A peek inside a boutique cybercrime-friendly E-shop – part five
Seeking financial liquidity for their fraudulently obtained assets, novice cybercriminals continue launching new DIY cybercrime-friendly e-shops offering access to compromised accounts, harvested email databases, and accounts that have been purchased using stolen credit card data, in an attempt to diversify their portfolio and, consequently, increase the probability of a successful purchase from their shops.
In this post, I’ll profile one of the most recently launched cybercrime-friendly e-shops, continuing the “A peek inside a boutique cybercrime-friendly E-shop” series.
More details:
Malicious ‘Security Update for Banking Accounts’ emails lead to Black Hole Exploit Kit
Cybercriminals have recently launched yet another massive spam campaign attempting to trick e-banking users into thinking that their ability to process ACH transactions has been temporarily disabled. Upon clicking on the link found in the malicious email, users are exposed to the client-side exploits served by the Black Hole Exploit Kit.
More details read more…
Phishing For Bank Account Information
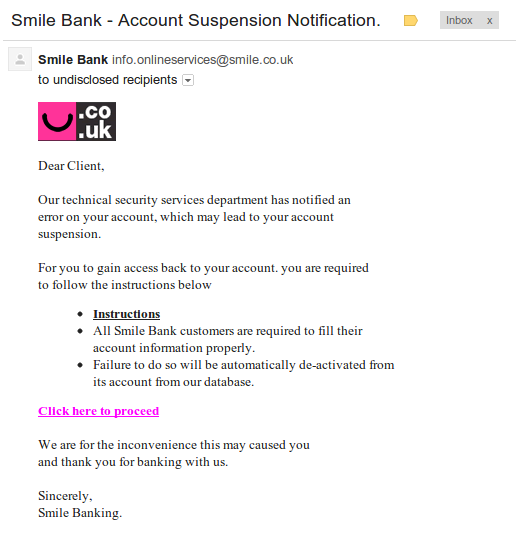
When you’re a threat researcher, you are always on the look out for anything that looks ‘phishy’, even if it’s on your own personal time. Today, I opened my personal email to find this:
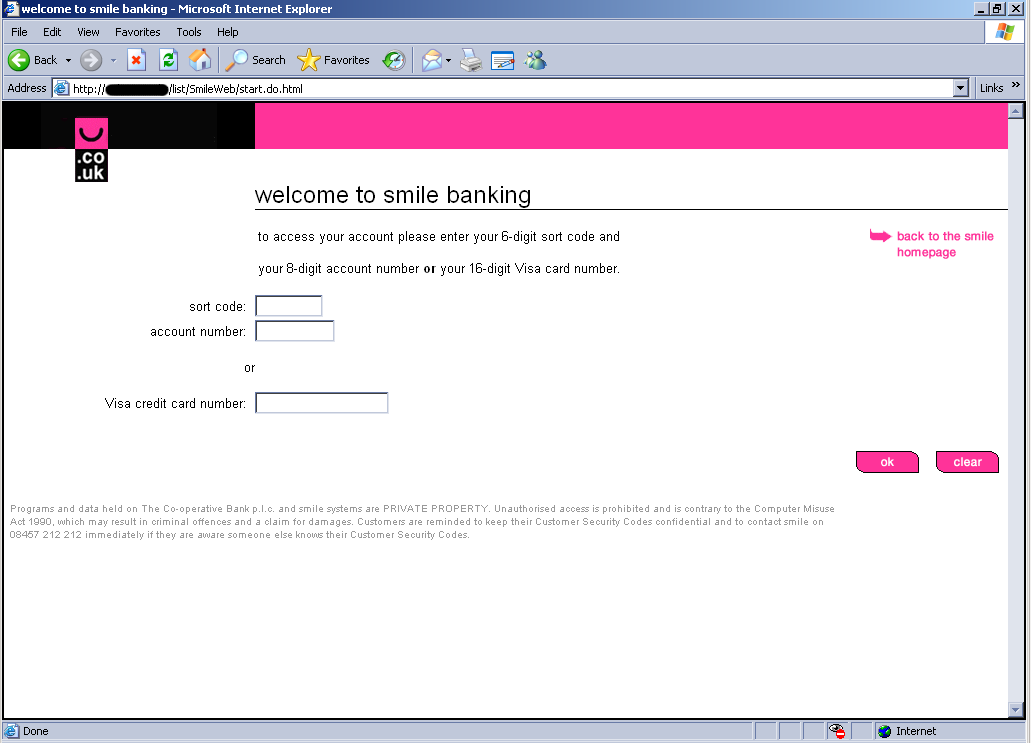
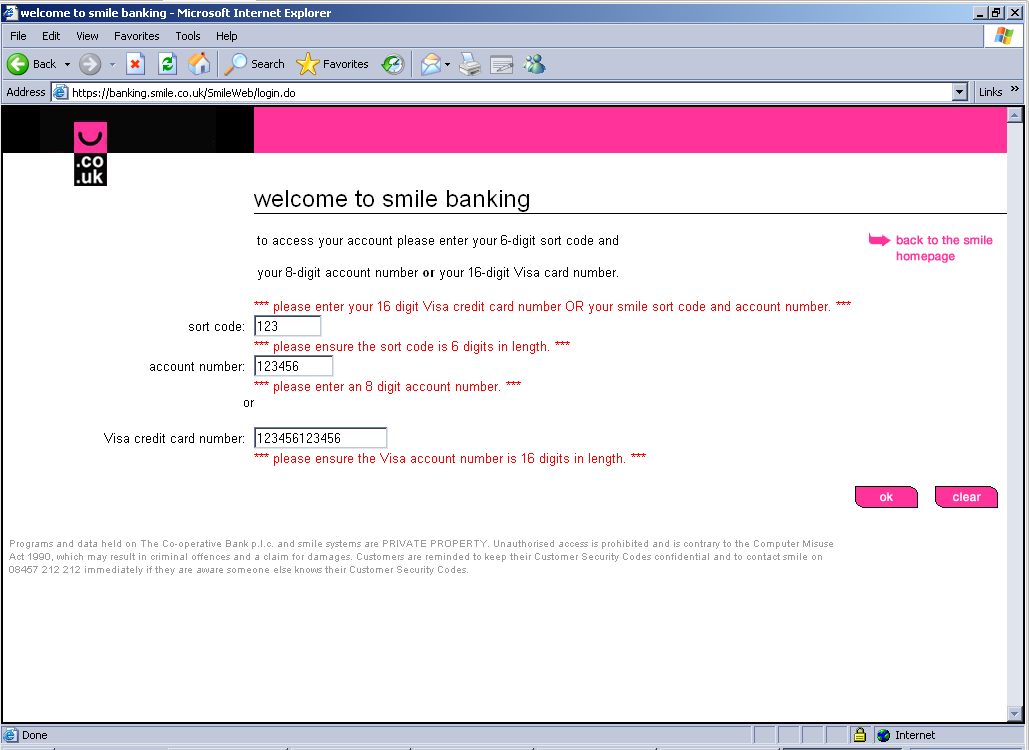
Although the email looked very convincing, I don’t bank with Smile Bank so I knew something was up. Smile Bank is an actual bank based in the UK. The bad guys used a spoofed email address to make it look like it came from the legit Smile Bank domain smile.co.uk. If someone did bank with Smile Bank, I can see how they could easily be tricked. It’s the “Click here to proceed” link that gives the bad guys away. The link goes to a page hosted by pier3.hk, which is a legitimate domain, but appears to be compromised with a simple HTM page that is a redirect to the real malicious site. The redirect sends you here:
