MDR for MSPs: Navigating EDR compatibility
When it comes to endpoint detection and response (EDR) compatibility within an MDR offering, managed service providers (MSPs) are weighing two key priorities: native EDR integration or the flexibility to support multiple solutions. According to a recent OpenText survey, opinions are split almost evenly. While 52% of MSPs view native compatibility as moderately or very important, 48% place greater value on flexibility.
This divide reflects the unique demands MSPs face. On one hand, native compatibility ensures a tight integration. On the other, the ability to work seamlessly with various EDR tools is critical for MSPs managing diverse client environments. For MSPs managing a mix of EDR tools across their customer base, this adaptability can be the difference between a smooth operation and a logistical headache.
In this blog, we’ll explore why flexibility in EDR compatibility is becoming a critical advantage for MSPs, how it ties into SIEM analysis, and actionable steps MSPs can take when evaluating MDR providers.
The case for native EDR compatibility
For MSPs and their customers, native EDR compatibility can offer advantages, especially when targeting newer companies that have not yet established an EDR infrastructure.
Here’s why:
- Streamlined integration:
Native EDR solutions typically provide seamless integration with the MDR platform, simplifying deployment and reducing setup time. This can be particularly appealing for MSPs looking to quickly onboard new customers who do not yet have an EDR solution in place. - Ease of use:
A native EDR integrated into the MDR platform provides MSPs with a consistent toolset, simplifying training for security teams and boosting overall efficiency and productivity.
However, for MSPs serving established SMBs that already have an EDR solution, the dynamic changes. An MDR capable of working with any EDR solution often delivers greater flexibility and value by complementing the SMBs’ existing setups.
When flexible EDR support wins
For MSPs, flexibility in EDR support provides a more strategic advantage. Managing security for well-established SMBs often means working within complex, diverse environments where a rigid “one-size-fits-all” approach simply doesn’t work. Here’s why flexible EDR support matters:
- Avoiding “rip and replace:”
Many MSP prospects already have an EDR solution in place that they are comfortable with and that meets their needs. Moving to a new, native EDR can impose a “rip and replace” burden, leading to disruptions and additional costs that may not be acceptable to MSPs. - Supporting diverse client environments:
MSPs often manage a variety of EDR products across their customer base. The ability to support multiple EDRs means MSPs can tailor their MDR services to fit the unique needs of each client without forcing them to change their existing security infrastructure. - Future-proofing:
Flexibility allows MSPs to stay ahead of the curve by ensuring their MDR solution can integrate with emerging EDR tools. This adaptability is crucial in a rapidly evolving cybersecurity landscape.
The MDR advantage—unifying EDR telemetry through SIEM
In a modern MDR solution, the SIEM platform serves as the backbone, ingesting security telemetry from across the customer environment. This includes feeds from firewalls, cloud services, identity providers, and—crucially—EDR solutions. The ability to support multiple EDR tools isn’t just about flexibility; it’s about leveraging the full power of SIEM to deliver more effective and unified threat detection and response.
- Centralized visibility:
By aggregating telemetry from diverse EDRs and other security tools into a single SIEM platform, MSPs gain a holistic view of the customer’s security posture. This comprehensive perspective enables faster identification of threats and vulnerabilities across the environment. - Improved threat detection:
SIEM platforms excel at correlating data from multiple sources. By ingesting streams from EDRs alongside other security feeds, the MDR solution enhances its ability to detect sophisticated threats with greater accuracy and precision, reducing false positives and improving response times. - Enhanced reporting and insights:
Unified telemetry within the SIEM allows MSPs to generate detailed, actionable reports that highlight trends, identify gaps, and demonstrate the value of their security services. These insights help MSPs guide their clients in making smarter security investments.
Actionable advice for MSPs
When choosing an MDR provider, MSPs should keep a few key factors in mind:
- EDR compatibility:
Ensure the MDR solution can seamlessly integrate with multiple EDR tools to support your diverse client environments. - SIEM integration:
Look for MDR solutions that can unify EDR telemetry through a centralized SIEM platform. - Scalability:
Choose an MDR provider that can scale with your business and offers the flexibility to adapt to evolving client needs and emerging cybersecurity challenges.
By prioritizing these factors, MSPs can provide their customers with advanced, efficient, and flexible security solutions that meet their unique needs.
6 ways to get the most from Data Privacy Week
Data Privacy Week (Jan. 27-31) is an excellent opportunity to reflect on the importance of protecting one of your most valuable assets: your personal information. Whether you’re browsing online as a consumer or running a business, data privacy is paramount in an environment where cyber threats can lurk around every corner.
In the spirit of Data Privacy Week, here are six ideas to help you protect yourself—and your data:
1. Understand your level of risk
Get acquainted with the phrase personally identifiable information. This includes any data that can be used to identify you, and it ranges from your name and address to more sensitive information like health and financial records. Here are some common examples:
- Health data: Information stored in a patient portal, online pharmacy, or health insurance website.
- Financial data: Details of your bank account, 401K fund, or IRA.
- Apps: Data collected by various applications you use. This information can range from your current location to previous purchasing habits.
- Social media: Information you share on platforms like Facebook, Twitter, and Instagram.
Knowing what kinds of personal data you have out there is the first step toward protecting it.
2. Learn the basics of data privacy self-defense
Protecting your data doesn’t have to be complicated. Here are some basic steps you can take to safeguard your privacy:
- Create secure passwords: Use a combination of letters, numbers, and special characters.
- Use multifactor identification: Add an extra layer of security to your accounts by using a password combined with a code sent to their phone or a fingerprint.
- Limit the number of cookies you accept: Be selective about which websites can track your activity.
- Beware of public Wi-Fi: Avoid accessing sensitive information on unsecured networks.
- Use a virtual private network, or VPN: Encrypt your internet connection to protect your data.
- Keep software up to date: Regular updates can protect you from security vulnerabilities.
3. Update your privacy settings
Take some time to review the privacy settings on the apps, devices, or websites you use most often. You might be surprised at what you find. The nonprofit National Cybersecurity Alliance has compiled a comprehensive list of popular sites’ privacy pages to get you started.
4. Arm yourself with antivirus protection
An effective antivirus program is essential for protecting your devices from malware and other threats. Look for features such as real-time scanning, automatic updates, and comprehensive protection against various types of malware. A product like Webroot offers a variety of antivirus solutions to keep your data safe. Webroot even offers a product selection tool that can help you find a solution tailored to your unique needs.
5. Find an encrypted data backup product
Backing up your data is crucial, but it’s equally important to ensure that those backups are secure. An encrypted data backup solution like Carbonite can protect your data from unauthorized access. Carbonite’s secure, always-on backup ensures that you won’t lose important, irreplaceable files due to accidental deletion or device malfunction.
6. Take in a movie
After all that hard work learning about data privacy, it’s time to reward yourself by doing something fun. Hop on the couch and watch a movie that delves into the topic. Here are some suggestions from the nonprofit group Educause:
- Terms and Conditions May Apply
- Citizen Four
- Code 2600
- Gattaca
- Minority Report
- 1984
- The Lives of Others
Managed Detection and Response: Key trends MSPs can’t afford to ignore
Cyber threats have never been more relentless, and businesses of all sizes are feeling the pressure. That’s where Managed Detection and Response (MDR) comes in—a lifeline for overburdened security teams navigating a threat landscape that’s growing more sophisticated by the day.
At its core, MDR is about augmenting, complementing, and upskilling internal security operations. It’s not just about tools—it’s about the expert humans behind those tools. MDR providers bring battle-tested security practitioners and capabilities with:
- Global visibility into threats and threat actors.
- Detection engineering expertise to uncover what others might miss.
- Strong threat hunting capabilities, working 24/7 to stay ahead of adversaries.
- Seamless integration across diverse security tools and logging ingestion from all corners of the organization’s infrastructure.
What started as an emerging offering has quickly grown into a cornerstone of modern cybersecurity strategy. Today, MDR is a thriving, competitive market. As Forrester notes: “MDR continues its ascent as an established, growing service with expansion, innovation, and an abundance of competition.”
But with maturity comes diversity of capabilities. For Managed Service Providers (MSPs), the challenge isn’t just keeping pace with the evolution of MDR—it’s about understanding what truly matters to their customers and delivering solutions that make an impact.
