IRS themed spam campaign leads to Black Hole exploit kit
Recently, cybercriminals launched yet another massive spam campaign, this time impersonating the Internal Revenue Service (IRS) in an attempt to trick tax payers into clicking on a link pointing to a bogus Microsoft Word Document. Once the user clicks on it, they are redirected to a Black Hole exploit kit landing URL, where they’re exposed to the client-side exploits served by the kit.
More details:
Cybercriminals impersonate AT&T’s Billing Service, serve exploits and malware
Cybercriminals have launched yet another massive spam campaign, this time impersonating AT&T’s Billing Center, in an attempt to trick end and corporate users into downloading a bogus Online Bill.
Once gullible and socially engineered users click on any of the links found in the malicious emails, they’re automatically redirected to a Black Hole exploit kit landing URL, where they’re exposed to client-side exploits, which ultimately drop a piece of malicious software on the affected hosts.
More details:
Millions of spamvertised emails lead to W32/Casonline
Thanks to a mature monetization model introduced by vendors of bogus online gambling software, cybercriminals continue mass mailing millions of emails in an attempt to earn revenue for each and every new installation of the promoted software.
In this post, I’ll profile several prolific spam campaigns attempting to trick users into visiting a bogus web site, and downloading a copy of the potentially unwanted application (PUA) most commonly known as W32/Casonline.
More details:
Some Clarification…
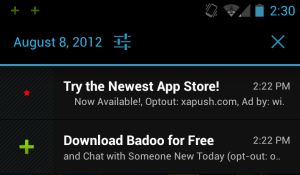
Recently Webroot posted a blog about an app called “London Olympics Widget” which was found in a third party market that may need further clarification. This app is what we consider a Potentially Unwanted Application (PUA). PUAs are apps are not considered to be good, nor are they considered malware either. They are apps that walk a thin line and thus are in a grey area. The app in question was classified as a PUA because the of the advertisement SDK add-ons it contains. There are a lot of free apps out there that contain these advertisement SDK add-ons in order to create revenue, and that’s okay. It’s when these advertisement SDK add-ons are overly aggressive and display behaviors such as creating ad related home screen icons and bookmarks, accessing the contact list, and displaying ads in your notification bar that we call these PUAs. We detect these annoying apps in order to inform the user of its presence. Google has recently taken the same stance against these aggressive advertisements and has updated their Ad Policies to warn developers that this type of aggressive advertising will no longer be allowed in the market: Google Play Developer Program Policies
In the case of “London Olympics Widget”, it is a simple app that displays what events are going on in the Olympics on which days. Nothing wrong with that at all. The reason we have classified this as a Potentially Unwanted Application is because it is using the Olympics to draw people into installing their apps so they can make money on multiple aggressive advertisement SDK add-ons. It is the aggressive advertisement SDK add-ons that are requesting permissions to read contacts, look up device ids, and read SMS messages. Why do they want to read your SMS, collect your contacts and blast you with ads? Probably not to make your mobile experience better. Permissions are a scary thing, but just because an app has a permission to do something doesn’t necessarily mean it’s malicious. It’s the code within the app that uses these permissions that makes the determination of good or bad. Can “London Olympics Widget” read your contacts and read your SMS? Yes, but that doesn’t mean they are using the data collected in a malicious way. They are using the data to for advertisement reasons which isn’t considered blatantly malicious, but is considered something you may not want on your device which is why we detect it as a PUA.
As always, make sure you install apps from safe markets, and if it has more permissions than what you think it should, be cautious. Scanning with Webroot SecureAnywhere Mobile will detect PUAs and malware to make sure users stay ad annoyance free, and safe while using a mobile device.
Ongoing spam campaign impersonates LinkedIn, serves exploits and malware
Remember the LinkedIn exploits and malware serving campaigns which I profiled in March, and May?
Over the past 24 hours, cybercriminals launched the most recent spam campaign impersonating LinkedIn, in an attempt to trick LinkedIn’s users into clicking on the client-side exploits and malware serving links found in the emails.
More details:
Beware of Malicious Olympic 2012 Android Apps
By Joe McManus
There are too many events happening at one time during the Olympics, which might tempt you to install an app for that. But be careful of what you install. Not all apps are what they appear to be. As an example let’s look at the app called “London Olympics Widget”.
More details:
Spamvertised ‘PayPal has sent you a bank transfer’ themed emails lead to Black Hole exploit kit
Sticking to their well proven social engineering tactics consisting of systematic rotation of the abused brands, cybercriminals are currently spamvertising millions of emails impersonating PayPal, in an attempt to trick end and corporate users into interacting with the malicious campaign.
Once the interaction takes place, users are exposed to the client-side exploits served by the Black Hole exploit kit, currently the market share leader within the cybercrime ecosystem.
More details:
Spamvertised AICPA themed emails lead to Black Hole exploit kit
Certified public accountants, beware what you click on!
Cybercriminals are currently spamvertising millions of emails impersonating AICPA (American Institute of Certified Public Accountants) in an attempt to trick users into clicking on the client-side exploits and malware serving links found in the emails.
More details:
Spamvertised ‘Your Ebay funds are cleared’ themed emails lead to Black Hole exploit kit
Cybercriminals are currently mass mailing millions of emails impersonating eBay and PayPal in an attempt to trick end and corporate users into clicking on the malicious links found in the emails. Upon clicking on any of them, user are exposed to the client-side exploits served by the Black Hole exploit kit.
More details:
read more…Russian spammers release Skype spamming tool
Taking advantage of DIY spamming tools and harvested databases of user names, cybercriminals have been systematically abusing multiple instant messaging services in an attempt to trick as many users as possible into interacting with their malicious campaign.
In this post, I’ll profile a newly released DIY Skype spamming tool, discuss its main features, and whether or not it can lead to an increase in the overall spam levels affecting Microsoft’s Skype.
More details:
Cybercriminals target Twitter, spread thousands of exploits and malware serving tweets
Twitter users, beware!
Over the past several days, cybercriminals have been persistently spamvertising thousands of exploits and malware serving links across the most popular micro blogging service. Upon clicking on the clicks, users are exposed to the exploits served by the Black Hole web malware exploitation kit.
What’s so special about this campaign? What’s the detection rate of the malware it drops? Where does it phone back once it’s executed? Have we seen additional malware phone back to the same command and control servers, indication a connection between these campaigns? Let’s find out.
More details:
Spamvertised ‘Download your USPS Label’ themed emails serve malware
Cybercriminals are currently spamvertising millions of emails impersonating the United States Postal Service (USPS), in an attempt to trick end and corporate users into downloading and unpacking the malicious .zip attachment distributed by them.
What’s so special about this campaign? Where is the malicious sample phoning back to? Are there more malware samples that also phoned back to the same command control servers in the past? Let’s find out.
More details: