Cyber News Rundown: Edition 6/30/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
Ukraine Hit With Nationwide Cyberattack
In the past week, Ukrainian officials have been making announcements regarding a cyberattack that has affected nearly all of the nation’s industries and government sectors. Also affected is Ukraine’s main airport, creating significant delays. While it is still unclear who initiated the attack, officials are saying that the infection was targeted to cause destruction across a variety of the country’s essential systems.
Wind Farms Surprisingly Insecure
As we move get closer to mass-production of wind power, the security of the turbines themselves is coming under scrutiny. Over the past few years, researchers have been performing penetration tests on multiple wind farms across the US, and have discovered that most are only as secure as the tumbler lock on the turbine door. After accessing the interior of the rarely-manned turbine, researchers were able to gain full control of not only that individual turbine, but every other one connected to the network. In light of such tests, the industry will soon have to make significant improvements to the turbines’ physical security of the turbines, as well as the networks they use.
Petya Ransomware Destroys Data, Rather than Ransoming It Back
Following this week’s Petya cyberattacks, researchers have been working tirelessly to understand the exact circumstances involved. While some believed it to be a ransomware attack, it appears the malware author’s intent was purely destructive. Rather than the typical bitcoin ransom demand, the infection virtually destroys the hard drive in question by encrypting the Master File Table and removing any access to the remainder of the encrypted files.
8Tracks Music Social Network Hacked
Over the past few days, a hacker operating on the Dark Web has posted an offer for 18 million 8Tracks user accounts and passwords. A sample of the data was verified, and, although the usernames and passwords are all SHA-1 encrypted, several web tools are readily available to any buyers determined to crack it. 8Tracks has since confirmed the breach and recommended that all users change their login credentials, especially those that have been used for multiple sites.
South Korean Banks Face Large DDoS Ransom Demand
In the last few days, at least 5 major South Korean banks have been threatened with a large-scale DDoS attack unless they pay a ransom of $315,000 in bitcoins. It’s no coincidence that this attack comes just weeks after the successful ransom of a South Korean web hosting service, though it would appear that the attackers never followed through, as the banks’ sites have remained up and running past the Monday deadline.
Webroot Customers Protected from Latest Ransomware Attack
[Updated June 29, 2017, 10:20 a.m. MDT]
A host of companies across industries have confirmed attacks today by a brutal wave of ransomware, including global law firm DLA Piper, U.S. pharmaceutical giant Merck, and the Danish shipping company Maersk. Although targets originally appeared in Ukraine—shutting down power plants, banking services and supermarkets—this latest cyberattack has quickly spanned critical economic sectors around the globe.
Webroot customers are protected against this variant. This cyberattack was first seen by our threat research team at roughly 10:00 a.m. UTC on June 27, 2017.
What we know
Webroot’s threat researchers have confirmed that this ransomware is a variant of an older attack dubbed Petya, except this time the attack uses EternalBlue to target Windows systems—the same exploit behind the infamous WannaCry attack. While this variant appears to be an upgraded version of Petya, there is no confirmation that this attack is from the same author.
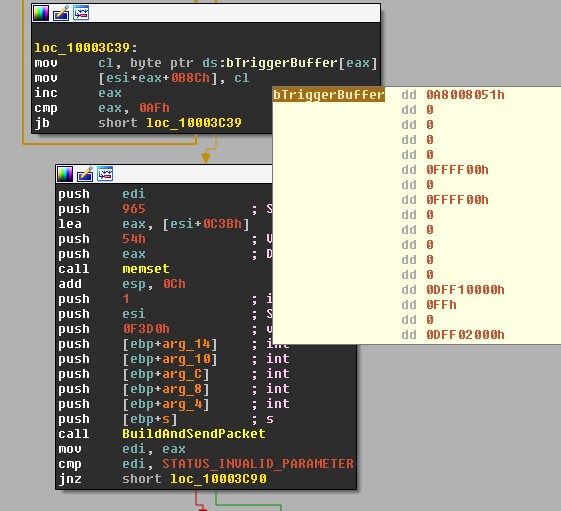
This variant mirrors Petya in that it encrypts the Master File Table (MFT) by overwriting the bootloader code, though unlike previous versions, it encrypts files based on file extension. The system fails to boot as usual and the end user instead sees a screen that appears similar to DOS and demands payment. The shot below depicts the preparation of the EternalBlue triggering packet.
This is the same attack vector that made WannaCry so effective, but we have also observed additional techniques used to infect more machines.
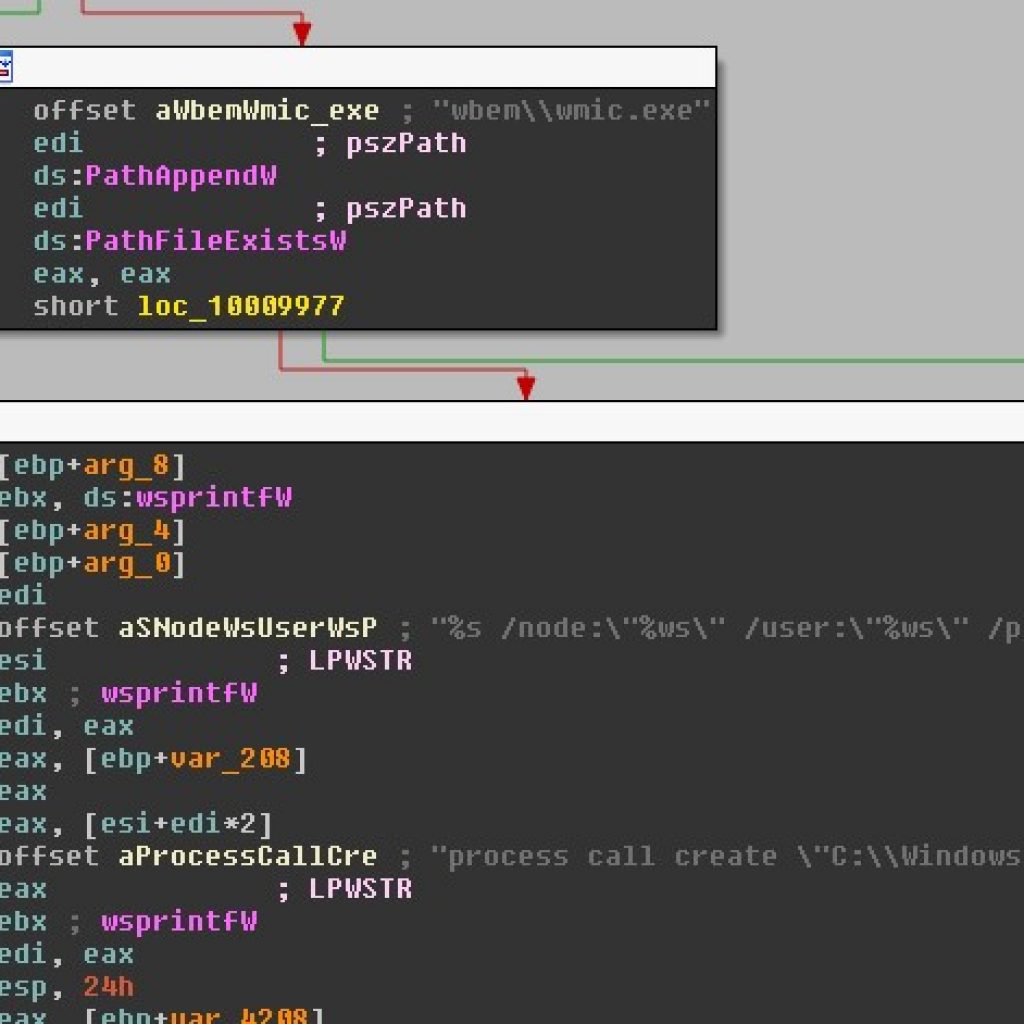
Here we can see that the worm is also utilizing WMI (Windows Management Instrumentation) in a technique to further reach through the network using credentials siphoned from the local machine.
Once the machine is infected, the computer will immediately restart to what looks like a ‘chkdsk,’ but isn’t. Below is an image from Ukrainian Prime Minister Pavlo Rozenko’s Facebook showing the world what the ransomware looks like while it encrypted his computer during this fake chkdsk stage.
Vice Prime Minister of Ukraine, Павло Розенко (Pavlo Rozenko) on Facebook. This is what Petya looks like when it’s encrypting your drive. pic.twitter.com/RgPtfuWK7p
— Mikko Hypponen (@mikko) June 27, 2017
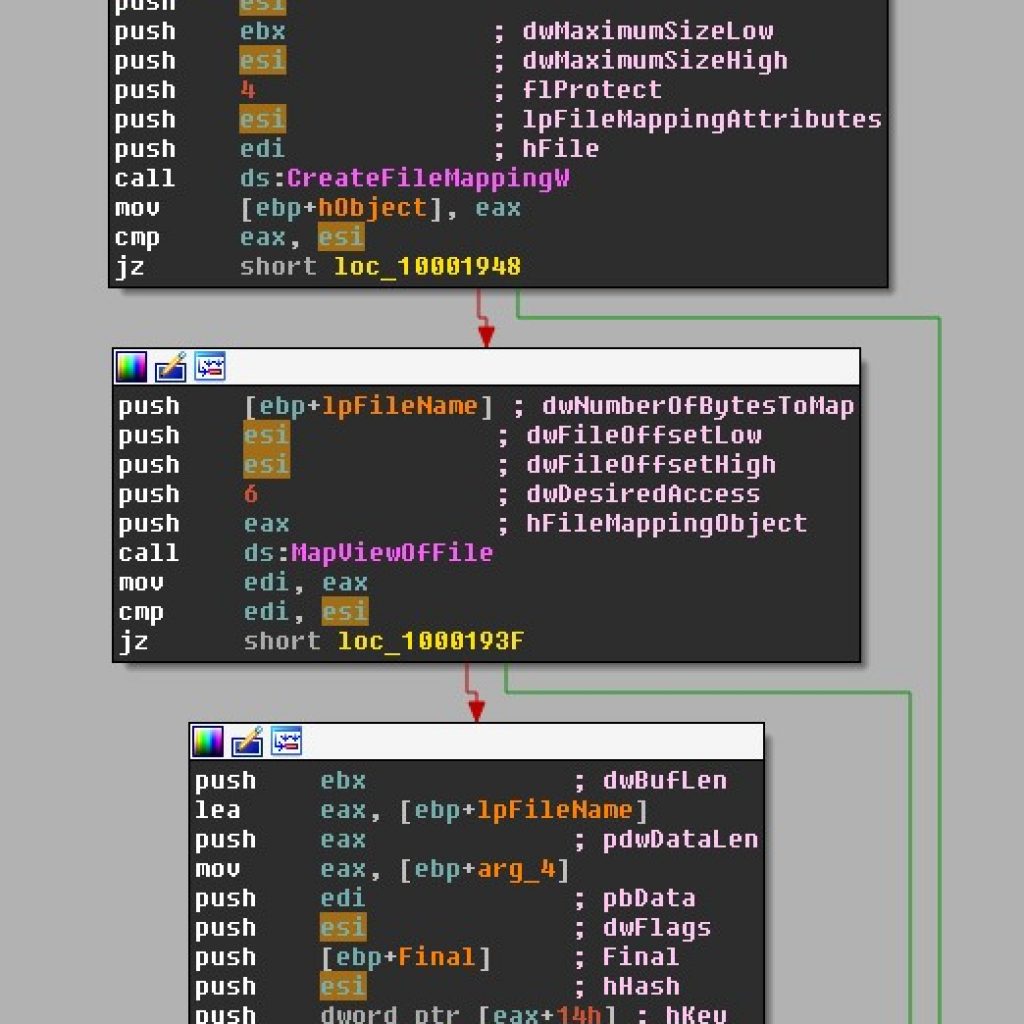
This stage is the ransomware encrypting files on your hard drive. We found that the ransomware doesn’t encrypt the entirety of your files with matching extensions, but instead encrypts up to the first mebibyte of data. This is done presumably to save time during the encryption process, but also ensures that enough of the file is encrypted to be unlikely to restore without paying the ransom.