So, what exactly drives adoption, and which capabilities resonate most with MSPs in supporting their customers?
When it comes to endpoint detection and response (EDR) compatibility, MSPs are split almost evenly—52% of respondents rated native compatibility as moderately or very important, while 48% viewed it as less critical.
This near-even divide underscores an important trend: for many MSPs, the ability to support a range of EDR products is becoming just as crucial as having native EDR integration. Since many MSPs support a variety of EDR products across their customer base, the ability of an MDR solution to seamlessly integrate with multiple tools is often prioritized over a ‘one-size-fits-all’ approach.
For MSPs, this flexibility means they can:
- Tailor MDR services to fit the unique needs of each SMB client
- Avoid being locked into a single EDR vendor, maintaining freedom of choice
- Future-proof their offerings by ensuring compatibility with emerging EDR tools
Ultimately, while native EDR compatibility is still a desirable feature, MSPs are clear: an MDR solution’s real value lies in its versatility across diverse environments.
Cloud-based SIEM—The backbone of MDR
The survey revealed that 81% of respondents rated cloud-based SIEM (security information and event management) as important—whether slightly, moderately, or very—to be included in their MDR solution. This emphasizes the shift toward scalable, centralized solutions designed to enhance visibility and efficiency in managing threats across the full breadth of the MSP customer’s environment.
This highlights how cloud-based SIEMs empower MSPs to:
- Scale with ease as their SMB customers grow and threats evolve
- Stay connected with anywhere-accessible platforms
- Streamline operations by correlating andcentralizing threat management and response
For MSPs, incorporating cloud-based SIEM into their MDR offerings is no longer just a nice-to-have—it’s a competitive differentiator.
SOAR capabilities—Automation in MDR services takes center stage
In the world of Managed Detection and Response (MDR), security orchestration, automation, and response (SOAR) capabilities are rapidly becoming game-changers. For MSPs, the most valuable benefit from SOAR is clear: automation. When asked to identify the most valuable benefit from SOAR, the results revealed key insights:
- 30%—Automation of common tasks
Automating routine tasks significantly via workflows reduces the time spent on manual processes, leading to faster, more efficient incident resolution and freeing up teams to focus on higher-value activities. - 27%—Improved 24/7/365 protection
Enhanced after-hours response capabilities are critical for ensuring continuous protection, especially for SMBs that need around-the-clock vigilance. - 24%—Reduced alert fatigue
Prioritizing actionable alerts enables more accurate threat detection, helping MSPs build greater confidence in their systems and focus on the threats that truly matter.
This prioritization reflects a preference for efficiency and proactive threat management in MDR workflows. For MSPs, SOAR isn’t just a tool for automation—it’s a critical enabler of better resource management, helping them reduce the burden on their teams while offering enhanced, after-hours response to their customers.
The survey highlights key priorities for MSPs in the MDR landscape: flexibility, scalability, and efficiency. These qualities are critical for MSPs to meet the diverse and evolving needs of their SMB customers. For both MSPs and their customers, this focus translates into enhanced access to advanced threat detection and response capabilities, even when resources are constrained.
Up next—Deep dives into MDR’s most Important capabilities
This blog kicks off a four-part series exploring key insights from our OpenText MDR survey. Over the next few weeks, we’ll take a deeper look at the essential capabilities MSPs need to stay ahead of the curve and provide maximum value to their customers.
We’ll dive into:
- EDR compatibility: Why it’s crucial for your MDR offering—and when flexibility wins.
- Cloud-based SIEM: Why it’s a must have for MSPs in an MDR offering.
- SOAR benefits: How SOAR is elevating MDR services and improving efficiency.
Stay tuned for actionable insights that will help MSPs navigate the rapidly evolving world of MDR.
Why MSPs need proactive, 24/7 threat hunting
Cybercriminals are becoming increasingly sophisticated, agile, and fast. For managed service providers (MSPs) supporting small and medium-sized businesses (SMBs) with cybersecurity services, staying ahead of these adversaries is crucial. One of the most effective ways to do so is through round-the-clock threat hunting.
In this blog, we’ll explore why constant threat hunting is essential, the challenges MSPs face in providing it, and how OpenText MDR can help overcome these challenges while offering SMBs the protection they need.
The critical edge of 24/7 threat hunting
The pace of cyberattacks has never been faster. Modern threat actors are well-organized and highly skilled, using a range of attack methods to infiltrate systems, escalate privileges, and exfiltrate valuable data. The days of simplistic attacks that can be thwarted by basic defenses are long gone. Today’s adversaries employ advanced tactics like cross-domain attacks, use of stolen credentials, and sophisticated social engineering campaigns to infiltrate systems.
In addition to their increasing sophistication, adversaries are also incredibly fast. Breakout time, the window of time it takes for an attacker to gain initial access and the point at which they can move laterally to other critical systems, can be measured in minutes.
Given this reality, each minute lost in detection can give attackers the critical time they need to entrench themselves deeper within the organization’s environment. That’s why faster detection and response times are essential, delaying the response only increases the damage. That’s where 24/7 threat hunting becomes indispensable for MSPs looking to stay one step ahead of cybercriminals and protect their SMB customers.
Proactive threat hunting is the key to proactively identifying suspicious activity. It’s not just about waiting for an alert; it’s about actively searching for hidden threats in real-time. Threat hunting involves a combination of human expertise and advanced technologies that continuously analyze system data, identifying suspicious patterns or behaviors. By leveraging threat intelligence, threat hunters can spot emerging tactics, techniques, and procedures (TTPs) used by adversaries, often before they’re seen in traditional threat intelligence feeds.
The challenge of building 24/7 threat hunting
in-house
While 24/7 threat hunting is undeniably essential for protecting SMBs, building and delivering this capability in-house presents significant challenges for many MSPs. Providing round-the-clock monitoring and expert threat hunting requires not only advanced technology but also skilled cybersecurity professionals—resources that can be costly, complex to manage, and hard to scale. Here are some of the main challenges MSPs face when trying to provide 24/7 threat hunting:
- High financial investment
A fully staffed threat hunting team with a security operations center (SOC) requires significant financial investment. In-house teams need to be equipped with advanced security tools, threat intelligence, and continuous training. - Complexity of management
Threat hunting is not a simple task. It involves gathering and analyzing vast amounts of data from a range of endpoints, networks, and cloud to identify and track suspicious activity. With the growing number of tools and services available, managing these resources can quickly become overwhelming. MSPs may lack the expertise to tie everything together or the time to continuously monitor and analyze threat hunting data. - Resources
Maintaining 24/7 monitoring requires ongoing staffing, training, and operational management, which can stretch MSP resources thin. It’s hard to find skilled professionals who can perform threat hunting and respond to incidents in real-time. Cybersecurity talent is in high demand, and the shortage of skilled security experts makes it even more difficult for MSPs to maintain a robust in-house security operation.
Given these challenges, how can MSPs continue to provide best-in-class security services to their SMB customers? The answer lies in outsourcing to a fully managed solution that offers 24/7 threat hunting without the need for large internal teams or heavy financial investment.
That’s where OpenText MDR comes in.
OpenText MDR: The MSP solution for 24/7 threat hunting
For MSPs looking to provide round-the-clock threat hunting without the overhead of building an in-house solution, OpenText MDR offers a fully managed detection and response service that provides continuous monitoring, expert threat hunting, and rapid incident response—backed by a 24/7/365 SOC.
Here’s how OpenText MDR addresses the challenges MSPs face:
- Comprehensive, scalable SOC
OpenText MDR comes with 24/7/365 coverage staffed by experienced cybersecurity professionals. This means MSPs can offer their clients continuous monitoring and rapid incident response, without the need to invest in expensive infrastructure or manage the in-house complexities. - Expert threat hunting
At the heart of OpenText MDR’s threat hunting is our team of security experts who work around the clock, 24/7, to proactively hunt for emerging threats. Leveraging a combination of AI-driven analytics and real-time data analysis, our threat hunters can identify suspicious activity and potential risks long before they escalate into full-blown attacks. With a deep understanding of adversary tradecraft and advanced threat intelligence, our experts are equipped to detect sophisticated attack methods. This combination of human expertise and cutting-edge technology enables our team to spot attack patterns as they emerge. - Integrated SIEM & SOAR capabilities
OpenText MDR combines cloud based SIEM and SOAR capabilities in one platform. This integration simplifies threat detection, prioritization, containment, and enables remediation through automated and customizable workflows, enabling a swift and coordinated response when a threat arises. - Seamless integration with existing tools
OpenText MDR integrates with over 500 security tools and services, allowing MSPs to leverage their existing investments while enhancing their capabilities with advanced threat detection and response. This collaborative approach streamlines the process, making it easier for MSPs to implement and manage without starting from scratch. - Cost-effective solution
Instead of investing heavily in tools, infrastructure, and talent to build an in-house solution, MSPs can rely on OpenText MDR as either a fully managed or co-managed service. This enables MSPs to offer cutting-edge protection to their SMB clients at a fraction of the cost and complexity of running their own SOC.
By partnering with OpenText MDR, MSPs can provide their SMB customers with proactive, 24/7 threat hunting and comprehensive protection against sophisticated cyber threats. This simplifies security, allowing MSPs to stay competitive while ensuring their clients are safeguarded without the burden of building and managing an in-house threat hunting team.
Why MSPs must offer 24/7 cybersecurity protection and response — and how OpenText MDR can help
In today’s cyber threat landscape, good enough is no longer good enough. Cyberattacks don’t clock out at 5 PM, and neither can your security strategy. For Managed Service Providers (MSPs), offering customers 24/7 cybersecurity protection and response isn’t just a competitive advantage—it’s an essential service for business continuity, customer trust, and staying ahead of attackers.
But delivering round-the-clock security coverage is easier said than done. It requires the right tools, expertise, and scale. This is why partnering with OpenText for offering managed detection and response (MDR) can help MSPs deliver on this critical need without overburdening their resources.
The case for 24/7 cybersecurity protection
Let’s face it: the cyber threat landscape is relentless, and the game is changing fast. Small and medium-sized businesses (SMBs) make up the core customer base for MSPs and are often top targets for cyberattacks. Cybercriminals see SMBs as easier to exploit—with fewer resources for advanced defenses and treasure troves of valuable data.
But what makes the modern threat landscape even more dangerous is the speed and sophistication with which cybercriminals operate. Attackers are no longer lone actors poking at vulnerabilities. They are part of well-funded by rogue nations, highly organized operations using advanced techniques, automation, and artificial intelligence to breach systems faster than ever.
- The numbers don’t lie: SMBs are the victims of 43% of cyberattacks. And many of these attacks happen outside of business hours.
- Cybercrime costs are skyrocketing: Global cybercrime damages are expected to hit $10.5 trillion annually by 2025, and businesses without adequate security measures face steep financial and reputational losses.
- Compliance mandates are tightening: Regulations like GDPR, CCPA, and PCI DSS mean SMBs are under growing pressure to protect their sensitive data 24/7.
For MSPs, this means your customers need more than basic firewalls and endpoint protection. They need real-time monitoring, proactive threat hunting, and rapid incident response—all delivered 24/7. Anything less, and you risk leaving customers vulnerable to costly breaches.
The challenge for MSPs: Scaling 24/7 coverage
For MSPs, managing a large number of customers, the question becomes: How do you respond in real-time to stop these lightning-fast threats before they cause irreparable damage? Providing 24/7 cybersecurity protection is no easy task for MSPs. Building an in-house security operations center (SOC) to handle threats around the clock is both costly and resource-intensive.
Some common challenges include:
- Talent shortages: The cybersecurity industry faces a well-documented skills gap, making it hard for MSPs to find and keep experienced analysts. This challenge is so widespread that 43% of MSPs cite it as their biggest obstacle to delivering security services.
- High costs: The expense of creating an in-house SOC can be astronomical, often reaching millions. In fact, 33% of MSPs identify the overwhelming cost of needing numerous cybersecurity tools as a major barrier to offering security services.
- Evolving threats: Cybercriminals are constantly adapting and refining their attack strategies, making it essential for MSPs to stay ahead. This ongoing evolution demands continuous investment in both training for an MSP’s security team and the latest technologies to effectively detect and mitigate new types of threats.
This is where OpenText MDR comes in, empowering MSPs to deliver enterprise-grade protection without the heavy lifting of building your own in-house SOC.
Why MSPs should partner with OpenText MDR
OpenText MDR combines cutting-edge technology, human expertise, and 24/7 monitoring to help MSPs meet their customers’ growing cybersecurity demands. Here’s why OpenText MDR is the ideal solution:
- 24/7/365 threat monitoring and response
OpenText MDR provides constant vigilance, ensuring your customers are protected day and night. With advanced threat detection and remediation powered by SIEM and SOAR technology, it quickly spots and shuts down threats before they can do any damage. - Access to cybersecurity experts
You don’t need to recruit, train, or retain a team of highly skilled security analysts. OpenText MDR’s team of experts, including threat hunters, incident responders, and forensic analysts, acts as an extension of your team, empowering you to provide your customers with a proactive defense without the burden of recruiting an in-house team. - Scalability without complexity
As your customer base grows, OpenText’s Secure Cloud Platform scales effortlessly to meet demand. OpenText MDR simplifies security management with automation that processes vast amounts of data quickly and integrates seamlessly with over 500 tools and services. Its lightweight agent ensures effortless deployment across multiple environments, providing end-to-end data visibility in a single dashboard, while leveraging existing investments and guided by expert human analysts - Proven threat intelligence
Leverage OpenText’s global network and AI-driven threat intelligence and over 35 different threat intel feeds to stay ahead of emerging attack vectors. With automated and customizable workflows, continuous threat prioritization, containment, and remediation, you gain a proactive and collaborative approach to securing endpoints, networks, and cloud—reducing the likelihood of breaches and minimizing downtime.
Why MSPs can’t afford to wait
In a world where attackers can compromise a network in under an hour, every second counts. Without the ability to detect, analyze, and respond to security threats in real time, your customers face serious risks:
- Downtime from a successful attack, leading to lost revenue.
- Loss of sensitive data, with potential regulatory fines to follow.
- Reputational damage that’s hard to repair.
MSPs that partner with OpenText MDR gain the speed, expertise, and oversight needed to combat these threats head-on. By combining advanced technology with human expertise, OpenText MDR delivers the constant vigilance your customers need to stay secure in the face of ever-evolving cyber threats.
Let’s work together to give your customers the 24/7 protection they deserve.
Contact us today to learn more.
6 reasons why SMBs love OpenText MDR
In today’s digital-first world, small and medium-sized businesses (SMBs) face cybersecurity challenges that grow more complex by the day. SMBs are prime targets for attackers hoping to gain a foothold inside any organization that doesn’t have extensive security measures. As threats increase, so does the need for comprehensive, reliable, and accessible protection.
This is where managed detection and response (MDR) services come in. MDR combines threat detection, investigation, and response, offering businesses the support from a team of security experts who monitor the environment 24/7 to identify and respond to threats. For many SMBs, MDR is an ideal solution because it provides a level of protection and expertise that would otherwise require building an in-house security operations center (SOC).
With OpenText MDR, SMBs get exactly this level of protection, backed by a trusted name in cybersecurity. Delivered through our extensive network of leading MSPs, OpenText MDR offers the power of an enterprise-grade SOC, helping SMBs fortify their defenses, protect their data, and stay operational no matter the time of day.
SMBs are turning to OpenText MDR for several key reasons that make a difference in their security approach:
1. 24/7/365 monitoring and threat response
Cyber threats don’t follow a 9-to-5 schedule—they’re more likely to strike after hours or on weekends, when in-house teams may be offline. That’s why around-the-clock protection is crucial.
Working together with your MSP, OpenText provides robust, continuous protection supported by a skilled team of security experts. This around-the-clock vigilance offers invaluable peace of mind, knowing that security professionals are actively monitoring and defending your infrastructure from evolving threats, day and night.
2. Fast incident response
In the face of a cyber-attack, every second matters, and a rapid response can mean the difference between a minor incident and a major disruption.
With dedicated analysts for investigation and escalation within 15 minutes, OpenText MDR collaborates seamlessly with your MSP to deliver rapid incident response within critical time frames. This swift action minimizes potential damage, safeguards business continuity, and helps companies avoid costly disruptions.
3. Meet regulatory compliance requirements
Compliance can be tough, especially for SMBs with limited resources. OpenText MDR makes it easier by helping businesses meet key standards like NIST, PCI, HIPAA, and SOC 2.
With built-in security controls, reporting, and documentation, OpenText helps protect customer data, reduce risks, and keep you clear of costly fines. Plus, it frees up your team to focus on running the business, knowing that OpenText MDR is supporting your compliance requirements.
4. Low total cost of ownership (TCO)
Building an in-house SOC requires a significant investment that goes beyond just the initial setup. The costs quickly add up when factoring in the specialized hardware, advanced software, and the need to recruit and retain highly skilled security professionals. For many SMBs, these expenses are simply out of reach, which makes it challenging to keep up with the level of protection needed to guard against sophisticated cyber threats.
OpenText MDR solves this by offering a fully managed or co-managed SOC-as-a-Service model through your MSP, which cuts down on costs by eliminating the need for an in-house infrastructure and dedicated security team. With OpenText MDR, businesses can optimize their security budget without sacrificing the level of protection that’s required to counteract today’s cyber threats.
5. Enhanced protection beyond endpoint security
SMBs are increasingly investing in endpoint security, which is a crucial first step. However, today’s sophisticated adversaries often bypass these initial defenses, making it critical to have more than endpoint security alone.
OpenText MDR enhances an organization’s existing endpoint protection by integrating AI-driven automation, SOAR workflows, and a turnkey cloud SIEM into the security environment. This enables active monitoring and protection across the attack surface, while automating threat response and accelerating remediation times. With OpenText MDR, businesses benefit from a comprehensive, streamlined security service that operates continuously, working smarter, faster, and more efficiently to safeguard against evolving threats.
6. Advanced threat intelligence and threat hunting
Cyber threats are constantly evolving, and OpenText MDR stays ahead with threat intelligence from over 35 sources worldwide. SMBs gain valuable insights into emerging threats and can protect their business with OpenText’s security experts conducting threat hunting to proactively identify and neutralize potential risks before they escalate. This intelligence-driven approach provides an essential security practice that gives businesses the edge to thwart sophisticated attacks.
Cyber-attacks can bring business operations to a grinding halt, leading to reputational damage and substantial financial loss. In this climate, having a trusted security partner like OpenText—a provider known for its reliable and innovative security solutions—is essential for businesses looking to stay secure, resilient, and prepared for whatever cyber threats may come their way.
Ready to protect your business with comprehensive, around-the-clock security?
Discover how OpenText MDR can safeguard your organization today.
Top 5 roadblocks for MSPs and how OpenText MDR clears the way
The managed service provider (MSP) industry is booming with opportunities. At the same time, MSPs face the challenge of balancing customer satisfaction with profitability, making strategic decisions more important than ever. For 35% of MSPs, building cyber resiliency for customers is a top strategic priority, but that goal often runs up against resource constraints and rising operational costs.[i] To stay competitive, MSPs are focusing on improving operational efficiency (35%) and keeping costs under control (33%).[ii]
One of the smartest ways to tackle these strategic goals is by partnering with OpenText to deliver managed detection and response (MDR) services. This partnership empowers MSPs to offer a cutting-edge, fully managed detection and response service, taking the weight off operational costs and simplifying the complexity of building and managing an in-house MDR solution.
Here are five ways OpenText MDR helps MSPs overcome their biggest challenges:
1. Filling the security staff resource and skills gap
Staffing can be a perpetual challenge for MSPs, particularly when it comes to hiring and retaining skilled cybersecurity professionals. With a global shortage of 4.8 million cybersecurity experts, this issue is only becoming more pressing. MSPs feel the strain in several key areas, including:
- Managing an overwhelming volume of alerts with a limited team
- Cultivating the advanced skills needed to thoroughly investigate and prioritize threats
- Attracting and retaining top security talent to close skills gaps and support business growth
OpenText MDR tackles this challenge for MSPs head-on by providing you with a fully managed or co-managed MDR partnership. With OpenText MDR, MSPs can access 24/7/365 security expertise and continuous threat monitoring without the cost or complexity of building an in-house SOC. This not only eases the pressure on your internal teams but ensures a high-level of security coverage for your customers at all times.
2. Streamlining alert management
Detecting advanced threats requires a sophisticated approach to monitoring a customer’s attack surface. This is where SIEMs come in—essential for correlating data and identifying threats. However, SIEMs can be complex to configure, manage, and tune, which can lead to a high volume of false positives. For MSPs with limited resources, this flood of irrelevant alerts can overwhelm teams and drain operational efficiency.
OpenText MDR solves this by leveraging advanced threat intelligence to correlate security logs and reduce false positives, all while managing the SIEM and monitoring alerts for you. By continuously prioritizing critical threats, our experts handle the complexity of alert management, allowing MSPs to focus on what matters most—securing their customers—without the burden of filtering through a flood of false alarms.
3. Accelerating incident response
With a flood of alerts constantly coming in and the need to pivot between multiple consoles to investigate, MSP security teams often struggle with slow, time-consuming incident response. The pressure to act quickly is high, as swift action is essential to prevent the disastrous outcomes of a breach. However, many teams find themselves bogged down, bouncing between disparate tools and struggling to identify and respond to threats in real-time.
OpenText MDR addresses this challenge with fast, proactive monitoring and continuous threat hunting to detect suspicious activity early. Our dedicated experts streamline incident response by quickly identifying threats and escalating them within 15 minutes, ensuring MSPs can act fast and minimize the impact of potential breaches.
4. Simplifying security management across complex environments
Managing a customer’s complex environment can be challenging for MSPs. With diverse security tools, large volumes of data, and multi-environment deployments, the complexity of managing each unique environment can overwhelm MSP teams, stretching resources thin and hindering effective security management. Delivering cybersecurity services that support your diverse customer environments requires a solution that integrates seamlessly and simplifies management without adding to the burden.
OpenText MDR makes it easy to support your customer environments by offering a fully integrated solution that seamlessly supports your MSP partner and tools ecosystem. With AI-driven automation, OpenText MDR processes vast amounts of data quickly, integrating effortlessly with over 500 tools and services. Its lightweight agent ensures easy deployment across multiple environments, providing end-to-end visibility through a single dashboard. This not only streamlines security management but also helps MSPs leverage their existing investments while benefiting from expert human analysts guiding the process.
5. Driving revenue growth without barriers to entry
For MSPs, staying competitive and standing out in your region requires offering innovative solutions that meet customer needs without the complexity and barriers often associated with new vendor partnerships. Having an MDR offering can be a key driver for growth, but the challenge lies in finding an MDR vendor that has both a cutting-edge solution and flexible licensing, without the constraints of long-term contracts or rigid terms.
OpenText MDR addresses this by offering a subscription-based model with no minimum contract, making it easy to integrate into your existing service offerings. MSPs can access additional services like penetration testing, vulnerability management, and custom incident response plans as needed, with simple, integrated billing through OpenText’s Secure Cloud Platform. This flexibility allows you to scale your MSPs cybersecurity services as your business grows.
Discover how OpenText MDR can empower your MSP to overcome challenges and drive growth.
Top 5 reasons MSPs choose OpenText MDR
It’s an exciting time to be a managed service provider (MSP). More than ever, small and medium businesses (SMBs) are looking to MSPs as trusted advisors to help safeguard them from today’s growing cyber threats. One of the services in high demand right now? Managed detection and response (MDR). When asked about their biggest growth drivers, MSPs cite addressing clients’ cybersecurity concerns and awareness as the top new-business drivers (54%).1
For MSPs, adding MDR to your lineup can create new revenue streams while enhancing the value you bring to your clients. By offering OpenText MDR to your MSP clients, you gain access to skilled security experts and advanced technology infrastructure—without the complexity and cost of building it all in-house.
Here’s why more MSPs are partnering with OpenText to power their MDR security services:
1. Seamless integration with your existing tools
One of the greatest advantages of choosing OpenText MDR is its compatibility with your existing tools. OpenText MDR easily integrates with over 500 third-party tools, using APIs so you can add MDR services to your offerings without disrupting your current technology stack.
This flexibility also extends to popular professional services automation (PSA) tools, allowing for smooth incident ticketing and vulnerability management within your established workflows. With OpenText MDR, you can confidently grow your service portfolio while keeping your partner ecosystem intact.