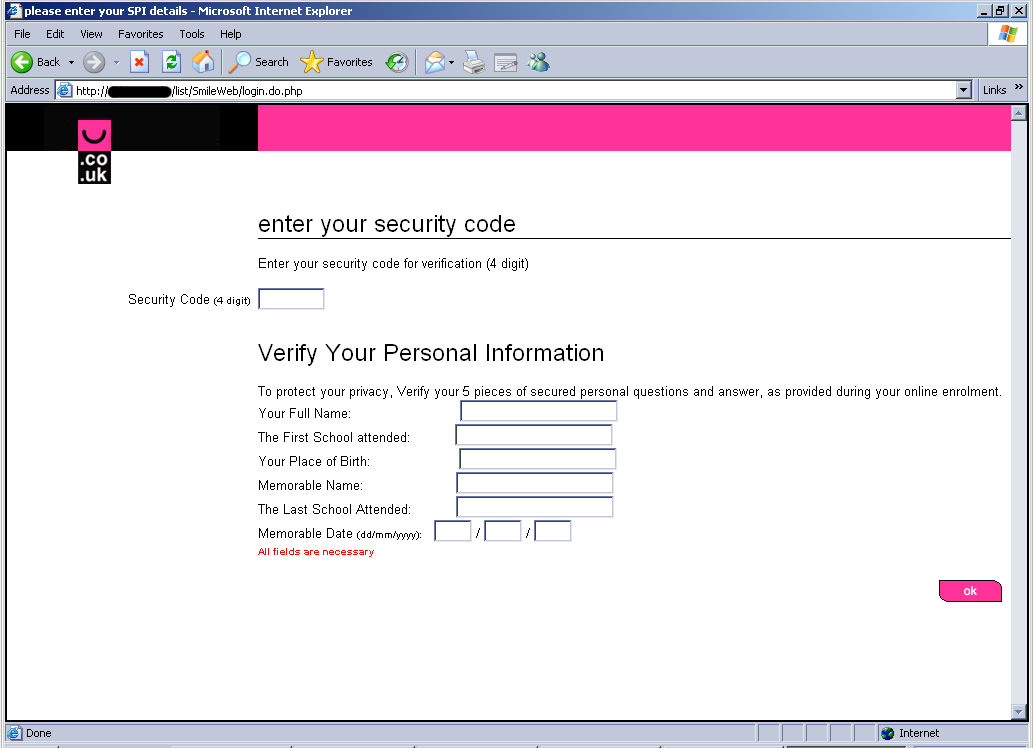
Once filled in and submitted, it then sends you here:
When this page is filled in and submitted, it sends you to the legitimate Smile Bank site:
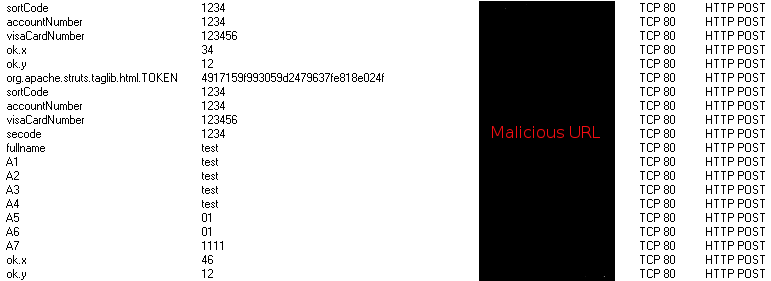
In the background, I captured the network traffic to discovery all the input I entered being sent in plain text to the malicious URL:
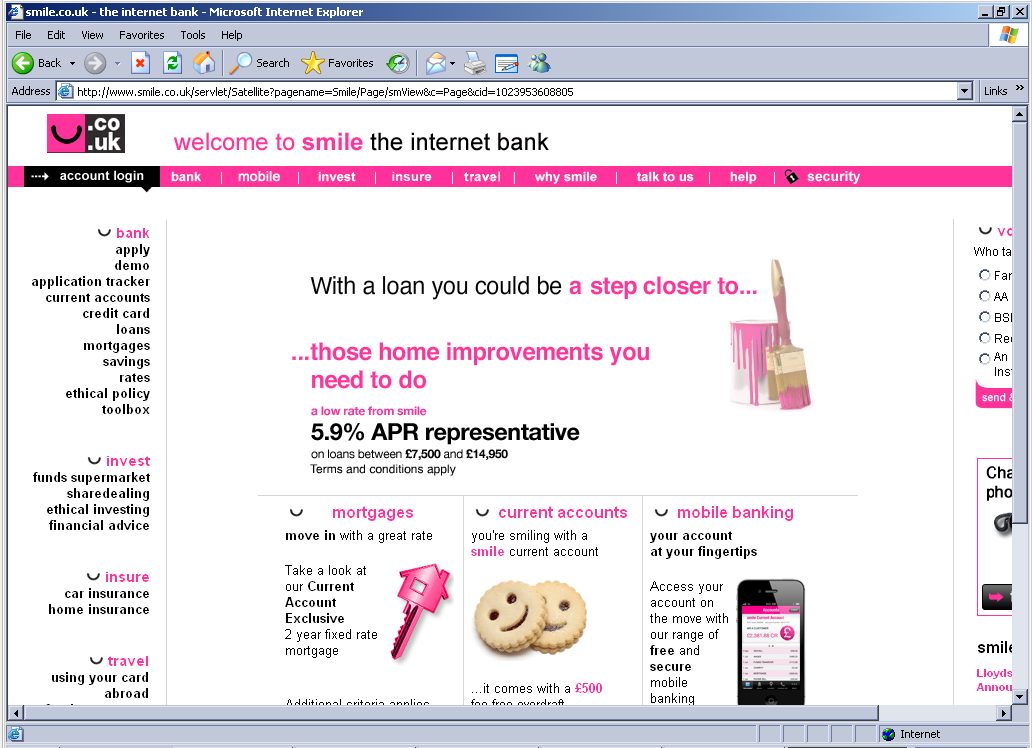
In comparison, I went to Smile Bank’s real login screen. It was identical except for the fact it didn’t accept my nonsense for inputs:
This trick could easily be done with any large bank. Make sure to always be suspicious of any email claiming to be from your bank that threatens your account has been locked and insists that you need to enter your account information. Also, if the link to enter your account information isn’t to the URL of the bank it claims to be from, you know it’s malicious.
