Fake UPS Document Installs Fake Microsoft Patch Payload
![]() As if we didn’t have enough to deal with this week — after a Microsoft patch Tuesday that brought with it a boatload of security updates for Windows, Office, Silverlight, Visual Studio, and other programs — some enterprising malware distributor is emailing around bogus tracking number malware dressed up in the icon of a PDF document, and that malware is downloading payloads named after the updaters that Windows Update retrieves during an update.
As if we didn’t have enough to deal with this week — after a Microsoft patch Tuesday that brought with it a boatload of security updates for Windows, Office, Silverlight, Visual Studio, and other programs — some enterprising malware distributor is emailing around bogus tracking number malware dressed up in the icon of a PDF document, and that malware is downloading payloads named after the updaters that Windows Update retrieves during an update.
The malware arrived into one of our spam collection points with an attachment named UPS_document.zip. Way to be original there, criminals. Inside the Zip file was an executable downloader named UPS_Document.exe. Upon execution, it retrieves at least three payloads, including a copy of SpyEye (a password stealing Trojan), a tiny agent sending profiling information about the infected system, and a fraudulent “rogue system utility” called (on my XP testbed) Windows XP Restore.
The rogue takes on much of the appearance of a previous Rogue of the Week, named Windows Recovery. In fact, Windows XP Restore looks to be a very slightly modified duplicate of that software. If you’ve been hit with either rogue, there are some cool free tools for you to download that will repair some of the damage; Read on for details.
Android ‘Angry Birds’ Malware Contains Bot-like Code
![]() Most of yesterday, Threat Research Analyst Armando Orozco and I took a closer look at a piece of malware discovered by a university security researcher, Xuxian Jiang of North Carolina State. The malicious code, which the malware creator named Plankton, is embedded into a number of apps that were briefly posted to Google’s Android Market earlier this week, then rapidly pulled down after the researchers informed Google of their initial findings.
Most of yesterday, Threat Research Analyst Armando Orozco and I took a closer look at a piece of malware discovered by a university security researcher, Xuxian Jiang of North Carolina State. The malicious code, which the malware creator named Plankton, is embedded into a number of apps that were briefly posted to Google’s Android Market earlier this week, then rapidly pulled down after the researchers informed Google of their initial findings.
The Plankton code appears in a number of applications that were all focused on the popular game series Angry Birds. Some of the samples we looked at came as Android apps with names like Angry Birds Rio Unlocker v1.0, Angry Birds Multi User v1.00 or Angry Birds Cheater Trainer Helper V2.0.
When executed, the program displays the following text on the screen:
Welcome!
Simply click on the button below to unlock ALL levels in Angry Birds Rio. This will not delete your scores but might change the number of pineapples and bananas you have
None of the programs function as advertised. Instead, the malicious apps install additional code into the Android device into which they’re installed. These additional functions provide remote access and control of the Android device to, presumably, the distributor of the malicious apps, whose identity remains unknown at this time.
Malware Load Points Raise the Complexity Bar
 When malware ends up on an infected machine, one of the first things it will do is to ensure that it will start up again after the victim reboots their computer. For a criminal it makes sense. After all, what good is malware that stops working after a reboot?
When malware ends up on an infected machine, one of the first things it will do is to ensure that it will start up again after the victim reboots their computer. For a criminal it makes sense. After all, what good is malware that stops working after a reboot?
In Windows, there are tons of ways for malware to accomplish this small but critical task, most of which involve the Registry. Technical folks call the Registry keys that are used for this purpose load points or auto-start locations. There’s even a pretty good free app from Microsoft that will show you everything configured to start itself up using any of these load points.
The Threat Research Analysts here use their knowledge of load points to fine-tune definitions. Increasingly, we have to kill a load point then reboot the computer to remove a piece of malware. I wanted to call attention to some odd load point trends, where load points are stacked like dominoes, so the action that starts the execution process is several steps removed from the actual execution.
Why Put Security Into the Cloud?
This week, Webroot’s Thre@t Reply managed to steal some time with Ian Moyse, who knows a thing or two about the benefits of putting your computer and network security into the cloud, out where the threats are, rather than keeping your security inside your network or on individual computers.