2. Grow your revenue with flexible, hassle-free licensing
With cybersecurity top of mind, MSPs are seeing a surge in demand for security services. OpenText MDR helps you capitalize on this opportunity with a subscription-based model designed to grow with you—risk-free.
There are no long-term contracts, hidden fees, or minimums—just the freedom to scale your MDR services month-to-month, at your own pace, and based on your clients’ evolving needs. This flexibility lets you capture new revenue streams without overextending your resources.
3. Enhancing EDR with SIEM and SOAR capabilities
Effective MDR requires more than simply monitoring a client’s endpoint detection and response (EDR) solution—it demands a comprehensive view of the entire attack surface. OpenText MDR delivers this by enhancing your client’s EDR with advanced SIEM and SOAR capabilities.
The platform features real-time monitoring—integrated SIEM and SOAR capabilities—enabling rapid threat detection and automated response across your clients’ environments. This advanced approach safeguards your clients from evolving threats on all fronts—from endpoint to cloud.
4. Automation combined with human expertise
OpenText MDR brings together the speed of automation and the skill of experienced security analysts. This blend ensures that threats are detected quickly, incidents are prioritized with care, and responses are expertly managed around the clock, every day of the year. You get the best of both worlds—cutting-edge technology and dedicated human oversight that augments your MSP team.
With OpenText MDR, you can confidently offer clients a proactive, always-on defense against evolving threats—without the need to build up your own in-house security team.
5. Rapid incident response and proactive threat hunting
A speedy response is crucial to stopping adversaries in their tracks before they gain a foothold. MSPs can count on OpenText’s rapid incident response support, complete with dedicated escalation paths for high-priority threats, ensuring swift action when it matters most. You have the flexibility to choose whether you want the OpenText MDR team to completely manage threat response, or opt for co-managed support, where your team takes the lead with OpenText offering expert backup and resources.
OpenText MDR also delivers continuous, proactive threat hunting to identify and neutralize risks before they can affect client environments. This powerful combination of active threat hunting and fast response equips MSPs to provide clients with a robust, preemptive defense against emerging threats.
A speedy response is crucial to stopping adversaries in their tracks before they gain a foothold. MSPs can count on OpenText’s rapid incident response support, complete with dedicated escalation paths for high-priority threats, ensuring swift action when it matters most. You have the flexibility to choose whether you want the OpenText MDR team to completely manage threat response, or opt for co-managed support, where your team takes the lead with OpenText offering expert backup and resources.
OpenText MDR also delivers continuous, proactive threat hunting to identify and neutralize risks before they can affect client environments. This powerful combination of active threat hunting and fast response equips MSPs to provide clients with a robust, preemptive defense against emerging threats.
Stand out and succeed with OpenText MDR
By adding OpenText MDR to your portfolio, you can differentiate yourself in the market, offering SMBs a level of protection that goes above and beyond the competition. With 24x7x365 coverage, over 500 third-party integrations, SIEM and SOAR at no additional cost , and proven value, you’ll be able to deliver superior MDR service that not only meets but exceeds customer expectations.
Do you actually need a VPN? Your guide to staying safe online!
With the rise of online scams and privacy risks, virtual private networks (VPNs) are becoming more popular for day-to-day use. Or at least I feel like they are based on the number of ads I hear for them on my favorite podcasts.
So maybe you’ve heard of VPNs but aren’t actually sure what they are. Simply put, a VPN creates a safe, anonymous pathway for the data you send and receive over a Wi-Fi network, allowing you to browse anonymously and access content as if you were in a different location.
Maybe you’ve used VPNs as a remote worker to access resources and applications for your job, or as a student to connect to your university network. Do you really need a VPN for personal use? The short answer—absolutely! Keep reading for the long answer and for tips on choosing the right VPN.
How do VPNs work?
Essentially, VPNs create a secure tunnel for your data. The five core components of a VPN are:
- Encryption: The conversion of information into a coded format that can only be read by someone who has the decryption key. It ensures that data remains secure and private during transmission or storage.
- VPN servers: Usually located all over the world, VPN servers act as intermediaries between your device and the internet and maintain your privacy by masking your IP address and location.
- Kill switch: Blocks your device’s internet access if the VPN connection drops. This way, the VPN app makes sure you’re always protected.
- Split tunneling: Allows you to choose which internet traffic goes through the VPN (with encryption) and which goes directly to the internet.
- VPN protocols: Transmits your data according to protocols like OpenVPN, IKEv2, and WireGuard. Each cover different use cases like streaming or gaming or are required for certain types of devices.
Why use a VPN?
Maybe you already have other personal cybersecurity tools for personal user and think you don’t need a VPN. Consider the following and see if you still feel that way:
Privacy protection
Because a VPN creates a secure tunnel for your data, you don’t have to worry about bad actors peeping in on your activity and private information. This is especially important when using public Wi-Fi at coffee shops, airports, malls or hotels, where hackers can easily overcome public Wi-Fi security protocols to gain access to your device.
Antivirus augmentation
Even if you already have antivirus software, using a VPN enhances your personal cybersecurity.
Personal privacy:
- Antivirus software: Primarily protects your device from malware, viruses, and other malicious software.
- VPN: Encrypts your internet connection, hiding your online activities from ISPs, hackers, and even government surveillance. Keeps your browsing history and personal data private and anonymous.
Secure public Wi-Fi use:
- Antivirus software: Can detect and block malicious files or websites, but it doesn’t secure your internet connection.
- VPN: Protects your data on public Wi-Fi networks, which are often unsecured and a hotspot for hackers. A VPN encrypts your connection, making it much harder for anyone to intercept your data.
Accessing restricted content
I have a friend who loves British television but can’t always access it due to living in America. So she uses a VPN to set the United Kingdom as her virtual location and then watches all the BBC murder mysteries she wants.
This capability is extremely useful if you’re someone who travels a lot. For example, if you find yourself in a country with strict censorship laws, a VPN can help you access your usual content—even if it is restricted.
Which VPN should you choose?
Consider the following when researching VPNs:
- Connection speed
- Unlimited data and bandwidth
- Number and location of servers across the globe
- No-log policy*
- Security features and protocols
- Ease of use
- Brand reputation and customer support
While some VPNs may be free, they often come with limited performance, data caps, and lower security and log standards.
What steps should you take next?
Cybersecurity is only going to get more important as technology—and cyberthreats—advance. To protect your private, sensitive data, you’ll need all the tools at your disposal to keep out criminals. Add a VPN such as Webroot™ Secure VPN to your arsenal of cybersecurity tools to browse the internet safely and privately.
*A no-log policy means that the provider doesn’t keep any records of your online activities, ensuring your privacy and anonymity. This policy protects you from tracking, reduces the risk of data breaches, and prevents third-party access to your information. It also builds trust and gives you peace of mind, knowing your online activities are not being recorded or shared.
Nastiest Malware 2024
Steam the Webinar on demand HERE
As we look back on the cybersecurity landscape of 2024, it’s clear that the world of digital threats continues to evolve at an alarming pace in parallel with AI. This year has seen ransomware groups adapt and innovate, pushing the boundaries of their malicious capabilities and evasiveness from law enforcement. In our annual “Nastiest Malware” report, now in its sixth year, we’ve observed a steady increase in both the number and sophistication of malware attacks. The ransomware sector, in particular, has witnessed the emergence of “business models,” with ransomware-as-a-service (RaaS) dominating the scene. Elite ransomware authors have concluded that profit sharing and risk mitigation are key contributors to their consistent success and evasion of authorities.
The saga of LockBit in 2024 exemplifies the resilience and adaptability of these cybercriminal groups. Despite a major law enforcement operation in February, dubbed “Operation Cronos,” which saw the FBI and international partners seize LockBit’s infrastructure and obtain over 7,000 decryption keys, the group managed to resurface within days. This cat-and-mouse game between LockBit and law enforcement agencies has continued throughout the year, with the group’s leader even taunting the FBI, claiming that their efforts only make LockBit stronger. The LockBit story underscores a crucial point: while law enforcement operations can disrupt cybercriminal activities, they often fall short of delivering a knockout blow. These groups have become adept at rebuilding their infrastructure, rebranding when necessary, and continuing their operations with minimal downtime.