Bogus ‘Facebook Account Cancellation Request’ themed emails serve client-side exploits and malware
Facebook users, watch what you click on!
Cybercriminals are currently mass mailing bogus “Facebook Account Cancellation Requests“, in an attempt to trick Facebook’s users into clicking on the malicious link found in the email. Upon clicking on the link, users are exposed to client-side exploits which ultimately drop malware on the affected host.
More details:
Fake ‘FedEx Tracking Number’ themed emails lead to malware
At the end of October, a cybercriminal or group of cybercriminals launched three massive spam campaigns in an attempt to trick users into clicking on a deceptive link and downloading a malicious attachment. Upon execution, the malware phones back to the command and control servers operated by the party that launched it, allowing complete access to the infected PC.
This time they didn’t try impersonating USPS, UPS or DHL, but FedEx.
More details:
DIY malicious domain name registering service spotted in the wild
Security researchers and security vendors are constantly profiling and blocking the malicious operations launched by organized crime groups on the Internet.
In an attempt to increase the life cycle of their malicious campaigns, cybercriminals rely on a set of domains hosted on bulletproof servers. In addition to this tactic, they also rely on fast-fluxing, a technique where a domain’s IP automatically rotates on a specific time interval, with IPs from the botnet’s infected population — state of the art bulletproof hosting in a combination with cybercrime-friendly domain registrar.
In order to make it even harder for the security community to disrupt their campaigns, cybercriminals also implement the random domain name generation tactic. This makes it more difficult for researchers to assess and shut down their operations, as of all the randomly generated domains initiating “phone home” command and control server communications, only a few will actually respond and will be registered and operated by the cybercriminals behind the campaign.
In this post, I’ll profile a recently launched DIY malicious domain name registering/managing service which makes it easier for cybercriminals to manage their domains portfolios. The service allows them to register randomly generated domains in mass, instantly change IPs and Name Servers, and cross-reference with anti-spam checklists for verification of clean/flagged IPs.
More details:
Bogus ‘End of August Invoices’ themed emails serve malware and client-side exploits
Cybercriminals have recently launched yet another massive spam campaign attempting to trick users into clicking on malicious links or executing malicious attachments found in the spamvertised emails.
More details:
Bogus ‘Intuit Software Order Confirmations’ lead to Black Hole Exploit Kit
Sticking to their well proven practice of systematically rotating impersonated brands, the cybercriminals behind a huge majority of the malicious campaigns that we’ve been profiling recently are once again impersonating Intuit in an attempt to trick its customers into clicking on links exposing them to the client-side exploits served by the Black Hole Exploit Kit.
More details:
Bogus ‘Meeting Reminder” themed emails serve malware
Cybercriminals are mass mailing malicious emails about a meeting you wouldn’t want to attend – unless you want to compromise the integrity of your computer.
Once executed, the malicious attachment opens a backdoor on the affected host, allowing the cybercriminals behind the campaign to gain complete access to the affected host. Naturally, we’ve been monitoring their operations for quite some time, and are easily able to identify multiple connections between their previously launched campaigns.
More details:
Cybercriminals impersonate T-Mobile U.K, serve malware
Cybercriminals are currently impersonating T-Mobile U.K, in an attempt to trick its customers into downloading a bogus billing information report. Upon execution, the malware opens a backdoor on the affected host, allowing the cybercriminals behind the campaign complete access to the infected PC.
More details:
Cybercriminals impersonate Vodafone U.K, spread malicious MMS notifications
Over the past couple of days, cybercriminals have launched yet another massive spam campaign, once again targeting U.K users. This time, they are impersonating Vodafone U.K, in an attempt to trick its customers into executing a bogus MMS attachment found in the malicious emails. Upon execution, the sample opens a backdoor on the affected hosts, allowing the cybercriminals behind the campaign complete access to the affected PC.
More details:
Bogus DHL ‘Express Delivery Notifications’ serve malware
From UPS, USPS to DHL, bogus and malicious parcel tracking confirmations are a common social engineering technique often used by cybercriminals to trick users into clicking on malicious links or executing malicious attachments found in the spamvertised emails.
Continuing what appears to be a working social engineering tactic, cybercriminals are currently mass mailing bogus DHL ‘Express Delivery Notifications’ in an attempt to trick users into executing the malicious attachment. Once executed, it opens a backdoor on the affected host allowing the cybercriminals behind the campaign complete access to the infected PC.
More details: