Cyber News Rundown: Banking Trojans in Google Play
Banking Trojans Still Appearing in Google Play Store
Multiple security researchers recently discovered a handful of banking trojans that have still managed to make their way into the Google Play app store, despite Google having increased its security to detect such apps. Many of the apps are disguised as astrology/horoscope software, but instead of reading the future, they steal SMS and call logs from the device, install unauthorized apps, and even seek out banking credentials based on other installed applications. Some of these apps had been installed by up to 1,000 individuals, many of whom are likely under the assumption that the app removed itself, after showing a fake error message claiming incompatibility with the device.
Obama-themed Ransomware Forges Dangerous Path
A new ransomware variant bearing the face of the former US president, Barack Obama, has been spotted in the wild performing some unusual encryption tactics. Rather than encrypting personal word documents and pictures, this variant focuses on encrypting executable files across the system, which could lead to the system crashing and other devastating results. It is still unclear if this methodology is the intent, or just an oversight by the ransomware’s authors, but this type of damage is unlikely to pay off if it renders the system nonfunctional.
Thousands of Online Stores Compromised
Due to security loopholes in eCommerce sites that use Magento as a host, nearly 8,000 sites have been confirmed to be hosting card-skimming malware, with up to 60 more being compromised every day. The breaches led to malicious scripts being added to the pages to record and upload any customer inputs in real time, rather than following a more complicated path to obtain the same data after the transaction is complete. Unfortunately, it is difficult to determine whether a site is safe without checking the entire codebase for any unauthorized entries.
Fake Tech Support Ads Now Indistinguishable from Real Counterparts
In the run-up to Google’s release of a verification program for third-party vendors to display ads, the company has been inundated with countless fake tech support advertisements that are nearly impossible to identify over a real vendor’s ads. The creators of these fake ads will go to almost any lengths to avoid detection, including creating entire companies to continue their illicit activities.
Unsecured Sites Leaving .git Repositories Easily Accessible
Nearly 400,000 websites have been found with exposed .git directories that could lead to major information exposure, if improperly accessed. These repositories contain everything from passwords and API keys for the site, to forgotten data stored on the sites. Fortunately for the website owners, the researcher who discovered the breach was not acting maliciously, and quickly began contacting them with information on how he found the leak and what they could do to resolve it.
EICAR – The Most Common False Positive in the World
If you saw a file called eicar.com on your computer, you might think it was malware. But, you would be wrong. Readers, if you haven’t yet met the EICAR test file, allow me to introduce you to it. If you have used the EICAR test file, let’s get a bit cozier with it.
If you ran this file through VirusTotal, 61 out of 62 antimalware scanners currently would detect the EICAR test file as if it were malicious. That’s because the EICAR file is actually a tool that was designed to help users verify their antimalware scanner is functioning properly. The EICAR test file is a harmless piece of code that most vendors have agreed to flag as if it was malicious. Essentially, it’s a false positive—by design—for your benefit. Some scanners detect it, some do not; neither outcome indicates that any scanner is better or worse than another.
If you have heard of EICAR, you may have seen it referred to as a “test virus,” but that’s inaccurate. Think of it more like the test button on a smoke detector in your home. The test button doesn’t simulate fire or smoke; it simply lets you know that the smoke detector is functional. The test button certainly doesn’t tell you anything about the quality of the smoke detector. Similarly, the EICAR test file does not simulate malware, it just causes a scanner to demonstrate how it would handle a threat it detected (assuming the vendor has chosen to recognize the file as malicious, that is.)
Using the EICAR Test File
Now that you know more about EICAR, let’s talk about why, how, and when you might want to use it.
- Curiosity. The first time I used the test file, it was purely out of curiosity. What if I zipped the file up or changed its extension from .com to .xyz, and so on. Because the file itself is harmless, I could simulate any number of scenarios without risk to my computer or my data.
- Smoke test. The intended purpose of the test file was always to verify that your scanner was properly installed and that the scan engine was functional. Any time you install a new antimalware product, you can give it a quick test with the EICAR file to make sure it is functioning as designed (if the vendor support the file, that is.)
- Forensics. Malware writers often try to disable a scanner as soon as their malicious code gains a foothold on a given computer. If you periodically test your scanner and, one day, it fails to detect the test file, that could indicate of an infection. Keep in mind, it could also indicate that another layer of security blocked the file before it got to your scanner. The test itself is not conclusive and should only be considered as part of a bigger picture.
- Behavioral information. Between 1997 and 2004, I worked at Microsoft, ensuring none of their software releases were infected. I used 11 different virus scanners on each of my test machines (don’t try this at home). The testing was not about the quality of the scanners, but rather how they’d react in different situations to help me make decisions and gain greater knowledge. For example, antivirus scanners have default configurations that I needed to test and potentially modify. Back then, not all scanners scanned all extension types by default. A directory with EICAR test files that each had different extensions would allow me to determine if my scanner’s default configuration for file types needed to be adjusted. Once I made modifications, I had to test those as well. There were a variety of tests I could run involving filenames with punctuation or foreign language characters, too. Basically, I could test virus handling without needing am actual virus.
Note: At the Virus Bulletin conference in 1999 I presented the paper, “Giving the EICAR Test File Some Teeth.” If you’re interested in the breadth of test scenarios I explored, you can read the paper on the Virus Bulletin website.
Where to Find EICAR
You’d think the easiest way to get your hands on this file would be to download it straight from www.eicar.org, except that your antimalware scanner might block the download. To get around that, you’d likely have to temporarily disable your web protection—WHICH I DO NOT RECOMMEND. Instead, I’ll show you how to create the file yourself.
Here are the step by step instructions.
- Open Notepad.
- Copy the following string and paste it into Notepad:
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H* - Save the file and cross your fingers that your scanner doesn’t detect it on close.
Note: You could create the file in Microsoft® Word, but you’d have to save it as plain text. The test file must begin with the test string, and Word includes additional information in .doc and .docx files.
The file eicar.com, will run on older operating systems, but not on a 64-bit OS. When you run it on a compatible OS, the file will display this text.

You can change the display message to anything you like. In the following example, I’ve replaced the word EICAR with my name.

However, if you change it as I did above, it will no longer be a valid test file and should not be detected by your antimalware program.
At the 1999 Virus Bulletin conference, I asked researchers for EICAR-like test files to test script and macro detection. Although we still don’t have that, the Anti-Malware Testing Standards Organization (AMTSO) provides a set of security feature checks at www.amtso.org/security-features-check. Just be sure to remember that the security feature checks, like the EICAR test file, don’t indicate the quality of the product, but they can be used to ensure that certain features are functioning.
Questions? Comments? Let’s talk on the Webroot community forum.
Cyber News Rundown: Texas Voter Data Leaked
Texas Voters’ Data Leaked
A security researcher just discovered a publicly-available file containing sensitive voting information for nearly 99% of all registered voters in the state of Texas. The file was compiled by a data firm that was trying to gauge political opinion for the 2016 elections, as well as more localized campaigns. With all the attention the presidential campaigns brought to election security, mistakes like this one could lead to more serious outcomes if companies who handle such information don’t take the necessary precautions.
Chinese Hotel Breach Exposes 130 Million Guests’ Data
Huazhu Hotels Group has come under fire after several of their customer databases were uploaded to GitHub by their own development team. The databases were found for sale on the Dark Web and contained over 240 million unique records, with information ranging from names and addresses to card numbers and travel itineraries, a portion of which has been verified by a local security firm. The data appears to come from nearly all the hotel group’s brands, and is not localized to a specific region or name.
Instagram Unveils Support for Third-Party 2FA
Nearly a year after Instagram announced their addition of SMS-based 2FA, the company has stated that they now allow support for third-party 2FA applications. In doing so, they give users the option to either set up an SMS verification path or receive a code through another app when attempting to log in to their account. This announcement comes just weeks after a string of high-profile accounts were hacked, leaving users with no options to regain access to the hijacked pages.
Bank of Spain Hit by DDoS Attack
Over the weekend, the Central Bank of Spain fell victim to a DDoS attack that continued through Tuesday afternoon, leaving users with spotty access to the bank’s website. Fortunately, the bank itself remained fully operational through the attack, as they are a central bank rather than commercial. Additionally, all communications with other Central Banks around Europe were unaffected, with no signs of other malicious activity.
HTTPS Now Standard on over Half of Top Sites
With the push to enforce full encryption on the internet, over half of the top million sites are now using HTTPS, with millions of domains switching over every day. This is likely due to Google’s efforts in the last couple months to warn Chrome users who attempt to access an unsecured site, in hopes of encouraging users to take their own security more seriously.
Cyber News Rundown: Dark Tequila Malware
Dark Tequila Targets Mexican Financial Organizations
Over the past 5 years, one malware campaign has been plaguing the financial industries of Mexico: Dark Tequila. While many researchers have been monitoring samples for most of that time, only recently has the entire campaign come into focus, with over 30,000 unique targets in 2018 alone. Using mostly spear-phishing tactics, the malware is able to spread quickly and steal a significant amount of information with relative ease and, for its finale, a USB infector is copied to any removable drive enabling it to spread across offline channels.
Babysitting App’s Database Breached
Over 93,000 users of the popular child-sitting app Sitter are being notified after the MongoDB database the app uses was compromised. Most information on the app is considered highly sensitive, including names, home addresses, and even full address book contacts for thousands of users. It remains unclear how long the database remained unprotected and Sitter is now contacting all affected users.
Ryuk Ransomware Uses Highly Targeted Attacks
The authors behind the ransomware variant Ryuk have taken significant strides towards ensuring large ransom payouts by focusing exclusively on large corporations and demanding Bitcoin ransoms that only those organizations could even fathom paying. They have already received two ransoms ranging from 15 to 35 Bitcoins, or roughly $225,000, with a daily ransom increase of half a Bitcoin for each day unpaid.
American Healthcare Organization Hit by Phishing Attack
Recently, Augusta University Health announced that, in September 2017, they experienced a data breach that could possibly affect over 400,000 patients. Listing sensitive data from home addresses to social security numbers and other forms of ID, this breach could easily set up future phishing attacks on individuals. Officials are still working to determine how such a breach could have occurred (and remained undetected for nearly 10 months). Because of a lack of encryption, the breach was far more damaging than it otherwise would have been.
Cardio-Imaging Devices Vulnerable to Exploits
Several versions of Philips’ cardiovascular imaging devices have been found to contain multiple exploits that would easily allow an attacker to perform unauthorized code execution and cause the devices to malfunction. Fortunately, these devices are not remotely accessible, and the company has already begun putting new safeguards in place with their next major patch.
Cyber News Rundown: Instagram Hack Baffles Users
Instagram Hack Baffles Users
Hundreds of Instagram users have found themselves locked out of their accounts over the past week, with all methods of retrieving them having been removed as well. The episode began with many users noticing their accounts had been logged out and contact information changed, including email addresses with a .ru domain. Even though some users have been able to follow Instagram’s prescribed process to regain control of their accounts, many others hit roadblocks, frustration, and days of failed attempts.
Adobe Suite Receives Multiple Patches
Following Patch Tuesday, Adobe users found themselves on the receiving end of 11 total patches for Flash Player, Acrobat, and several other key programs. Most of the patches were related to remote code execution caused by improperly escalated access privileges. The company said it remains confident none of the flaws addressed were exploited before they were patched.
Millions Vanish in Indian Bank Hack
One of India’s largest banks announced that its systems had been hacked this week, with at least $14 million remaining unaccounted for. The largest chunk of funds were stolen with a cyberattack on the bank’s ATM servers that allowed hackers to simultaneously withdraw funds from ATMS in 28 different countries before transferring another couple of million dollars to a company based in Hong Kong. While officials are working closely with law enforcement to determine the attacker’s identities, it is very unlikely that they investigation will turn up anything of worth, judging by investigations of similar hacks in the past.
Finnish DDoS Attack Shuts Down Government Sites
On Sunday a handful of Finnish government sites became unavailable after a DDoS attack prevented users from logging into Suomi.fi, which handles identity verification for ministry-related sites. While some ministry sites don’t require the Suomi site for verification, this attack has prompted an increase in security measures used for sites that providing critical functions. Fortunately, the attack subsided after several hours and all affected sites were returned to normal by Sunday evening.
Fortnite Cheats Lead to Nothing but Infections
With Fortnite more popular than ever amongst the younger generation, a new wave of malicious “cheats” have been making their way around the internet hoping to entice young gamers with hopes of gaining advantages. Many of the available cheat tools offer free in-game currency, movement improvements, and even third-party downloaders for the game itself, all of which result in a malicious payload being installed on the computer while the user remains oblivious.
Cyber News Rundown: WannaCry Shuts Down Taiwanese Chipmaker
Chipmaker Production Halts After WannaCry Attack
A recent WannaCry attack at a Taiwanese chip manufacturerhas brought production to a standstill and threatens delays for new Apple products yet to be released. The manufacturer has announced that after two days their systems are clear and production is able to continue, blaming their own negligence for the attack rather than a targeted breach. Fortunately, no business or personal information was compromised and the infection was handled promptly.