As we detail our analysis of the six most notorious ransomware and malware groups that have dominated headlines in 2024, it’s important to note that the threat landscape extends beyond just these actors. The rise of AI-driven phishing and social engineering, increased targeting of critical infrastructure, and the emergence of more sophisticated fileless malware are all trends that have shaped the cybersecurity battlefield this year.
In this report, we’ll explore how these groups have evolved, their most significant attacks, and the broader implications for cybersecurity. We’ll also provide updated survival tips for both businesses and individual users, reflecting the ever-changing nature of these threats.
Ransomware
Over the past decade, ransomware has established itself as the pinnacle of cybercriminal exploits. It is the most successful and lucrative avenue for monetizing a breach of a victim. Every year we see more and more data stolen and higher ransom demands dominating headlines. Each ransomware group on our Nastiest Malware list utilizes the double-extortion method where the data stolen is leveraged for leak potential on dark web leak sites. The impending damage to brand and reputation that comes with the public disclosure of a breach are massive threats to companies of any size. Not to mention the impending regulatory fines that come with the breach. This strategy has shown it’s resilience over the past few years since it became mainstream and it seems to be as robust as ever. Let’s take a look at what the payment numbers look like so far in 2024.
Source: Coveware
We’ve seen a drop-off from the highs last year – fueled by Cl0p ransomware group making over $100 Million in a few months in late 2023. But when we zoom out you can see that it will be going up over time. This time next year we anticipate the amounts to be higher than what they are now. Some of this will be fueled by inflation, some will be an increase in effectiveness in tactics, and some by the anticipated 2025 “bull run” price spike in crypto – the only payment method these criminals accept.
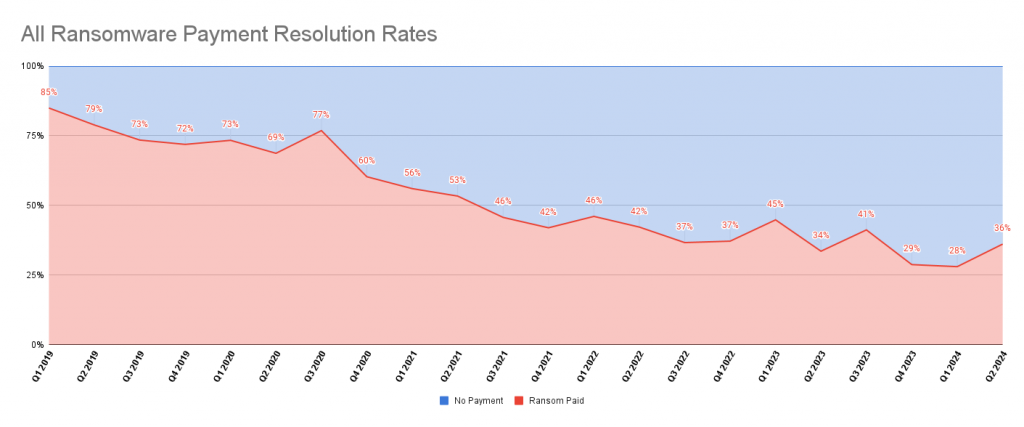
Looking at the payment resolution rates – meaning the percentage of people that end up paying the ransom, we can see a slight increase during this year. Zooming out the trend does indicate an overall decline which is good news and reflects that the industry is taking serious precautions in their security posture. We expect that this slight increase is only temporary and will continue the trend of decreasing for next year.
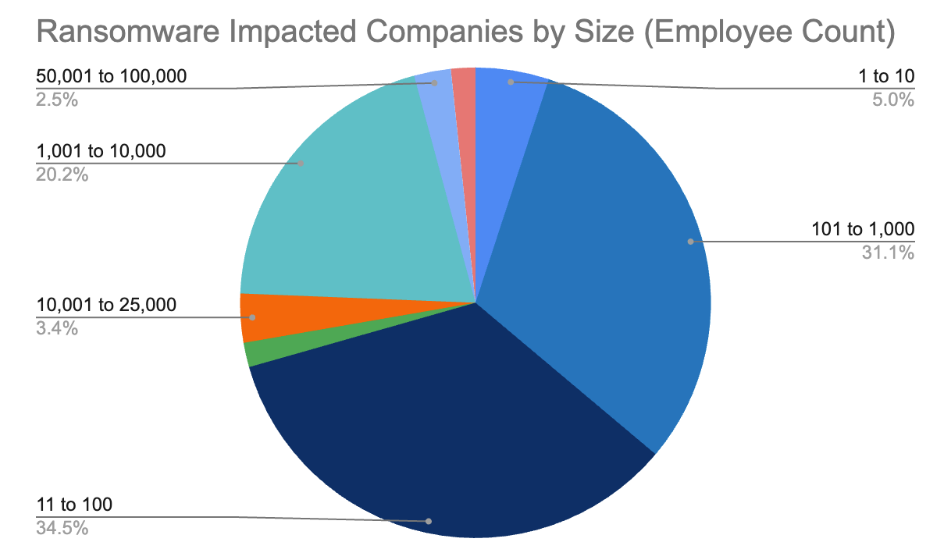
One nasty change this year is the increase of ransomware attacks on smaller sized businesses. The market share of ransomware attacks on business with under 100 employees is now almost 40%. While the media headlines of record breaking ransoms against fortune 500 companies will always take center stage, the small to mid market has always been the bread and butter for cybercriminals. The amount of effort and return on investment of time is too good for criminals not to be attracted to these easier and weaker targets. Now let’s take a look at this year’s Nastiest Malware.
LockBit: The Resilient Threat
One of the most notorious ransomware groups, LockBit, faced significant challenges and disruptions in 2024 due to coordinated international law enforcement efforts. The year began with “Operation Cronos,” a major strike against LockBit’s infrastructure in February. Led by the UK’s National Crime Agency (NCA) and involving agencies from multiple countries, including the FBI, this operation resulted in the seizure of LockBit’s leak sites and the exposure of information about nearly 200 affiliates. A pivotal moment came when the FBI obtained over 7,000 decryption keys, allowing victims to unlock their encrypted data for free. This dealt a severe blow to LockBit’s operations and credibility – remember that most of the success and money is from the affiliates that choose thier ransomware payload over another’s group so credibility and trust are paramount in this criminals scene.
Despite these setbacks, LockBit attempted to maintain its operations, quickly adapting by changing encryption methods and shifting its leak site strategy. However, law enforcement continued to apply pressure throughout the year. In May, authorities revealed the identity of LockBit’s alleged mastermind, Dmitry Yuryevich Khoroshev, and offered a $10 Million reward for information leading to his arrest. The culmination of these efforts came in October when law enforcement agencies announced additional arrests and disruptions. Four individuals connected to LockBit were arrested, including a major developer and two affiliates. Notably, Aleksandr Ryzhenkov, linked to both LockBit and the infamous Evil Corp group, was unmasked and sanctioned. These actions, part of the ongoing Operation Cronos, significantly impacted LockBit’s operations, leading to a noticeable decrease in their attack frequency and causing distrust within the cybercriminal community.
Despite LockBit’s attempts to maintain its fearsome reputation, including false claims of attacks, the group’s activities were impacted throughout 2024, marking a significant victory for global cybersecurity efforts. However, LockBit is still a major player in the RaaS scene and the leader and his affiliates are still making millions in ransoms. LockBit has proven its resilience in the face of law enforcement efforts, presenting the group’s adaptability and persistence. The leader has boasted that he loves the FBI and that they only make his group stronger, and he wants to hit one million businesses before retirement. This is a stark contrast from most ransomware groups when hit by law enforcement as they will quickly retire the brand and repivot to another. This RaaS has been on the Nastiest Malware for over three years maintaining its status as a top contender in the Ransomware scene in 2024.
Akira: The Healthcare Menace

The Akira ransomware group was first observed in March 2023 and immediately became one of the most formidable threats in the threat landscape. By January 2024, the group had impacted over 250 organizations and claimed approximately $42 million in ransomware proceeds. Akira’s rapid rise to the top was marked by its versatility and constant evolution of tactics. In 2024, Akira expanded its capabilities significantly. Initially focused on Windows systems, the group deployed a Linux variant targeting VMware ESXi virtual machines in April. Throughout the year, Akira demonstrated a pattern of swift adaptation to new vulnerabilities. They actively exploited several critical vulnerabilities, including SonicWall SonicOS, Cisco Adaptive Security Appliance (ASA), and FortiClientEMS software. These exploits allowed Akira to gain initial access, escalate privileges, and move laterally within compromised networks.