[youtube=http://www.youtube.com/watch?v=JHAZxxWzBWk]
As always, feel free to submit your security question to @webroot, or by email to blog (at) webroot (dot) com, or in the comments below and we’ll get one of our threat researchers to answer it on an upcoming Thre@t Reply video. To see any of our other video replies to reader questions, visit the Webroot channels on YouTube or Vimeo.
MacProtector: Rogue of the Week
 This week, we turn our attention temporarily away from the never-ending stream of rogue security products on the Windows platform and take a closer look at the Mac OS analogue, MacProtector (aka Mac Security, Mac Defender, MacGuard, and–if history serves–soon to be many, many other names).
This week, we turn our attention temporarily away from the never-ending stream of rogue security products on the Windows platform and take a closer look at the Mac OS analogue, MacProtector (aka Mac Security, Mac Defender, MacGuard, and–if history serves–soon to be many, many other names).
There’s been a lot of press coverage of these rogues — including a video blog post by us — in the past few weeks, so we thought it was high time we took a deeper dive.
Even though Webroot doesn’t offer an automated removal solution for the Mac, there’s good news for most Mac users — with only a little bit of effort, it’s fairly rudimentary to simply delete the rogue .app and be done with it. In this case, the Activity Monitor (Apple’s GUI process monitor, located by default in the Utilities folder inside the Applications folder) is your best friend.
The program appears as a stub .mpkg installer, which means that the application that installs the program isn’t a container with the full program stuffed inside. The installer drops an app named avRunner.app into the Applications directory, then executes it.
Thre@t Reply: What’s a Firewall?
This week’s Thre@t Reply video features Threat Research Analyst Armando Orozco answering one of the most frequently asked questions we receive: What is a firewall, and how does it work? Well, the actual question wasn’t put quite so politely, but that’s the gist of it. Armando is the primary researcher working on the Mobile Security for Android product, but he also researches malware on Windows and Mac malware, as well.
[youtube=http://www.youtube.com/watch?v=p9cK7wkrZRo]
As always, feel free to submit your security question to @webroot, or by email to blog (at) webroot (dot) com, or in the comments below and we’ll get one of our threat researchers to answer it on an upcoming Thre@t Reply video. To see any of our other video replies to reader questions, visit the Webroot channels on YouTube or Vimeo.
Rogue of the Week: Windows Recovery
 Word from the AMR group last week was that there weren’t many changes from the previous week; Many of the same rogue antivirus previously reported in this blog continue to plague the Internet.
Word from the AMR group last week was that there weren’t many changes from the previous week; Many of the same rogue antivirus previously reported in this blog continue to plague the Internet.
This week I decided to focus on a rogue that’s recently become a problem. It goes by the name Windows Recovery, though it’s also been called Ultra Defragger or HDD Rescue by other AV vendors. Bottom line, it’s still a fraudulent program which relies on deception and trickery to convince a victim to fork over some cash for a “fix.” It’s just not a rogue antivirus; Call it a rogue system utility. Fortunately, the damage caused by this rogue is actually relatively straighforward to manually clean up.
The gist of this rogue’s deception comes down to trying to convince the victim that their computer hard drive has experienced some sort of major malfunction. To accomplish this, the rogue does a lot of sneaky stuff: For instance, it flags all files on the boot drive with the “hidden” attribute, then uses registry tricks to prevent Windows from displaying any hidden icons.
It also moves any shortcuts that point to programs (both from the start menu and on the desktop) into the Temp folder, effectively neutering the utility of the Start menu. (We have a free tool that can fix this.) And it uses the Registry to disable the user’s ability to open the Task Manager, changes the system wallpaper (and prevents you from changing that wallpaper), and hides the entire desktop from view. (And we have another free tool that can fix this, too.)
Chinese Android Trojan Texts Premium Numbers
By Andrew Brandt and Armando Orozco
![]() A Trojaned application that displays a cutesy image of a 2011 calendar on an Android device’s desktop comes with a nasty surprise: The app sends text messages to a premium service that charges the phone’s owner money.
A Trojaned application that displays a cutesy image of a 2011 calendar on an Android device’s desktop comes with a nasty surprise: The app sends text messages to a premium service that charges the phone’s owner money.