Routers Cause Spread of Global Cryptomining Attack
Researchers have been following the increasing spread of a cryptomining attackover the past week that has affected nearly 200,000 MikroTik routers across the globe. The attack appears to stem from a single attacker, who likely targeted the MikroTik devices due to their high-volume of usage within large corporations and even ISPs, giving them the largest possible net for potential cryptomining. Even though MikroTik implemented a patch for this type of vulnerability back in April, there are still thousands of unpatched devices just waiting to become part of a swift growing network of infected mining machines.
Hackers Hit Hong Kong Healthcare
Several computers within the Hong Kong Health Department were recently victimized by a ransomware campaignthat, surprisingly, doesn’t demand a ransom payment. Though the attack has been traced back to mid-July, the identity of the attacker and their motivations are still unknown. Luckily, systems containing personal data were unaffected by the attack, and proper backups of the targeted systems mean that no operations were halted by the encryption.
Patient Records System Infested with Bugs
The widely-used OpenEMR platform, a patient management system, was found to contain numerous bugsthat could have allowed the records for over 100 million patients worldwide to be exposed. Several of the bugs would have allowed anyone with minimal credentials to obtain sensitive data, ranging from the scheduling and billing of medical procedures to administrative access for health organizations. Patches were quickly implemented by OpenEMR after they were informed of the bugs by a third-party security team.
TCM Bank Applications Leaked
Up to 10,000 customers are possibly affected after a year-long breachby a third-party firm allowed their sensitive information to be compromised. The breach affects those customers who applied for a TCM credit card from March 2017 to July 2018, with TCM confirming that at least 25 percent of the total applications in that period were leaked as part of this issue. Within 24 hours of being notified, both TCM and the third-party vendor were working to resolve the leak and to find ways to prevent future security issues.
Between Two Worlds: An Interview with Reverse Engineer Eric Klonowski
This week, I’ll be at Black Hat USA 2018 in Las Vegas. If you’ve ever been to Black Hat, then you know all about the flood of information and how hard it can be to take it all in. This year’s presentations will range from the newest trends in browser exploits, bots, and social engineering attacks, to the security status quo and how legal policies shape information security. And it’s anyone’s guess what the hottest topics around the water cooler will look like. To prepare, I reached out to Eric Klonowski, Principal Reverse Engineer at Webroot, to shed some light on his role at Webroot and what he and his peers bring to a major industry event like Black Hat.
Below is our interview, edited for length.
Tyler: Eric, tell us why a role like yours is valuable to security companies.
Eric: If you want to be successful in any industry, you have to have someone who understands the problems, down to the details, that your product is supposed to solve. That’s what I do. I work to understand threats, threat actors, and the malware that’s proliferating to help seal off the vulnerabilities they exploit and prevent attacks.
How has your role at Webroot evolved over time?
When I first came on board in 2015, my role was about 70 percent research, 30 percent development. Now, it’s more like 10 percent research and 90 percent development. We have to stay on top of the latest and greatest invasive techniques. That means we’re doing a lot of development. We have a staff reverse engineer who takes malware apart to write software that will block it better.
It’s not a regular 9-5. I’m a security nut and this work fascinates me, so it’s always on my mind.
It probably helps in your line of work to be able to think like a hacker, except you’re one of the good guys. What’s it like to live in that duality each day?
First off, “hacker” is our word. You don’t use that word.
Whoa.
I’m kidding. But let’s take a second to talk about “hacking.” Back when I was getting proficient at software development, I hung out in hacker forums that were full of people who would use basically copy and paste someone else’s malware to break into systems. I have no respect for that. It doesn’t take any skill or smarts.
The ethical piece aside, I do have respect for people who develop exploits and sophisticated malware. What they do is very similar to what I do. We’re both trying to solve the same problems creatively, efficiently, and effectively. We’re just coming at it from different sides, and with a different goal in mind. So yes, you could call me a hacker, but I’d say I’m a “white hat.”
It’s always fun to poke around and see what you can do, but you do have to know when to draw the line. Sometimes, researching malware is like being a vigilante; you report what you see and make the compromised locations known.
How quickly does your team have to act when they discover a new threat?
Our pace can vary widely, but when we discover a new threat, we try to crush it quickly. We have to move fast to hand our research and development work to the product team so they can integrate a mitigation strategy into our product. For instance, with the WannaCry ransomware attack last year, my phone was buzzing like crazy before I even got out of bed. Some days are like that.
When other researchers release a report of a new malware variant or zero-day, we crack it open and try to get a better understanding of how it might spread. As an example, if we’re examining ransomware, we want to observe the encryption mechanisms it contains. In a way, we look to see if the author made any mistakes.
What types of tools do you use in reverse engineering?
By name, I typically utilize IDA, which is the industry standard. I also rely pretty heavily on WinDBG. When it comes down to it, those tools make your job easier. But someone in my position can use a pretty wide variety of tools to disassemble software and extrapolate what they are looking for.
You once told me reverse engineering was the “ultimate puzzle.” How did you discover this type of work?
I’ve always liked taking things apart and making them work better, and I started writing code when I was nine or 10. Later, I was hired as an intern for a defense contractor and had to do a lot of security-related research and software development. That’s really where it started, and I chose to stay on full-time for a few years. Until then, I was self-taught and didn’t really understand software on a large scale, but I learned so much about development from the people I was working with. I also worked on a lot of personal projects that propelled me forward on this path.
Where there any “aha moments” for you that made you decide this was the right career?
When I started at Webroot and became familiar with how the product functioned, I was pretty excited to see that we really do a great job here. We offer such a great product; the challenge to continue to make it better each day pretty motivating. And I’m very fortunate to have found a way to get paid to do something that’s always been a hobby I love.
Eric, thanks for the interview! I know we’re grateful you’re on our team at Webroot.
Cyber News Rundown: Valve Bans Developer for Cryptojacking
Cryptojacking “Game” Found on Steam Store
Valve has taken recent action against an indie-developed game available on Steam, the company’s game/app store, and removed their listing after many customers had complained about cryptomining slowing their systems, once launched. Additionally, the developers have been caught selling in-game items on third-party sites, that were falsely portrayed as being items for another game in hopes of scamming more money from users. Fortunately, Valve was quick to deal with the issue and banned not only the game, but also the developers from submitting new games after their deceptive practices.
In-depth Look at Deepfakes
As special effects technology becomes more advanced, so too are those that would abuse its capabilities to cause unrest. With the release of Deepfakes, a video software that allows anyone to put any face on a body, or into a video, the power once held only by major production studios is now available to anyone with a computer. While many Deepfakes users have opted to create fake pornographic videos using popular celebrities, the software has also been used to cause political tension by falsely placing a politician’s likeness into a video with completely different audio and then distributing it as a legitimate recording.
