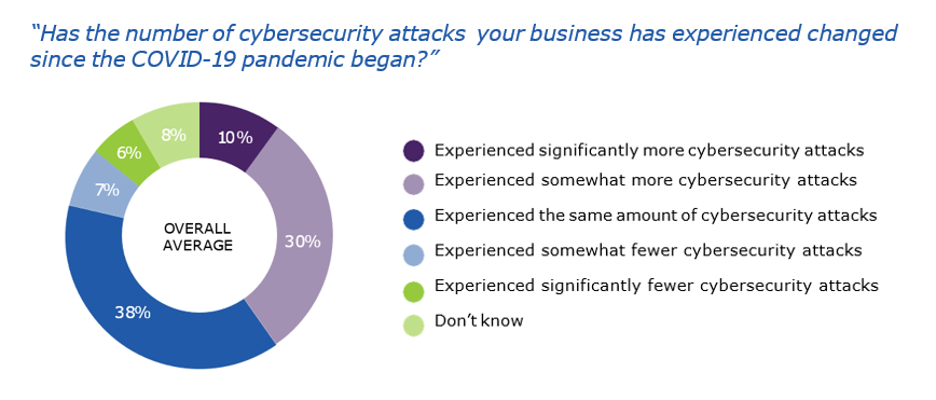
Whether you’re shopping for the latest tech gadgets or checking your work email, your online presence is susceptible to malicious threats. No industry or sector is immune. Even in the early days of 2022, a hospital in Jackson, Florida, experienced a ransomware attack that left medical professionals struggling to access patient records. Attacks like this not only have implications for patient care, but they also serve as a stark reminder of ongoing privacy issues in the online realm. As consumers and businesses are becoming increasingly more concerned about their data privacy, understanding how to protect that information becomes vital.
This week, the global community is rallying together to raise awareness about online privacy through Data Privacy Week.
What is Data Privacy Week?
Data Privacy Week began as a day of awareness in the United States, Canada and Europe and to commemorate the signing of Convention 108, the first internationally binding agreement addressing privacy and data protection. This year, the initiative has expanded to a week-long effort to generate awareness.
As data privacy and security implications become important for both businesses and individuals, there are a series of steps everyone can take:
- Adopt privacy mindfulness. Whether it’s for your home or your business, ensure you take privacy into account when you agree to the terms and conditions of items available for download from the internet or when you create a program that may expose your employees to online risk.
- Educate yourself. Avoid common attempts to compromise your information and identity by investing in security awareness training. Participate in simulated modules to test your knowledge and learn what traps to avoid.
- Back up your precious files. Not ready to part with your personal information? Make sure it’s backed up. That way, if you experience accidental or malicious data loss, your information is secure and accessible.
- Use antivirus software. Ensure online activities like shopping and browsing are secure by investing in a reliable antivirus. Adhere to updates and always renew your subscription to avoid a lapse in protection.
- Partner with a reliable provider. Some providers offer free protection and backup solutions, but can you really trust them? Always do your research and select a reputable provider to keep your devices and data safe.
From the rise of ransomware as a service (RaaS) to the use of malware to disrupt the political landscape, security, privacy and governance remain at a crossroads. With no signs of a resolution apparent, it’s important for everyone to take stock of their security stack.
One reliable approach is to adopt cyber resilience. Cyber resilience is a multi-layered, defense in depth strategy to ensure continuous access to your personal and business data no matter what happens. Establishing cyber resilience begins by assessing your current defense approach and employing the tools and know-how to remain protected and prepared for unknown threats. Whether it’s taking the time to educate your staff, upgrading your antivirus solution or investing in a reliable backup provider, make cyber resilience a priority.
This Data Privacy Week, let’s move beyond just becoming more aware of bad actors. Let’s take action to protect our data and our privacy.