A notable shift in Akira’s tactics occurred in early 2024 when they appeared to sideline encryption tactics, focusing primarily on data exfiltration. However, by September 2024, there were indications of a potential return to previous tactics using Windows and Linux payloads written in C++. This adaptability was further evidenced in a June 2024 attack on a Latin American airline, where Akira operators exploited vulnerable services to deploy ransomware and exfiltrate data.
Akira’s victims spanned a wide range of sectors, with a particular focus on manufacturing, professional services, healthcare, and critical infrastructure. The group’s success was attributed to its constant evolution, sophisticated attack methods, and the employment of double-extortion tactics. As of 2024, Akira had solidified its position as one of the most prevalent and dangerous ransomware operations in the cybersecurity threat landscape.
RansomHub: The High-Profile Attacker

RansomHub emerged as a formidable new player in the ransomware landscape in February 2024, quickly establishing itself as one of the most prolific and dangerous ransomware groups. Operating on a RaaS model, RansomHub attracted high-profile affiliates from other prominent groups like BlackCat/ALPHV following their FBI takedown in December 2023. This is likely due to its attractive payment structure where affiliates receive up to 90% of the ransom – compared to around 30-50% with other groups.
By August 2024, RansomHub had breached at least 210 victims across various critical U.S. infrastructure sectors, including healthcare, government services, financial services, and critical manufacturing. Notable attacks included breaches of Planned Parenthood, the Rite Aid drugstore chain, Christie’s auction house, and Frontier Communications, with the latter resulting in the exposure of personal information of over 750,000 customers. RansomHub’s tactics evolved throughout the year, employing sophisticated methods such as exploiting various software vulnerabilities, using intermittent encryption to speed up attacks, and leveraging double extortion techniques. The group’s data leak site became a significant threat, with stolen data being published for 3-90 days if ransom demands were not met.
The attack on Planned Parenthood not only demonstrated RansomHub’s capability to breach highly sensitive networks but also highlighted their willingness to target organizations with high reputational risks. This sparked widespread concern and discussions on cybersecurity measures within nonprofit organizations. By October 2024, RansomHub had overtaken LockBit as the most prolific ransomware group in terms of claimed successful attacks, solidifying its position as a major threat in the cybersecurity landscape.
Dark Angels: The Whaling Experts

Dark Angels emerged as one of the most formidable ransomware threats in 2024, gaining notoriety for their highly targeted “big game hunting” approach and record-breaking ransom demands. The group, which has been active since 2022, made headlines in early 2024 when they reportedly received a staggering $75 million ransom payment from a Fortune 50 company. This payment would be nearly double the previous record of $40 million paid by CNA Financial in 2021.The group’s modus operandi involves targeting a small number of high-value organizations, often exfiltrating massive amounts of data (typically 10-100 terabytes for large businesses) before considering encryption. This strategy allows Dark Angels to maintain a low profile while maximizing their profits.
In 2024, they continued to evolve their tactics, switching from a Babuk-ESXi-based ransomware to a variant of Ragnar Locker. Notable attacks attributed to Dark Angels in 2024 included a breach of a high-profile media company, where they stole proprietary information and engaged in lengthy negotiations before the ransom was paid. The group’s data leak site, named “Dunghill Leak,” is used to pressure victims into paying, though the group often prefers to avoid public attention. Dark Angels’ success in 2024, particularly the record-breaking ransom payment, has raised concerns that their tactics may be emulated by other cybercriminal groups, potentially leading to an increase in highly targeted, high-value ransomware attacks across various sectors.
RedLine: The Credential Thief
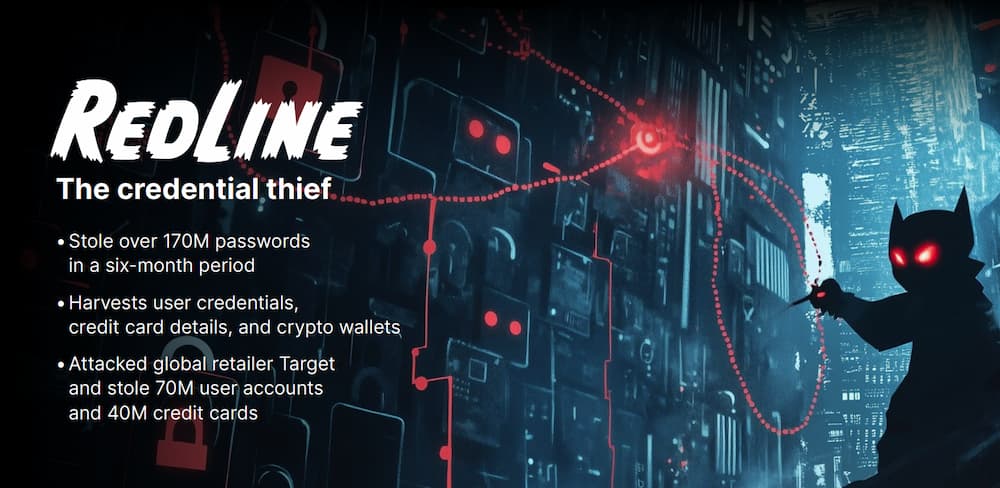
Not all of our Nastiest Malware are ransomware groups and RedLine Stealer has become one of the most prominent threats in 2024, particularly due to its capability to steal credentials and sensitive data across a wide array of sectors. Throughout 2024, RedLine demonstrated its effectiveness by stealing over 170 million passwords in just a six-month period, highlighting its massive impact. The malware’s capabilities expanded to include stealing not only passwords but also credit card details, cryptocurrency wallets, and browser data. Its adaptability and frequent updates allowed it to evade many security measures, making it a persistent threat across various sectors.
RedLine’s distribution methods remained diverse, with phishing emails and malicious websites being the primary vectors. The malware’s operators continued to refine their tactics, often disguising RedLine as legitimate software updates or enticing downloads. This approach allowed them to bypass traditional security measures and infect a large number of systems. The impact of RedLine extended beyond individual users to affect major corporations and critical infrastructure. Several high-profile breaches attributed to RedLine in 2024 resulted in significant financial losses and reputational damage for the affected organizations.
Breaking news!
In late October 2024 – RedLine suffered a takedown from a coordinated international law enforcement operation dubbed “Operation Magnus.” Led by the Dutch National Police and supported by agencies including the FBI, UK’s National Crime Agency, the operation successfully disrupted RedLine’s infrastructure and operations. The authorities gained full access to RedLine’s servers, obtaining crucial data including usernames, passwords, IP addresses, and even the source code of the malware. This breakthrough allowed law enforcement to retrieve a database of thousands of RedLine clients, paving the way for further investigations and potential legal actions against cybercriminals who used the malware. The U.S. Department of Justice charged Maxim Rudometov, a Russian national, as the suspected developer and leader of the RedLine malware operation. If convicted, Rudometov faces up to 35 years in prison on charges including access device fraud, conspiracy to commit computer intrusion, and money laundering.
Only time will tell if this seizure of assets is enough to shutdown the operations of RedLine and prevent them from bouncing back like we’ve seen time and time again from other resilient groups on this list.
Play Ransomware: The Versatile Threat

Play ransomware continued to be a significant threat in the cybersecurity landscape throughout 2024. The group, which first appeared in 2022, maintained its position as one of the most active ransomware operations, consistently ranking among the top threat actors. In 2024 a notable shift occurred when the group transitioned from its previous double-extortion tactics to specifically targeting ESXi environments. This change in focus allowed Play to exploit vulnerabilities in virtual machine infrastructures, increasing the impact of their attacks.
A significant attack attributed to Play Ransomware targeted a major utility provider, resulting in widespread service disruptions and raising concerns about critical infrastructure vulnerabilities. The attack began with the exploitation of unpatched FortiOS vulnerabilities in the company’s VPN infrastructure, allowing initial access to the network. From there, the attackers leveraged exposed RDP services to move laterally within the network, eventually gaining the access needed to deploy their ransomware payload.