Personal Data Easily Found by Researcher
A security researcher recently discovered a security flaw that allowed him to access personal records for over half a million customers of Fashion Nexus. While the company claims that no financial data was revealed, the personally identifiable info (PII) would be more than enough for an attacker to start committing large volumes of identity fraud. After quickly resolving the security issue, the company issued a recommendation to all customers of multiple affected e-commerce sites to change their passwords.
Google Removes Android Apps Containing Windows Malware
At least 145 Android apps have been removed from the Google Play Store after researchers discovered that they all contained malicious executables for the Windows operating system. While they will have no effect on an Android device, it still raises questions about the developer and if the system they are creating apps in has been maliciously compromised. A bigger issue would be faced if any device with an infected app was connected to a Windows computer, as the malware itself appears to focus on gathering keyboard input and searching for sensitive information stored on the system.
Yale Discovers Data Breach Nearly a Decade Too Late
After doing some vulnerability testing on several of their servers, Yale University became aware of a data breach that had occurred sometime in 2008. Even though Yale did a complete wipe of the servers in 2011, they had no idea of the previous breach and have only just begun contacting affecting alumni. Data being stored on the servers contained everything from name and physical addresses to social security numbers and birthdays, which would give any attacker significant strides towards stealing identities.
Crime and Crypto: An Evolution in Cyber Threats
Cybercriminals are constantly experimenting with new ways to take money from their victims. Their tactics evolve quickly to maximize returns and minimize risk. The emergence of cryptocurrency has opened up new opportunities to do just that. To better understand today’s threat landscape, it’s worth exploring the origins of cryptocurrencies and the progress cybercriminals have made in using it to advance their own interests.
The FBI screen lock
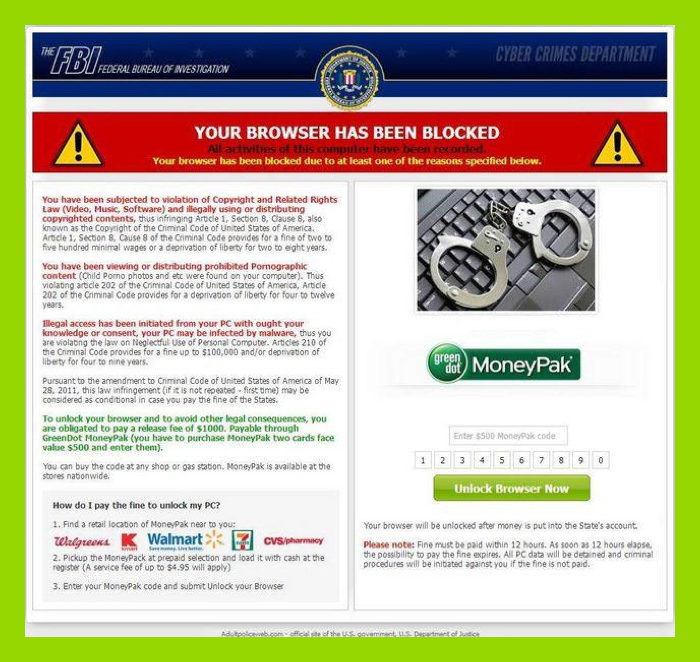
Source: @DavidSGingras on Twitter
Many readers may remember the infamous FBI lock malware that would pop up and prevent users from using their computer at startup. The malware presented the (false) claim that the victim had downloaded copyrighted material illegally or had watched pornography.
This was a common and successful scam that made millions globally by localizing the “official” police entity in order to legitimize the threat. The money it made was transferred via Ukash and MoneyPak, which were essentially gift cards available at local convenience stores that could be loaded with specified amounts of cash. Victims would enter the pin on the back of the card to pay the criminals.
This method of collecting money wasn’t without risks for criminals, however. If enough victims reported the scam to law enforcement, they would try to find and identify those responsible (attention criminals obviously tried to avoid).
Bitcoin and Silk Road
While the Ukash and MoneyPack scams were still alive and well, another popular and anonymous black market called Silk Road was experimenting with Bitcoin as a payment system.
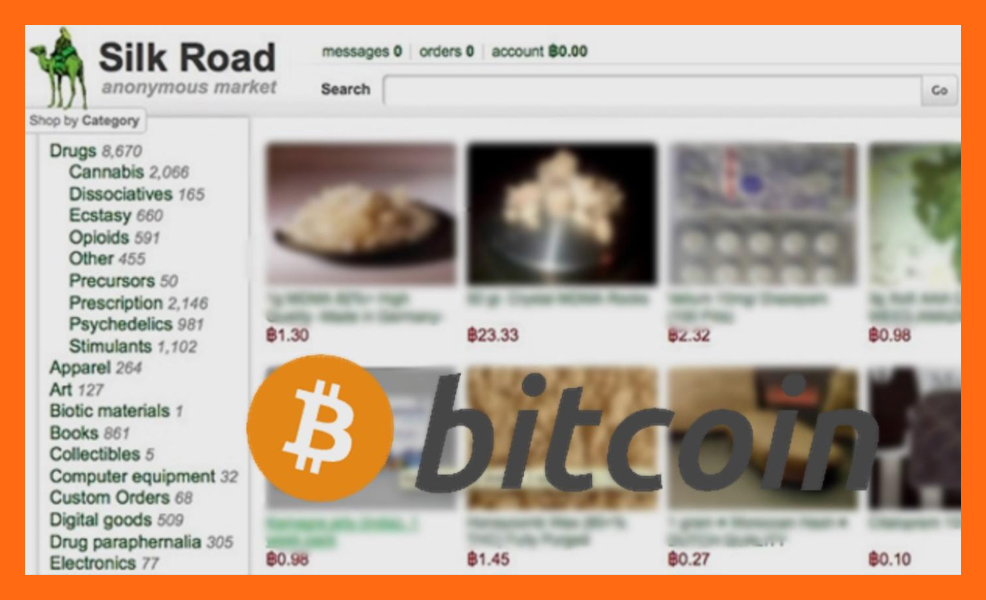
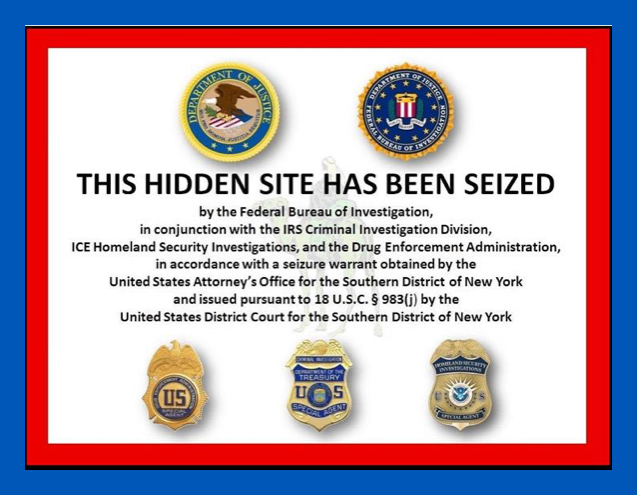
Silk Road was essentially an underground market on the encrypted dark web for goods otherwise illegal or extremely difficult to purchase in most countries. The site’s buyers and sellers remained effectively anonymous to one another and were almost impossible to track. For years this marketplace thrived and proved the efficacy of Bitcoin as a transactional system. Its success came to an abrupt halt in 2013, however, when the FBI seized Silk Road and arrested its founder.
The shutdown initially caused a nosedive in Bitcoin’s market price, but it quickly bounced back to surpass its value even at the height of the Silk Road.
So, what contributed to the shift?
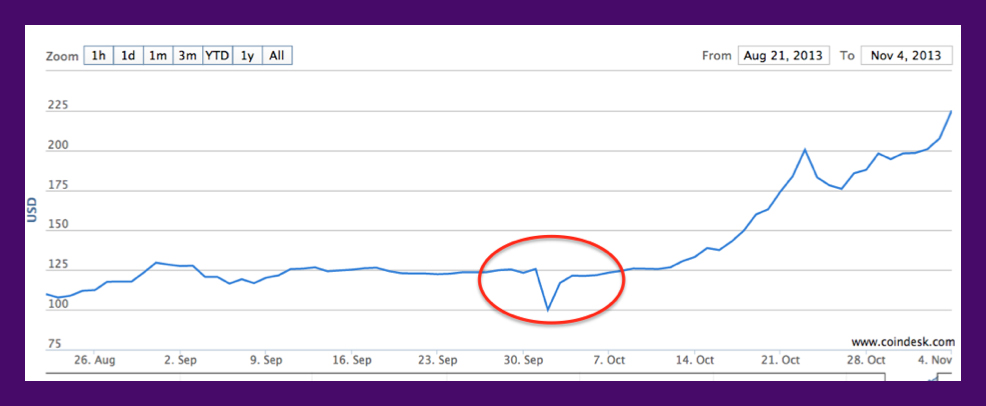
Source: coindesk.com
Enter CryptoLocker
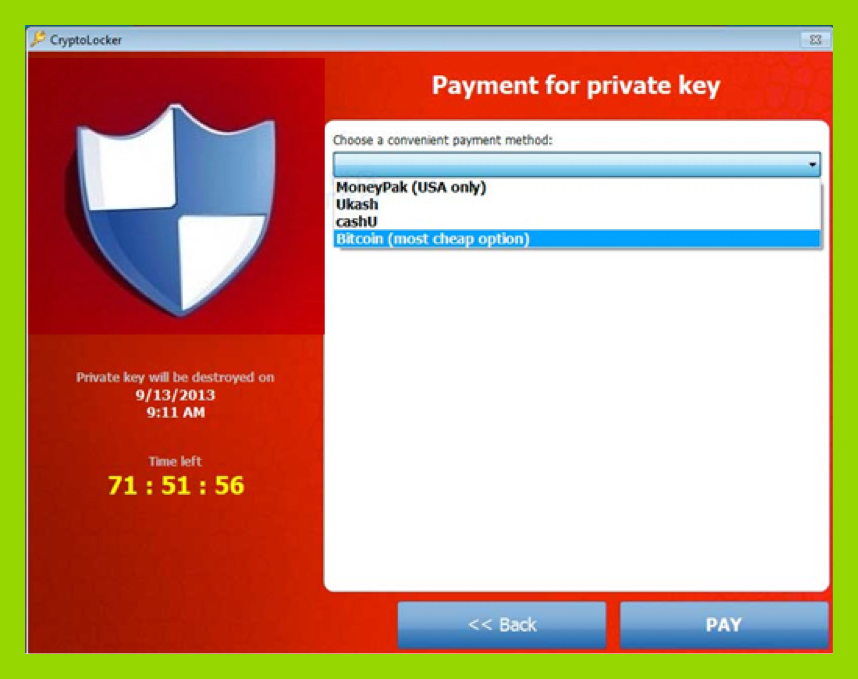
The first variants of Cryptolocker ransomware were seen in late September 2013. In terms of criminal business models, it was an instant success. Soon, many variants were infecting users around the world. Early editions accepted the still widely-used Ukash and MoneyPak as payment, but with a twist. Cryptolocker would provide a discount for Bitcoin payments. The proverbial Rubicon had been crossed in terms of cryptocurrencies receiving preferential treatment from cybercriminals. With ransomware rapidly rising to the top of the threat landscape, Bitcoin saw corresponding growth as fiat currencies were exchanged for it so ransoms could be paid.
Is Bitcoin Anonymous?
Not really. Since all Bitcoin transactions are recorded on a public ledger, they are available for anyone to download and analyze. Each time a victim pays a ransom, they’re given a Bitcoin address to which to send payment. All transactions to and from this address are visible, which, incidentally, is how the success of many ransomware campaigns is measured.
When a criminal wants to cash out Bitcoin, they typically need to use an exchange involving personal identifiable information. So, if a criminal isn’t careful, their victim’s Bitcoin wallet address can be tracked all the way to the criminal’s exchange wallet address. Law enforcement can then subpoena the exchange to identify the criminal. Criminals, however, are often able to keep this situation from unfolding by using tactics that prevent their “cash out” address from being flagged.
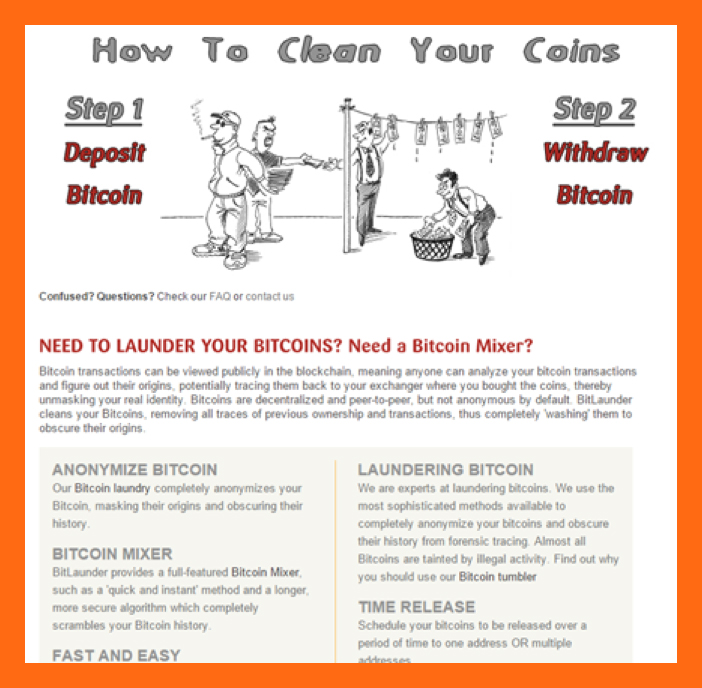
For a time, Bitcoin “mixers” offered to clean coins that were widely available on the dark web. Their methods involved algorithms that would split up and send dirty coins of varying amounts to different addresses, then back to another address clean, a process not unlike physical currency laundering. Yet, the process was not foolproof and did not work indefinitely. Once cryptocurrencies had gained significant legitimate adoption, several projects were started to search Bitcoin blockchain transactions for fraudulent activities. Chainalysis is one example.
Ransomware takes multiple cryptocurrencies
In the spring of 2014, a new cryptocurrency arrived. Dubbed Monero, it filled Bitcoin’s shoes, but without a public ledger that could be analyzed. Monero quickly became criminals’ most useful payment system to date. It uses an innovative system of ring signatures and decoys to hide the origin of the transactions, ensuring transactions are untraceable. As soon as criminals receive payment to a Monero wallet address, they’re able to send it to an exchange address and cash out clean, with no need to launder their earnings.
Monero started to see “mainstream” adoption by criminals in late 2016, when certain flavors of ransomware started experimenting with accepting multiple cryptocurrencies as payment, with Bitcoin, Ethereum, Monero, Ripple, and Zcash among the most common.
The Emergence of CryptoJacking
Monero has proven useful for criminals not just because it’s private. It also has a proof-of-work mining system that maintains an ASIC resistance. Most cryptocurrencies use a proof-of-work mining system, but the algorithm used to mine them can be worked by a specific chip (ASIC) designed to hash that algorithm much more efficiently than the average personal computer.
In this sense, Monero has created a niche for itself with a development team that maintains it will continually alter the Monero algorithm to make sure that it stays ASIC-resistant. This means Monero can be mined profitably with consumer-grade CPUs, sparking yet another trend among criminals of generating money from victims without ever delivering malware to their systems. This new threat, called “cryptojacking,” has gained momentum since CoinHive first debuted its mining JavaScript code in September 2017.
The original purpose of crypto-mining scripts, as described by CoinHive, was to monetize site content by enabling visitors’ CPUs to mine Monero for the site’s owners. This isn’t money from thin air, though. Users are still on the hook for CPU usage, which arrives in the form of an electric bill. While it might not be a noticeable amount for one individual, the cryptocurrency mined adds up fast for site owners with a lot of visitors. While CoinHive’s website calls this an ad-free way to generate income, threat actors are clearly abusing the tactic at victims’ expense.
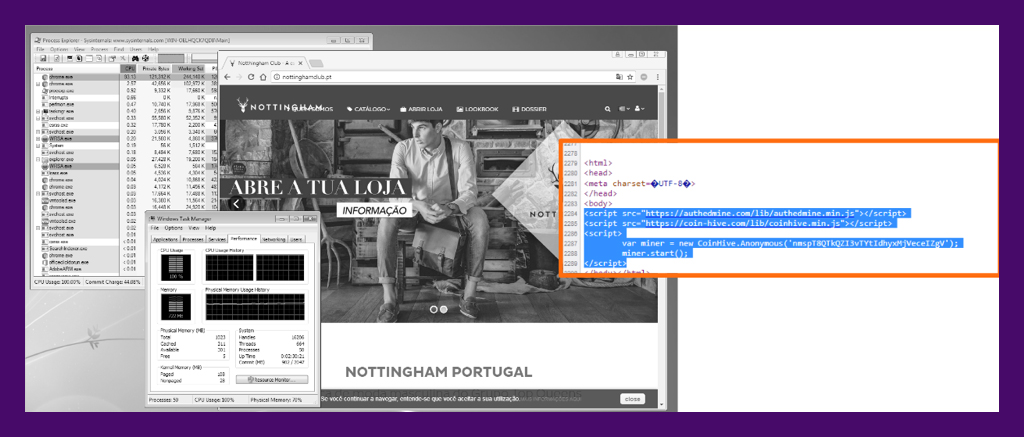
We can see in the image above that visiting this Portuguese clothing website causes the CPU to spike to 100 percent, and the browser process will use as much CPU power as it can. If you’re on a newer computer and not doing much beyond browsing the web, a spike like this may not even be noticeable. But, on a slower computer, just navigating the site would be noticeably sluggish.
Cybercriminals using vulnerable websites to host malware isn’t new, but injecting sites with JavaScript to mine Monero is. CoinHive maintains there is no need block their scripts because of “mandatory” opt-ins. Unfortunately, criminals seem to have found methods to suppress or circumvent the opt-in, as compromised sites we’ve evaluated rarely prompt any terms. Since CoinHive receives a 30 percent cut of all mining profits, they’re likely not too concerned with how their scripts are used. Or abused.
Cryptojacking becomes 2018’s top threat
Cryptojacking via hijacked websites hasn’t even been on the scene for a full year, and already it has surpassed ransomware as the top threat affecting the highest number of devices. After all, ransomware requires criminals to execute a successful phishing, exploit, or RDP campaign to deliver their payload, defeat any installed security, successfully encrypt files, and send the encryption keys to a secure command and control server—without making any mistakes. Then the criminals still have to help them purchase and transfer the Bitcoin before finally decrypting their files. It’s a labor-intensive process that leaves tracks that must be covered up.
For criminals, cryptojacking is night-and-day easier to execute compared to ransomware. A cybercriminal simply injects a few lines of code into a domain they don’t own, then waits for victims to visit that webpage. All cryptocurrency mined goes directly into the criminal’s wallet and, thanks to Monero, is already clean.
That’s why you should expect cryptojacking to be the preferred cyberattack of 2018.
Questions? Drop me a line in the comments below.
Cyber News Rundown: Bluetooth Man-in-the-Middle
Paired Bluetooth Devices Vulnerable to Man-in-the-Middle Attacks
A new vulnerability has been discovered that would allow an attacker to easily view the traffic sent between two Bluetooth-paired devices. The core of the vulnerability relies on the attacker’s device being within wireless range of both devices in the process of being paired. Signals from each device can then be intercepted and injected with malicious code before being forwarded to their intended destinations. Fortunately, the Bluetooth Special Interest Group has already implemented several updates so that a public-key validation is now required before pairing with a new device.