As first reported by the Taiwan-based AegisLab, a single developer, which went by the name zsone, published the apps to Google’s Android Market. All apps from that developer were pulled from the Market today by Google, though only some of them appeared to contain the undesirable code.
We took a closer look at one of the apps, called iCalendar, that AegisLab was kind enough to share with us, and it didn’t take long to find the malicious code inside. Fortunately for most non-Chinese Android users, the premium numbers reportedly only work within China. We’re still testing to make sure that’s correct.
Antivirus Center: Rogue of the Week
By Andrew Brandt and Brenden Vaughan
 Our Advanced Malware Removal group reported seeing several cases of a rogue called Antivirus Center this past week. The rogue isn’t new – we began seeing samples of it last year – but has re-emerged as a threat.
Our Advanced Malware Removal group reported seeing several cases of a rogue called Antivirus Center this past week. The rogue isn’t new – we began seeing samples of it last year – but has re-emerged as a threat.
This rogue is characterized by a close mimicry of some aspects of Microsoft’s free Windows Defender product, including the use of a program icon that looks like a castle, as well as some distinctive characteristics of its active file components. For example, the rogue’s application consistently uses a naming convention that looks like a long string of random alphanumeric characters, with a .dat extension, located in the Application Data folder of the “All Users” profile. As we’ve written before, no programs should run from the Application Data folder, so anything in that location is automatically suspect.
That said, it’s still going through the same stupid rogue AV motions, with all the exaggerated detections and predictably hilarious bad grammar we’ve come to expect. Read on for more details.
Thre@t Reply: “Online Shopping” | Part 2 of 2
In the second of a two-part series with Threat Research Analyst Grayson Milbourne, we answer a question about how to stay safe when shopping online. In the previous video, Grayson discussed how to identify a phishing page. In this episode, he continues his discussion by explaining how to tell whether the site you’re trying to purchase something from is operating safely and whether the site is able to protect your personal information when you click the “buy” button.
[vimeo 23488027]
As always, feel free to submit your security question to @webroot, or by email to blog (at) webroot (dot) com, or in the comments below and we’ll get one of our threat researchers to answer it on an upcoming Thre@t Reply video. To see any of our other video replies to reader questions, visit the Webroot channels on YouTube or Vimeo.
Thre@t Reply: “Online Shopping” | Part 1 of 2
In the latest Thre@t Reply video, Threat Research Analyst Grayson Milbourne answers a reader’s question about how to avoid being phished. The first step is to be able to identify whether you’re on the legitimate Web site you think you are, and if you’re not, what are the telltale signs that indicate you may be looking at a fake site designed solely to steal your user account and password information.
[youtube=http://www.youtube.com/watch?v=KklPP891bZ8]
To see the second half of the video, or any of our other video replies to reader questions, check out this post or visit the Webroot channels on YouTube or Vimeo.
ROTW: “Total Security” and Antivirus IS
By Brenden Vaughan and Andrew Brandt
 This week, our support and advanced malware removal (AMR) team did not have a lot of new data to report about rogue security products. The most commonly encountered infection continues to be one of the rogues we reported about last week.
This week, our support and advanced malware removal (AMR) team did not have a lot of new data to report about rogue security products. The most commonly encountered infection continues to be one of the rogues we reported about last week.
While we may refer to it as XP Total Security, it actually chooses one of a series of names at random, based on the operating system on the victim’s computer. Last week’s post contains a more comprehensive list of these names. As previously reported, you can remove the rogue by scanning (with our product, not theirs) while the computer is in Safe Mode.
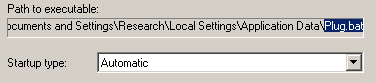
Its main executable has a random, three-character filename, and gets installed into a random, three-character folder inside the Application Data folder for the user who is currently logged on at the time of the infection. The rogue’s install location is:
%UserProfile%Local SettingsApplication Data<random><random>.exe
AMR reported seeing another rogue called Antivirus IS. While this is the first time they have mentioned it, Brenden believes it is a bit older, and has been floating around since late last year. Its logo is a blue shield with a single red diagonal stripe; its tagline, “Innovative protection for your PC,” is utter nonsense.
read more…











