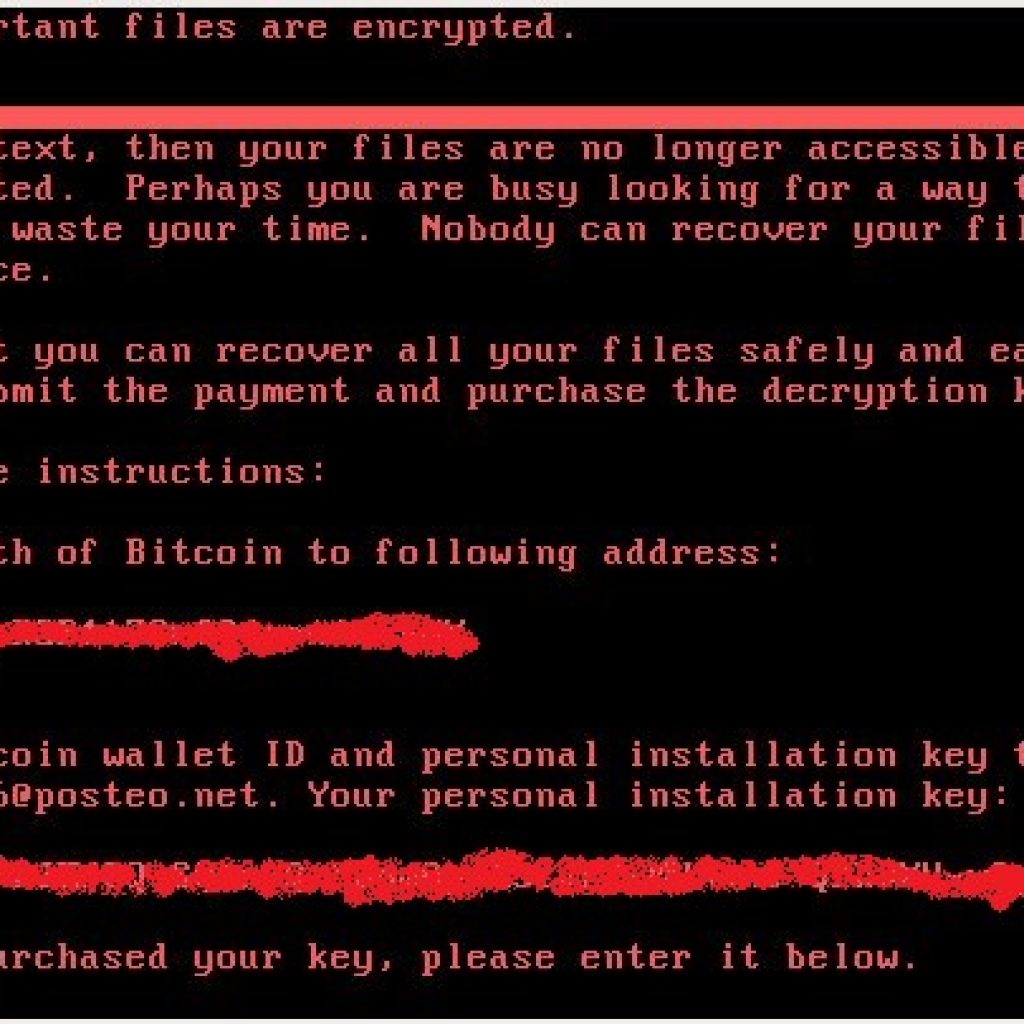
Once the fake chkdsk is complete (or all the files on the computer are encrypted) the infection will reboot the computer once more to this screen:
There is no way for a victim to retrieve their files other than to email the cybercriminal after paying the bitcoin address listed in the ransom. In fact, the email address listed in the ransom has, as of now, been shut down by the email provider. Essentially, this means victims are unable to get their files back, even after paying the ransom, as the payload author is now prevented from checking this email.
It now seems the attack’s intended effect was not to generate ransom payments at all. In a detailed post on the Microsoft Malware Protection Center blog, the initial route of infection was revealed to be a malicious update to tax accounting software deployed by the Ukrainian company M.E.Doc.
Given the initial attack vector and level of sophistication, the underlying motive appears to be aimed at wreaking the maximum amount of disruption in Ukrainian infrastructure, while merely operating under the guise of ransomware. This suspicion is supported by the absence of a payment portal or functional email address to deliver the ransom payment.
Why it matters
The bottom line is that companies are still failing to adequately secure their IT systems from the EternalBlue vulnerability in the Windows Server Message Block (SMB) server.
Microsoft issued critical security updates to patch this vulnerability on March 14, 2017. To verify that the MS17-010 patch is installed, follow the directions in this Microsoft support article.
If you’d like to learn more about this Petya-based attack, catch the replay of my webinar: Deep Dive into Petya-based & WannaCry Ransomware Attacks.
An interesting tidbit
Our threat researchers have determined that this infection includes a check to see if a file named “perfc” or “perfc.dat” exists in the Windows root directory before executing (a kill switch of sorts). Of course, the best “kill switch” is to perform updates that patch known vulnerabilities such as EternalBlue.
Cyber News Rundown: Edition 6/23/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
WannaCry Shuts Down Honda Production Plant
Over the last few days, Honda officials have discovered a recurrence of WannaCry across multiple machines around the globe. This reinfection was enough to force the temporary closure of their Sayama plant in Japan. While Honda did implement several patches to ward off the initial attack in May, their efforts may not have been thorough enough, leading to their current predicament. Fortunately, the plant was able to reopen a day later, after the systems had been fully updated and cleaned.
Web Host Pays Out $1 Million Ransom
A South Korea-based web hosting service was recently hit with a Linux variant of Erebus ransomware, which affected over 150 unique servers for thousands of different business clients. While Linux systems haven’t traditionally been desirable targets for ransomware, attacks like this one are steadily increasing as more Linux exploits are discovered. Faced with the prospect of overwhelming fallout, the owner of the hosting company chose to pay the ransom, after negotiating with the attackers for a smaller sum.
NSA Malware Installing Cryptocurrency Miners
As further effects of the NSA leak continue to surface, one NSA hacking tool in particular is being used again as a backdoor to allow remote file execution on infected machines and install a cryptocurrency miner. In addition to using DOUBLEPULSAR—a backdoor that was also used in WannaCry attacks in May—to infect the machine, the Trojan also does a check for CPU usage to determine if the computer is suitable for mining Monero, a newer cryptocurrency that has been gaining market strength.
Mac® Computers Becoming Focal Point for Attackers
As more high-level employees use Macs for their daily operations, cybercriminals have more reasons to focus on Apple products when looking for valuable data to steal. By using service-based malware campaigns, criminals can now target entire networks of systems, rather than individual computers, giving them greater reward for less effort. Fortunately for Mac users, the same security rules for PC still apply: run the latest security updates, always back up your important files, and use some form of third-party security software to cover the remaining attack vectors.
WannaCry Found on Australian Traffic Cameras
In the past week, officials have discovered at least 55 traffic cameras in Victoria, Australia were compromised with WannaCry ransomware after being connected to an infected USB drive. While the cameras have continued to function normally, traffic officials are still monitoring the system to ensure no incorrect traffic citations are issued due to the camera tampering.
Q&A with Reverse Malware Engineer Eric Klonowski
These days, it seems like you can’t turn on the TV or open a news site without reading some terrifying headline related to cybersecurity. And the numbers keep escalating. Yahoo’s breaches impacted 1 billion user accounts. Chipotle’s security incident affected more than 2,500 stores in 48 states. We know what cybercriminals are doing; they’re stealing credentials and laughing all the way to the bitcoin bank. So what are we, the good guys, doing to get ahead of criminals?
That’s where today’s interviewee, Eric Klonowski, comes into play. Eric is a senior advanced threat research analyst, meaning he reverse-engineers malware, at Webroot. He has to think like a hacker to figure out how the bad guys manipulate benign software by literally taking apart, or “unpacking” malware.
Webroot: Let’s start with the basics, Eric. Tell me a bit about yourself?
Eric Klonowski: Growing up, I was a nerd. I liked to take things apart and figure out how they work. At six or seven, I would take apart landline phones just to see what was inside.
This was my start as a reverse engineer. Even now, I like to disassemble random software to see what makes it tick.
On any given day, 90 percent of what I think about is related to security, malware, computer science, and engineering. It’s my passion. Perhaps I need to get outside more, but generally, security is what I think about.
I’m not surprised by your “focus” on the industry. I think your field requires that level of passion and commitment. Besides, nerds are cool nowadays, thanks to the Mark Zuckerbergs of the world. How did you make the leap from deconstructing phones to reverse engineering?
Probably not a shocker to anyone who has read this far, but I was a mischievous child. I remember going on a family trip when as a kid, and I spent the entire time on my laptop following Russian tutorials on how to crack software. I loved that complex software protections could be reduced to a simple byte.
I kept teaching myself from there, and that naturally evolved to looking at more in-depth, sophisticated software. Malware is particularly interesting to me because it is level 10 difficult as far as puzzles go. A malware author’s entire goal is to fool reverse engineers like me.
The problems I face are not traditional computer science problems that are covered in textbooks. They tend to be non-traditional, and without getting too far into the weeds, they are unique problems you won’t find at other organizations.
So how did you hear about Webroot?
I was perusing an online job search site and got an ad. Being a malware-oriented techie, I was aware of Webroot.
At the time, I was working as a government contractor, and I was interested in getting into the commercial world—something that doesn’t require clearance.
I don’t know, that sounds pretty cool!
It was an awesome opportunity. I started as an intern, which is key for getting your foot in the door anywhere, and it soon turned into a full-time job. But I wanted to be able to discuss my work and be more involved in the threat community.
That makes sense. What does a day in the life look like for you?
The majority of the time, I’m really excited to come into work. I know there are interesting problems waiting for me to dissect. The problems I face are not traditional computer science problems that are covered in textbooks. They tend to be non-traditional, and without getting too far into the weeds, they are unique problems you won’t find at other organizations. They aren’t algorithm or mathematically driven, but related to questions like, “how can I manipulate the nature of the software already running on the system?”
I also interface with almost every engineering team and multiple departments. It gets me out of my shell.
What lessons have you learned from working for a few years?
Absolutely everyone has something to offer. In school, we tend to segregate into specific engineering groups and form bias. Even working with people like you (public relations career shout out!), there tends to be a distancing at first because you don’t understand each other’s roles.
But we all have something to offer, and we are all good at what we do. I have something to learn from everyone at this organization.
That’s a great life lesson, Eric. Switching the focus to students, any advice for hopefuls in your field?
This is the kind of job where you need to be passionate about figuring out how things work. You may want to do something good for the world, and this is one way to do that. But if you’re the kind of person who walks by the puzzle store at the mall and thinks, “those look cool, I wonder how they work,” this is the kind of job you would find interesting.
Full disclosure: this is not just a 9-to-5 job. I find myself thinking about these problems all the time.
What about professionals looking to get into reverse engineering? There have been a lot of conversations around re-training traditional IT staff to fill the many cyber roles available.
I think people who have a solid network or security background could make the transition, if they are passionate enough about the field to teach themselves. This isn’t something you will pick up by shadowing a co-worker for a few days or reading a single book. You need to roll up your sleeves and dig into online forums, webinars, courses, and you need the drive to keep learning.
That’s the truth! It reminds me of my favorite quote from Mahatma Gandhi, “Live as if you were to die tomorrow. Learn as if you were to live forever.” Thanks for taking the time to chat, Eric.
If you’re interested in a job at Webroot, check out our careers page, www.webroot.com/careers.
Is Your Chat Client Leaving You Exposed?
Popular third-party chat platforms like Slack, Discord, and Telegram are just a few of the many new productivity applications that are being hijacked by cybercriminals to create command-and-control (C&C) communications infrastructures for their malware campaigns. As corporate security teams become more aware of traditional malware threats and deploy new security solutions to defend against them, cybercriminals continue to innovate. Now they’ve turned to well-known chat and social media applications as platforms to communicate with their deployed malware.
Hiding in Plain Sight
The appeal of these chat programs for cybercriminals is born from the fact that many of them are free, easy to use, and incorporate application programming interface (API) components that simplify connections between the programs and custom-built applications. It’s this use of APIs that allows hackers to operate undetected on corporate networks. This clever technique enables hackers to entrench their access by camouflaging themselves with normal data flows. Plus, because this malware leverages software platforms and services that are readily available (and free), all hackers need to do in order to stay connected to their growing malware bot farm is set up an account on their chat platform of choice.
Granted, not all software using APIs is susceptible to this type of attack. However, these attacks are a clear demonstration that tools used by project management and software development teams can be compromised in ways that expose their organizations to significant risk. I predict that similar vulnerabilities in productivity services and applications used by corporate technology teams will continue to be exploited—at an even greater rate. In many ways, these attacks mirror what we’ve seen recently targeting core protocols that operate on the Internet.
Know Your Enemy
Luckily, knowing the enemy is half the battle. With this in mind, we can manage these types of threats, and some of the steps I recommend come down to basic cyber hygiene. I highly recommend security professionals deploy an antivirus solution that incorporates anti-malware and firewall services to all endpoints. A solid threat-intelligence service is also vital to educate security staff and business stakeholders on the current threats and threat actors targeting their business.
One final point: it’s a good idea to screen all outbound network traffic in order to verify that it’s going to legitimate destinations. Hopefully, you’ve already deployed these recommended security controls. If you are missing one or more of these elements, it’s time to shore up your cybersecurity efforts to protect yourself and your organization.
Cyber News Rundown: Edition 6/16/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
New Mobile Phishing Attacks are Using URL Padding
In an attempt to trick mobile browsing users into accessing malicious sites, attackers have begun adding multiple hyphens to URLs that keep the false address out of the mobile browser’s small address bar. This “URL padding” has even been spotted targeting high-traffic sites such as Facebook and Craigslist, to increase criminals’ chances of stealing user login credentials. We strongly recommend that users enter the desired URL manually, rather than clicking links, while also trying to maintain the same security standards for their mobile devices as for PCs.
Airline Traveler Data Remains Unsecured
While physical security around air travel has greatly increased over the last decade and a half, the data security of the nearly 8 million travelers is still at risk. The trouble stems largely from antiquated airline systems in general, which are currently exempt from the current Payment Card Industry Data Security Standards that are compulsory for all other online-sales industries. For the sake of airline travelers everywhere, we hope these systems will soon receive the updates they so desperately need to keep passenger and employee data safe.
Mazda Cars’ Infotainment Systems are Totally Hackable via USB
Over the past several years, many Mazda owners have been modifying their car’s entertainment systems using USBs that are pre-loaded with a specific code that allows high-level access to the system. While your imagination could run wild with the cybercriminal possibilities, for the time being, the code only operates when the car is running. This minor defense mechanism stops attackers from accessing the car remotely. The initial USB vulnerability has been well documented since the 2014 model year, so it’s somewhat surprising that it hasn’t been exploited further.
London University Hit with Ransomware
Within the last week, officials at University College London have been attempting to discover the origin of an attack that left large portions of their networks encrypted. It’s likely it began with a phishing email which then propagated throughout the university’s shared networks over the next couple of days. Fortunately for students and staff, it appears the encrypted data was securely backed up and will be used to restore the file structures once the infection is fully removed.
Dark Web Service Offers SS7 Access for Cheap
Recently, a service has popped up on the Dark Web that would give several functionalities to anyone interested in tracking or monitoring any smart device. The service offers several different levels of monitoring, ranging from a basic report on a specific device to full tracking and message interception (for a larger fee, of course). While the exact method used to access these networks is still unknown, the manager of the service claims that it is surprisingly easy, even with all of the security and prevention techniques today’s telecom providers use.
Webroot Web Threat Shield: Enhancements to better protect your endpoints
Webroot SecureAnywhere® Business solutions will now give admins more ease of control within the Global Site Manager (GSM). From web overrides to Mac- and PC-specific enhancements, we’re delivering new features you asked for to ensure the best multi-vector protection possible.
Webroot protects endpoints against myriad threats at multiple attack stages spanning a variety of attack vectors. One way we do that is through Web Threat Shield evaluating the risk of a given website based on its history and association with other internet objects, i.e., its reputation.
Enable Web Overrides
We’ve released a GSM Console update giving admins the ability to configure create overrides on the default blocking behavior of Web Threat Shield. This ability to whitelist certain websites will give admins greater control and customization over which sites are allowed, in the event that a particular site with a lower reputation score is necessary to complete certain business tasks.