Vehicle Supplier Exposes Data for Key Car Manufacturers
A recent blunder from Level One Robotics left over 150 GB of data from several global car manufacturers on a completely unsecured server. The exposed data included factory schematics, secure request forms, and other highly sensitive information related to the assembly line process and personnel. Unfortunately, the server in question was left with public write privileges, enabling any malicious attacker to freely make changes to any of the data it contained.
Singapore Healthcare Provider Suffers After Major Data Breach
Nearly 1.5 million patients are being contacted after a data breach occurred at SingHealth, one of Singapore’s largest healthcare providers. The breach appears to have been thoroughly planned, as the high-level credentials were quickly attained after a single workstation was compromised. While no medical information was stolen, SingHealth has been reaching out to affected patients with regards to possible phishing scams that may result from the breach.
MoneyTaker Group Uses Unpatched Router to Carry Out Bank Heist
Russia’s PIR Bank recently fell victim to a rather sophisticated breach from the hacker group known as MoneyTaker, which has been responsible for over a dozen similar bank-related hacks over the past couple of years. By gaining access to the bank’s network using an outdated router, the group was able to successfully transfer portions of nearly $1 million to at least 17 different accounts before that money was withdrawn at various ATMs across the country. To make matters worse, it appears that the initial breach happened back in May, with the banks not discovering it until the day after the transfers took place.
Blackmail Scammers Cash in on Adult Site Visitors
Within the last week a campaign targeting visitors to several adult sites began making its way through thousands of email accounts. The scam focuses on scaring the victims with video captures of both their screen at the time they visited the adult site as well as video from the victim’s webcam, in hopes of extorting payments in Bitcoin. By viewing the traffic on the provided Bitcoin addresses, at least 30 individuals have paid the demanded price, gaining the scammers over $50,000 so far.
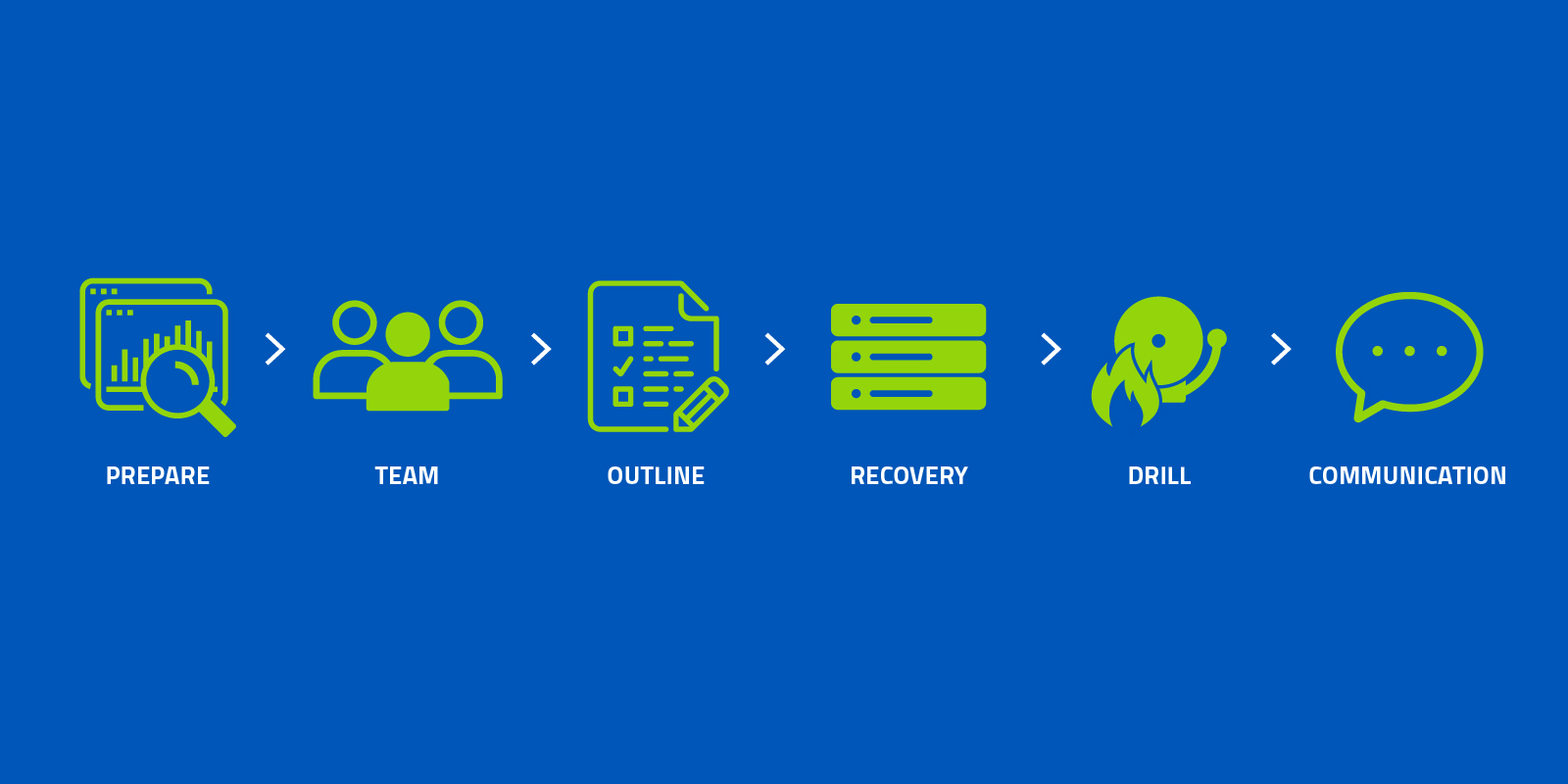
6 Steps to Build an Incident Response Plan
According to the Identity Theft Research Center, 2017 saw 1,579 data breaches—a record high, and an almost 45 percent increase from the previous year. Like many IT service providers, you’re probably getting desensitized to statistics like this. But you still have to face facts: organizations will experience a security incident sooner or later. What’s important is that you are prepared so that the impact doesn’t harm your customers or disrupt their business.
Although, there’s a new element that organizations—both large and small—have to worry about: the “what.” What will happen when I get hacked? What information will be stolen or exposed? What will the consequences look like?
While definitive answers to these questions are tough to pin down, the best way to survive a data breach is to preemptively build and implement an incident response plan. An incident response plan is a detailed document that helps organizations respond to and recover from potential—and, in some cases, inevitable—security incidents. As small- and medium-sized businesses turn to managed services providers (MSPs) like you for protection and guidance, use these six steps to build a solid incident response plan to ensure your clients can handle a breach quickly, efficiently, and with minimal damage.
Step 1: Prepare
The first phase of building an incident response plan is to define, analyze, identify, and prepare. How will your client define a security incident? For example, is an attempted attack an incident, or does the attacker need to be successful to warrant response? Next, analyze the company’s IT environment and determine which system components, services, and applications are the most critical to maintaining operations in the event of the incident you’ve defined. Similarly, identify what essential data will need to be protected in the event of an incident. What data exists and where is it stored? What’s its value, both to the business and to a potential intruder? When you understand the various layers and nuances of importance to your client’s IT systems, you will be better suited to prepare a templatized response plan so that data can be quickly recovered.
Visibility and business context are core requirements for a successful #incidentresponse plan. Know the key resources needed for your business’s success, and in the event of an incident, you’ll be prepared to protect your organization’s critical assets. #cybersecurity
— Gary Hayslip (@ghayslip) July 24, 2018
Treat the preparation phase as a risk assessment. Be realistic about the potential weak points within the client’s systems; any component that has the potential for failure needs to be addressed. By performing this assessment early on, you’ll ensure these systems are maintained and protected, and be able to allocate the necessary resources for response, both staff and equipment—which brings us to our next step.
Step 2: Build a Response Team
Now it’s time to assemble a response team—a group of specialists within your and/or your clients’ business. This team comprises the key people who will work to mitigate the immediate issues concerning a data breach, protecting the elements you’ve identified in step one, and responding to any consequences that spiral out of such an incident.
As an MSP, one of your key functions will sit between the technical aspects of incident resolution and communication between other partners. In an effort to be the virtual CISO (vCISO) for your clients’ businesses, you’ll likely play the role of Incident Response Manager who will oversee and coordinate the response from a technical and procedural perspective.
Pro Tip: For a list of internal and external members needed on a client’s incident response team, check out this in-depth guide.
Step 3: Outline Response Requirements and Resolution Times
From the team you assembled in step two, each member will play a role in detecting, responding, mitigating damage, and resolving the incident within a set time frame. These response and resolution times may vary depending on the type of incident and its level of severity. Regardless, you’ll want to establish these time frames up front to ensure everyone is on the same page.
Ask your clients: “What will we need to contain a breach in the short term and long term? How long can you afford to be out of commission?” The answers to these questions will help you outline the specific requirements and time frame required to respond to and resolve a security incident.
If you want to take this a step further, you can create quick response guides that outline the team’s required actions and associated response times. Document what steps need to be taken to correct the damage and to restore your clients’ systems to full operation in a timely manner. If you choose to provide these guides, we suggest printing them out for your clients in case of a complete network or systems failure.
Step 4: Establish a Disaster Recovery Strategy
When all else fails, you need a plan for disaster recovery. This is the process of restoring and returning affected systems, devices, and data back onto your client’s business environment.
A reliable backup and disaster recovery (BDR) solution can help maximize your clients’ chances of surviving a breach by enabling frequent backups and recovery processes to mitigate data loss and future damage. Planning for disaster recovery in an incident response plan can ensure a quick and optimal recovery point, while allowing you to troubleshoot issues and prevent them from occurring again. Not every security incident will lead to a disaster recovery scenario, but it’s certainly a good idea to have a BDR solution in place if it’s needed.
Step 5: Run a Fire Drill
Once you’ve completed these first four steps of building an incident response plan, it’s vital that you test it. Put your team through a practice “fire drill.” When your drill (or incident) kicks off, your communications tree should go into effect, starting with notifying the PR, legal, executive leadership, and other teams that there is an incident in play. As it progresses, the incident response manager will make periodic reports to the entire group of stakeholders to establish how you will notify your customers, regulators, partners, and law enforcement, if necessary. Remember that, depending on the client’s industry, notifying the authorities and/or forensics activities may be a legal requirement. It’s important that the response team takes this seriously, because it will help you identify what works and which areas need improvement to optimize your plan for a real scenario.
Step 6: Plan for Debriefing
Lastly, you should come full circle with a debriefing. During a real security incident, this step should focus on dealing with the aftermath and identifying areas for continuous improvement. Take is this opportunity for your team to tackle items such as filling out an incident report, completing a gap analysis with the full team, and keeping tabs on post-incident activity.
No company wants to go through a data breach, but it’s essential to plan for one. With these six steps, you and your clients will be well-equipped to face disaster, handle it when it happens, and learn all that you can to adapt for the future.

Cyber News Rundown: Venmo Setting Airs Dirty Laundry
Venmo’s Public Data Setting Shows All
Researchers recently uncovered just how much data is available through the Venmo API, successfully tracking routines, high-volume transactions from vendors, and even monitoring relationships. Because Venmo’s privacy settings are set to public by default, many users have unknowingly contributed to the immense collection of user data available for all to view. In addition to purchases, users can also leave a personalized note for the transaction, some of which range from drug references to more intimate allusions.
This is a great piece with real insight into what people take for granted on social platforms. I’m sure many of the accounts profiled had no idea that so much of their transaction information was public and searchable by default. https://t.co/qEzdkahGAZ #privacy
— Tyler Moffitt (@TylerM_Webroot) July 19, 2018
Spanish Telecom Suffers Major Data Breach
One of the world’s largest telecom providers fell victim to a data breach this week that could affect millions of Movistar customers. The breach allowed current customers to access the account of any other customer, simply by altering the alpha-numeric ID contained within the account URL. While parent company Telefonica was quick to resolve the issue, the communications giant could be forced to pay a fine upwards of 10 million EUR for not complying with new GDPR rules.
DDoS Attacks Target Gaming Publisher
Yesterday, Ubisoft announced via Twitter that they were in the process of mitigating a DDoS attack affecting many of their online gaming servers. At least three of Ubisoft’s largest titles were affected, leaving thousands of players unable to connect to online services. While Ubisoft has likely resumed normal activity, they are not the only gaming publisher to be the focus of these types of attacks. Blizzard Entertainment suffered a similar attack as recently as last week.
ProCare Health Under Fire for Patient Info Database
At least four companies handling the IT needs of the healthcare system in New Zealand have come forward to disclose an extremely large database containing of identifiable information (PII) for more than 800,000 patients. The database in question holds records for many thousands of patients, most of which were gathered without consent from patients, as the company has no direct dealings with them, but instead works with doctors to accumulate more data. While having such a large volume of data in one place can be risky, the security measures should equal the value of the data itself, which is still under scrutiny.
South Korea No Longer Main Target of Magniber Ransomware
Researchers have noticed over the past few weeks a significant trend involving the Magniber ransomware variant branching out from its long-time focus on South Korea to other Asian countries. Additionally, the source code itself has been vastly improved and has begun using an older exploit for Internet Explorer that would allow Magniber to increase infection rates across unpatched systems.