The group’s use of intermittent encryption continued to be a defining characteristic, allowing them to evade many endpoint security solutions while still rendering files inaccessible to victims. Play’s attacks were particularly damaging in the IT services sector, suggesting a strategic focus on organizations that could lead to supply chain impacts.

AI-Driven Phishing and Social Engineering:
- The use of AI and machine learning in crafting phishing emails has made these lures more convincing and harder to detect. Cybercriminals are leveraging AI to personalize attacks, increasing their success rates
Targeting of Critical Infrastructure:
- There has been a noticeable increase in attacks targeting critical infrastructure, including utilities and healthcare sectors, raising concerns about national security and public safety
Fileless Malware:
- Fileless attacks aren’t new, and neither is bypassing security protections but there has been an increase in harder to detect kill chains, more sophisticated attacks, more complex persistence, that are more effective at bypassing security than ever.
New Malware Language:
- Malware written in Golang continues to trend in both scale and complexity
Businesses:
- Lock down Remote Desktop Protocols (RDP) – this infiltration tactic has been around for a while, but it’s still one of the top infection vectors!
- Enhance Employee Training: Go beyond basic awareness. Implement regular, interactive cybersecurity simulations and scenario-based training.
- PATCH OR DIE!
- Implement a Multi-layered security and defense in depth posture.
- Adopt a Comprehensive Backup Strategy: Implement the 3-2-1 backup rule with immutable backups to protect against ransomware attacks.
- Develop and Test Incident Response Plans: Create, regularly update, and practice cybersecurity incident response plans.
Individual Users:
- Use Password Managers: Employ a reputable password manager to create and store strong, unique passwords for all accounts – consider passphrases.
- Enable Multi-Factor Authentication (MFA): Activate MFA on all accounts that offer it, preferably using authenticator apps or hardware keys.
- Keep Software Updated: Enable automatic updates for your operating system, applications, and security software.
- Be Cautious with Smart Devices: Secure your IoT devices by changing default passwords and keeping firmware updated.
- Practice Safe Social Media: Be cautious about the personal information you share on social media platforms.
- Use Virtual Private Networks (VPNs): Employ a reliable VPN service, especially when using public Wi-Fi networks.
Download the infographic HERE
The new Webroot PC Optimizer boosts computer performance
Think back to when your brand new laptop or desktop ran the smoothest, operating at peak performance. Is it still that fast, or does even the simplest task seem to take forever? Before you ditch your current PC, there’s a way to get it running like new again.
First things first, though—you have to understand why your PC is running slowly.
Do computers slow down with age?
If you’ve had your PC for a while, you might think it’s running slower because of aging hardware. But not even brand-new computers run at their optimal speed due to preinstalled bloatware.
What is bloatware?
Any application or software you don’t install on your device is bloatware. For example, the last laptop I got had an antivirus software trial preinstalled—not necessarily a bad thing, but still bloatware. Maybe you have a MacBook that has creative applications like GarageBand preinstalled. That’s bloatware too.
Bloatware isn’t always preinstalled. Some applications you download may include adware or utilities that slow down your PC.
How do I get my PC to run faster?
The tricky part about optimizing your PC is that the things that slow it down can be difficult to pinpoint. Maybe you’ve deleted all your unwanted and unused apps and data, but your computer is still running slowly. If this is the case, you need a PC optimization tool .
How does PC optimization improve performance?
With PC optimization software, you can:
- Declutter your PC of junk files, unnecessary programs, and temporary files.
- Remove unneeded background processes and programs to improve speed.
- Free up bandwidth to browse and stream faster.
Why is it important to optimize your PC?
It can be tempting to give up on your current PC and just go buy a new one. But consider sustainability issues, your budget, or even the hassle of transferring all your data to a new PC and spending time configuring it. If other parts of your hardware work perfectly—the screen, keyboard, speakers, battery, and so on—it’s worth optimizing and keeping your current hardware.
From a day-to-day perspective, your PC helps you create or enjoy videos, music, photos, documents, and much more to unleash your creativity, plan your life, and run your business. You need it operating at its full power and performance to handle demanding apps like video editing or 3D gaming.
What kind of PC optimization software should you get?
Look for these five features when researching PC optimization tools:
- Registry tuner: Cleans up the repository that contains massive amount of data about your PC.
- Hard drive defragmenter: Moves scattered data blocks closer together to improve read times.
- Startup manager: Manages which applications and utilities open when you start your computer.
- Junk file remover: Finds and deletes bloatware and junk files.
- Internet connection booster: Improves your internet speed.
Webroot™ PC Optimizer check all these boxes. Along with antivirus protection and data backup, Webroot keeps your computer running smoothly. Make PC optimization part of your regular digital hygiene and see the benefits firsthand with Webroot.
10 steps to safeguarding your privacy online
The more devices, digital apps and online accounts you use, the more efficient and convenient your life becomes. But all that ease of use comes with a price. Your devices are constantly collecting your personal data to fine-tune your user experience. At the same time, hackers, and other cyber criminals are working round the clock to steal this sensitive information.
Think of your digital identity as a confidential file full of high-value information – passwords, credit card numbers, bank account details, social security numbers and more. If you’re not taking the proper steps to guard your online privacy, you could end up handing over the files to a vast army of cybercriminals.
According to the Identity Theft Resource Center, there were 3,205 data compromises in 2023. That’s a 20% increase over the previous year. A data compromise can consist of any of the following:
- Data breach: Unauthorized access to your confidential information (i.e. social security number, date of birth, credit card number, address, etc.)
- Data exposure: Confidential information is likely exposed, but may or may not have been accessed
- Data leak: Accidental exposure of sensitive information, which may or may not have been accessed
High-profile companies and organizations are not immune to these attacks. many of which resulted in consumer data exposure. Here’s just a few that happened this last year that may have impacted your personal data.
- National Public Data: Nearly 3 billion Americans had their personal records, including social security numbers, hacked and leaked on to the dark web.
- T-Mobile: About 37 million T-Mobile customers had their personal data compromised in a January 2023 hack that accessed names, addresses and birth dates.
- Ticketmaster: In May, 2024, over 560 million customer records, including names, addresses, emails, order history and payment information, were leaked online and offered for sale by hackers who infiltrated Ticketmaster.
The best defense to counter these cyberattacks is always a good offense, so be proactive and protect yourself. Here are some essential tips for safeguarding your online identity:
- Create secure passwords: When it comes to passwords – longer is stronger. Make them complex and unique, incorporating letters, numbers and symbols.
- Turn on multifactor authentication: Add multi-factor authentication to your logins for extra security. This second step helps confirm your identity by sending a text or email with a security code or question.
- Limit how much personal information you share online: Be wary of oversharing on social media. Cybercriminals can act like detectives, putting personal details together to steal your identity.
- Limit app access to your information: Apps collect your data and share it, so be sure to manage your app permissions and control how much access they have to your information.
- Adopt safe browsing habits: Update browser privacy settings and avoid suspicious websites. Also, limit the number of cookies you accept and clear your browsing history and cache regularly.
- Beware of phishing scams: Phishing scams appear in our email inboxes, text messages, social media, and even voicemails. They’re designed to trick you into giving up your personal and financial information, so learn the tell-tale signs and avoid these scammers.
- Beware of public Wi-Fi: Public Wi-Fi networks often lack security, giving hackers easy access to your data. Always confirm your connection is encrypted and avoid making financial transactions unless you’re on a private network.
- Use a VPN: A VPN (virtual private network) protects your online identity and information. A trusted VPN will encrypt your internet connection and hide your IP address from potential hackers
- Use an all-in-one device, privacy, and protection solution: For ultimate device, privacy, and identity protection, use an all-in-one device solution like Webroot Premium and get the best of all worlds –threat detection, password manager, dark web monitoring, and real-time virus protection.
- Keep your devices and apps up to date: Install updates to get the newest features and latest security upgrades. Enable automatic updates to make sure you’re always protected.
Remember that the tech that makes your life easier is also tracking you and gathering your sensitive details. Cyber thieves will never stop trying to crack the safe and steal your precious data, but with a few smart moves, you can lock them out and protect what might be your most valuable asset of all – your online privacy.