The Webroot blog
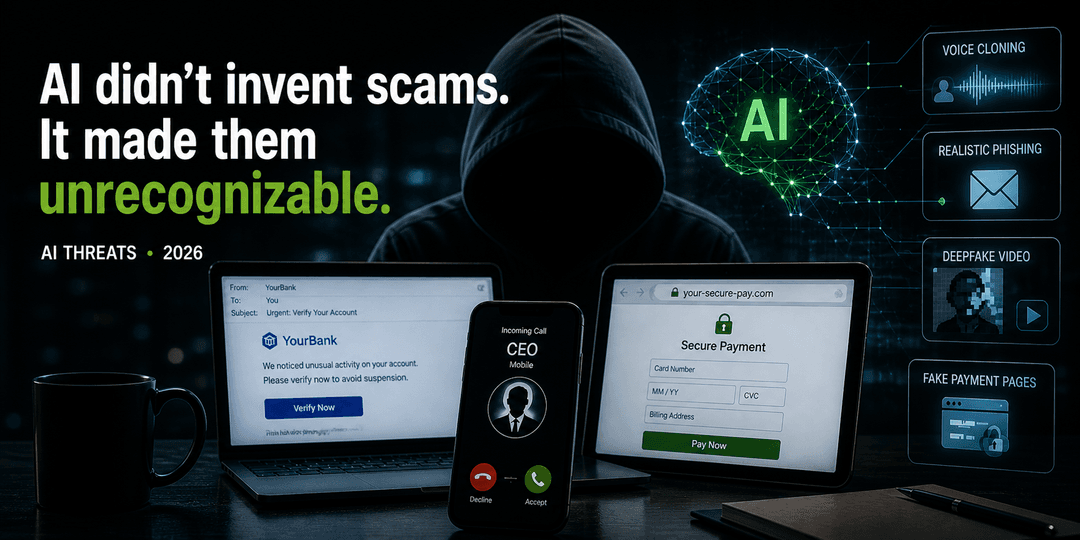
- BlogAI didn’t invent scams—it made them unrecognizableAI-powered scams now look authentic. Learn how modern fraud works, why trust signals fail, and what layered protection actually stops it.CybersecurityFamily SafetyIdentity and Privacy Protection
- BlogGraduation ready: Build a safer digital future with family online protectionHelp graduates protect their identity and devices with family online protection, identity monitoring, and cybersecurity tips.CybersecurityInternet Security
- BlogSpring clean your digital life: A smarter way to stay secureLearn how digital decluttering and Webroot PC Optimizer help keep your devices secure and fast.Digital TipsIdentity and Privacy ProtectionInternet Security
- BlogThe rise of dark AI: How scammers are using artificial intelligence against youArtificial intelligence powers the tools we use every day, from writing assistants to smarter search results.Identity and Privacy ProtectionInternet Security
- BlogLove, trust, and scams: How to protect your identity in a digital worldFebruary is a time for flowers, meaningful connection, and shared moments, but it’s also prime season for scammers to strike.Identity and Privacy Protection
- BlogNew year, new device: The antivirus setup checklist everyone skipsNew devices are often at their most vulnerable in the first days of use, before security is in place—making them an easy target for hackers. If antivirus software isn’t part of your initial setup, you could be opening the door to cyber threats before you’ve even logged in.CybersecurityInternet Security
- BlogGetting and giving respect onlineEarned and courtesy respect hinges on self-respect, how you present yourself, kindness, integrity, and respecting others.Digital Tips
- BlogCell phone theft: How to defend and protect yourselfCombating rising cell phone theft, an FCC initiative aims to disable stolen phones and educate users on security measures.Digital TipsMobile Security
- BlogHoliday scams: The 4 biggest scams to watch for (and how to outsmart them)Your friendly guide to staying safe while shopping, giving, and celebrating online this season.Family SafetyIdentity and Privacy Protection