Mac-Specific Changes
An improvement you can expect to see over the coming weeks will be managing Mac endpoints via policy. Updating the Web Threat Shield browser plug-in for Mac is an important first step towards providing more similar experiences across Mac and Windows platforms.
Please notify your clients of this update
Due to security measures specific to Mac browsers, your clients may receive a message when the browser extension updates. When agents receive the update, the Safari and Chrome browsers will launch themselves. Safari will ask the user to indicate they trust the updated browser extension, while Chrome’s message will be purely informational and can be closed without further action. Firefox will wait until the user launches it to throw a notification for the new browser . View a video of the anticipated user experience here:
PC-Specific Changes
Throughout June and July 2017, Windows endpoints will also receive an update. The update will be largely silent; however, individuals with older versions of Firefox will experience a pop-up.
Based on customer feedback, we’ve reduced the number of risk levels from five to three. The new categories will be Trustworthy, Suspicious, and High Risk. Additionally, we will no longer block specific categories (e.g., “proxy”), and will instead block by reputation only. Finally, we will provide more straightforward explanations for why websites have been blocked.
To learn more about these updates, visit the following update bulletins:
Cyber News Rundown: Edition 6/9/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
Internet Cameras Showcase Major Security Flaws
Researchers recently discovered as many as 18 different vulnerabilities with Foscam cameras. Among the exploits are several methods of gaining remote access to the cameras, as well as viewing active feeds, and searching through locally stored files. Although the researchers reported these issues months ago, the manufacturer has not yet addressed the issues. Unfortunately for consumers, Foscam makes devices for at least 14 different brands, all of which come with the same security risks.
EternalBlue Exploit Port to Windows 10
The notorious EternalBlue exploit, which was used in the WannaCry attacks, has been ported to Windows 10, which means all current versions of Windows are susceptible to the exploit, if not properly patched. In addition to the port, another exploit module was created, which slims down network traffic and allows the infection to remain undetected by current detection criteria. While researchers are still learning and understanding the full capabilities of EternalBlue, it has also opened the door for less skilled hackers to modify the otherwise well-written exploit for their own purposes.
Car Owner Database Publicly Available
In the last week, researchers found a publicly-facing database containing the customer and vehicle information for nearly 10 million cars in the US. The database, which had been actively available for around four months, has no known owner, though several dealerships named in the database have been contacted with inquiries. Unauthorized access to the information could give criminals more than enough information to have extra keys made for the vehicles, and could even lead to identity theft issues.
Turla Hacking Group Changing Methods of Attack
The cybercriminal group Turla has executed numerous cyberattacks on major corporations and government agencies over the last few years. Now, however, they’ve switched their focus to individual attacks, typically using Firefox browser extensions to create backdoors into personal systems. The attacks are coordinated by placing comments on highly-trafficked Instagram pages and pictures. The browser extension hashes the comment values until the malicious hash is discovered, at which point it contacts a C&C server for instructions. Fortunately for many social media users, the APIs used to create the malicious extension will be phased out in future versions of Firefox.
Edmodo Data Breach Confirmed
Officials at Edmodo, an education technology company that works with K-12 schools and teachers, have been working to discover the source of a breach that affects over 77 million individual accounts. The majority of affected users were children who used various Edmodo programs for school, as well as educators across the country. Although the freshness of the data would indicate that the breach occurred very recently, and Edmodo did attempt to notify its users quickly, not all users received word that their accounts had been breached. Thankfully, the company used strong encryptions to protect passwords, so it’s unlikely that attackers will invest the time and effort necessary to decrypt them to access accounts.
Talking DNS Protection with ConnectWise
It’s been an exciting week for our partner ConnectWise – they started offering customers Webroot® DNS Protection. To get insight into why this matters, I sat down with George Anderson, Webroot’s product marketing director for business solutions, and Gavin Gamber, vice president of Channel Sales and Alliances at ConnectWise.
Can we start with the basics? What is DNS?
George: DNS stands for Domain Name System. The basic job of DNS is to turn a human-friendly domain name like webroot.com into an Internet Protocol (IP) address like 66.35.53.194. Computers use IP addresses to identify each other. When a user accesses an external website or downloads files, their computer uses a DNS server to look up the domain name and then directs the user to that website.
Ok, kind of like a phone directory for the internet. That helps me understand the power DNS can hold.
George: That’s right. DNS is a powerful part of making the internet work. It also can be an equally powerful avenue for protecting a business. According to our data, many infections are generated through web browsing. Implementing web filtering security at the DNS layer can have a very significant impact on infection rates.
Wow. The internet is a big, beautiful, and scary place.
George: It can be. Using the internet is a high-risk activity for every business, regardless of size. Sometimes good sites can contain bad content. Users can fall victim to drive-by ransomware, employees can click on malvertising, and the list goes on.
Can you give us an example of what security at the DNS layer can stop?
Gavin: Let’s say, for example, you work with medical clients. Most of the end users are protected, but when guests come onto the network there is no way to monitor their web traffic. Since you don’t control the device, you don’t have any antivirus protecting the guest’s endpoint. With DNS filtering, you can protect the network and prevent guests from knowingly or unknowingly going to harmful or sensitive websites.
George: Using a web filtering solution at the DNS layer lets businesses do a few things. First, it creates policies for web usage that can be applied globally or by client. An MSP can decide, for example, whether to block certain content or social media sites. Second, it filters URLs for security risks, preventing infections by automatically sifting out known malicious websites. Finally, it allows a partner to monitor overall web usage and its security risk posture. What’s really different is that this all happens outside the network at the domain layer, so most infections are stopped at the earliest possible stage.
In a nutshell?
George: DNS Protection allows organizations to configure their router or firewall to point to Webroot’s secure DNS resolver servers for granular web filtering. Then, partners simply configure an acceptable internet usage policy. By doing so, they can block malicious URLs, restricted content, social media, or streaming sites they don’t want employees perusing at work.
ConnectWise, what are you hearing from partners about web filtering and its need?
Gavin: This is just one more layer of end user security that is typically time and labor intensive to set up. Our partners and their clients want to mitigate all attack vectors whether they manage all the devices on the network or not. As security risks persist, this is a must-have tool.
So what will all this mean for our ConnectWise partners?
George: First and foremost, it’s simple and easy for ConnectWise partners to deploy and manage. The new DNS Protection service has been fully integrated into the same Global Site Manager (GSM) console they use today for Webroot’s endpoint security. It also benefits from the same pillars of Webroot’s other security services.
- No hardware or software to install
- Includes robust reporting options for easy management
- Direct benefits from Webroot BrightCloud Web Classification Service
ConnectWise, why are you excited for this new product?
Gavin: When we first saw Webroot SecureAnywhere DNS we were blown away by the ease of use and straightforward deployment. Our initial reaction was that our partners would find this incredibly valuable. Additionally, this really leverages the threat intelligence that Webroot has collected over the years and gives that control to our partners in a very powerful and consumable product.
Thank you, both. Glad we could chat all things web filtering.
Interested in learning more? We have additional resources. You also can discover everything Webroot is doing with ConnectWise at Automation Nation, June 19-21 in Orlando, FL. Visit us at booth #201, where you can see a demo of DNS Protection.
Cyber News Rundown: Edition 6/2/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
Hackers Blackmail Surgery Patients
Hackers have begun contacting victims of a March data leak that exposed a database containing photos and other sensitive patient information. The majority of victims are linked to a Lithuanian cosmetic surgery clinic, and have received demands ranging from $40 to a full Bitcoin to prevent their photos from being released. Unfortunately for some of the patients, at least 25,000 photos have already been published, likely in an attempt to incite other ransom victims to pay.
Chipotle Payment Systems Hacked
Over the past few months, officials have been sorting out the severity of the Chipotle data breach that occurred between March and April of this year. As of the most recent statement, restaurants in 48 US states have been affected. The data that has been compromised consists of customer names and credit card information, but the company is working with multiple banks to assist any impacted customers.
Judy Malware Wreaks Havoc on Google Play Store
In the past week, Google has removed over 40 apps from the Play Store that were infected with “Judy” malware. Most of the apps were available in the store for quite some time, meaning the number of affected users could be in the millions. Fortunately, Google has recently released a new service that will continuously scan Android® devices for any malicious activity.
Phishing Study Reveals Interesting Results
A recent study conducted by Ironscales monitored 500,000 unique mailboxes from 100 different companies. The study revealed that, over the course of nearly 8,500 attacks on the boxes, many focused on only a small percentage. Additionally, nearly 80% of phishing attacks were able to bypass the email filter and remain undetected, while those with more brand-oriented themes were caught almost immediately. It also pointed out that, while less than half of these attacks lasted longer than 24 hours, the ones that made it past 30 days were capable of sustaining themselves for up to a year or more.
Game Hackers Mod Nintendo Game Cartridges
While the practice of hacking games is nothing new, several hackers in the community have found a way to create a full Hex editor within Super Mario World, using nothing more than standard controller inputs. By jailbreaking the cartridge to store user-written data in the small game save files, they have been able to mod the game, giving players a wide variety of special perks, and even changing the color schemes of game levels.
Webroot CTO Hal Lonas on Rethinking the Network Perimeter
“What are our cybersecurity protocols?” This question is one that has, undoubtedly, been top of mind for CTOs at numerous corporations and government agencies around the world in the wake of recent ransomware attacks. Given the hundreds of thousands of endpoint devices in more than 150 countries that were infected in the latest global attack, WannaCry, can you blame them?
Cybersecurity stock buying trends are on the rise. According to CNN Money, the PureFunds ISE Cyber Security ETF (HACK), which owns shares in most of the big security companies, was up more than 3 percent in early trading the Monday following the first WannaCry attacks. Positive performance in cybersecurity stocks comes as no surprise as organizations shore up their defenses in preparation for future attacks—big or small. This is the security climate in which we live.
While the numbers have been rising on both fronts, do the affected organizations truly understand what to look for when addressing cybersecurity? Where should the protection start? What obstacles might organizations need to overcome? How can they be better prepared?
Hal Lonas, chief technology officer at Webroot, takes us beyond the sobering wake-up call that attacks like WannaCry bring, and discusses actionable advice companies should consider when fortifying systems against cybercriminals.
Where should an organization start when thinking about combating malicious files entering the network?
Organizations should think about their security in terms of layers. Between the user sitting in the chair and the sites and services they access from their workstations, every level of security is equally important. The vehicles malicious files use to infiltrate the network shouldn’t be ignored either. Is it a URL? Is it a USB key that’s physically carried into the office? Or maybe it’s an employee who takes their laptop home and uses it on an unsecured network—the possibilities are endless. We’re in a very interesting era in which mobility has become the norm, there are more internet-connected devices than ever, and there are more angles every day for cybercriminals to launch attacks. Essentially, the perimeter is dissolving. That means organizations need to rethink how they approach protecting their networks.
We’ve heard the term “dissolving” a number of times recently when talking about the traditional notion of the network. Can you speak more on that?
Let’s use my phone as an example. Right now, it’s connected to the secure employee wireless in this office. When I hit the coffee shop later for a meeting, it might be on their public Wi-Fi. While I’m driving to the airport this afternoon, it’ll be on a cellular network. By tonight, it’ll be on the guest Wi-Fi in a hotel. With each movement and interaction, perimeters converge and overlap, and this phone is exposed to different levels of security across a variety of networks. Each step means I’m carrying data that could be exposed, or even malware that could be spread, between those different networks. These days, company work happens everywhere, not just on a corporate computer within the security of an organization’s firewall. That’s what we mean by dissolving perimeters.
We’re in a very interesting era in which mobility has become the norm, there are more internet-connected devices than ever, and there are more angles every day for cybercriminals to launch attacks.
One line of defense is endpoint protection. Whether you’re using a mobile device or laptop, that protection goes with the device everywhere. Even as you switch between networks, you know that’s one layer of protection that’s always present. Network or DNS-level security is also key, to help stop threats before they even make it as far as the endpoint.
How does Webroot BrightCloud® Streaming Malware Detection fit into the layered approach? Is it cutting edge in terms of protecting against malicious files at the perimeter?
Streaming Malware Detection is pushing the boundaries of network protection. As files stream through network devices—i.e., as they’re in the process of being downloaded in real time—Streaming Malware Detection determines whether the files are good or bad at the network level. That means the solution can analyze files in transit to stop threats before they ever land on the endpoint at all. We partner with the industry’s top network vendors, who have integrated this and other Webroot technologies as part of their overall approach to stopping malicious files at the perimeter.
In terms of what we’re doing with Webroot products, we’re expanding the levels in which you can be protected—looking at more and more different aspects of where we can protect you. We’re tightening the reigns from endpoint protection, which we’ve traditionally done extremely well, and branching further into the network with Streaming Malware Detection, as well as network anomaly detection with FlowScape® Analytics. We aim to bring value to our customers by protecting holistically. We’re adapting as a company with our product offerings to this new reality we find ourselves in.
What cutting edge approaches is Webroot taking to combat what has already infiltrated the network?
We hear a lot about advanced persistent threats. The reality is that those long-resting, largely undetected threats do make their way through and land in an environment with the intention of wreaking havoc, but doing it low and slow to avoid detection. The malware authors are very smart, which is something we try to anticipate. Webroot is really good at a couple of different things, not least of which is that we’re incredibly patient on our endpoint products. Essentially, we’ll monitor something that’s unknown for however long it takes, journaling its behavior until we’re absolutely sure it’s malicious or not, and then handling it appropriately.
In addition, we’ve recently added a product that does the independent network anomaly detection I mentioned earlier: FlowScape Analytics. Essentially, it analyzes day-to-day activity within a network to establish a baseline, then if something malicious or abnormal happens, FlowScape Analytics instantly recognizes it and alerts us so that we can track it down. In conjunction with our other layers of protection, it’s a solid cybersecurity combination.
What technology do you see helping to protect networks at the same scale and velocity threats are coming?
Streaming Malware Detection is a big one. Traditionally, malware has been sent into a sandbox where it has to execute and takes up resources. The sandbox also has to simulate customer environments. This approach comes with a lot of complexities and ends up wasting time for customers and users while awaiting a response. For scalability, analyzing the malicious files in transit at network speed frees up time and resources.
Is there anything else organizations should take into consideration? Machine learning at the endpoint level?
We’re always asking ourselves, “where’s the right juncture to layer in more security?” I’d like to see more organizations asking the same. You can look at our history, during which we developed a lightweight agent by moving the heavy lifting to the cloud, and that’s the theme we’ll continue to follow. The detection elements of machine learning can fit on our client, but we’ll do the computing-intensive and crowd protection work for machine learning in the cloud. That gives you the best efficacy, shares threat discoveries with all of our products and services in real time, and keeps devices running at optimal levels.
Cyber News Rundown: Edition 5/26/17
The Cyber News Rundown brings you the latest happenings in cyber news weekly. Who am I? I’m Connor Madsen, a Webroot Threat Research Analyst, and a guy with a passion for all things security. Any more questions? Just ask.
Samsung’s Latest Iris Scanners are Easily Fooled
Recently, ethical hackers have been able to bypass Samsung’s latest attempt at iris recognition with minimal effort. Would you believe the tech is fooled by simply scanning a high-res picture of the right pair of eyes? While the vendor who supplies Samsung with the recognition software assures users that their security is infallible, the opposite seems to be true. The group that discovered the hack was also responsible for finding the workaround for Apple’s Touch ID locking system.
University Twitter Account Hacked, Tweets Racist Remarks
Unfortunately, Salem State University in Massachusetts has joined the ranks of notable organizations, institutions, and individuals who have fallen victim to social media hacks. In the past week, officials at Salem State having been dealing with the aftermath of a hack that caused their Twitter account to post highly offensive, racist messages. For the time being, the account has been suspended, the tweets in question have been deleted, and the university has issued public apologies through all regional means.
Tech Support Scammers Using WannaCry to Leverage Payment
While tech support scams aren’t new, it seems that scammers are now shifting their tactics to use cyberattacks that have made the news as an extortion tool. After launching an annoying popup that informs victims of their (fake) WannaCry infection, the scammers prompt users to call the (fake) support number for assistance. They then demand an outrageous payment just to run the free Microsoft Malicious Software Removal tool.
Yahoobleed Vulnerability Leaks User Data
Security researchers have been warning Yahoo! about its numerous security vulnerabilities around user data for years, and have gotten only silence in response. The flaw comes from ImageMagick, an image processing system used by Yahoo, which didn’t receive a crucial patch that was released in early 2015. This flaw allowed criminals to send an email containing a malicious image file which, once opened, would enable the end user access to Yahoo! server information. Rather than patching the bug that cybercriminals could exploit, Yahoo! simply discontinued using ImageMagick.
Bank Biometrics Bypassed by Twin Brother
Recently, a reporter for the BBC discovered that his HSBC bank credentials could be falsified by his non-identical twin brother using the voice-recognition password system. The system allowed the reporter’s brother no fewer than 8 attempts to correctly match the voice patterns necessary to access the account, though it only offered him limited viewing access. HSBC has stated that they will decrease the number of failed attempts allowed, and will work to add more layers of security.