by Blog Staff | Oct 31, 2011 | Industry Intel, Threat Lab
By Mike Johnson
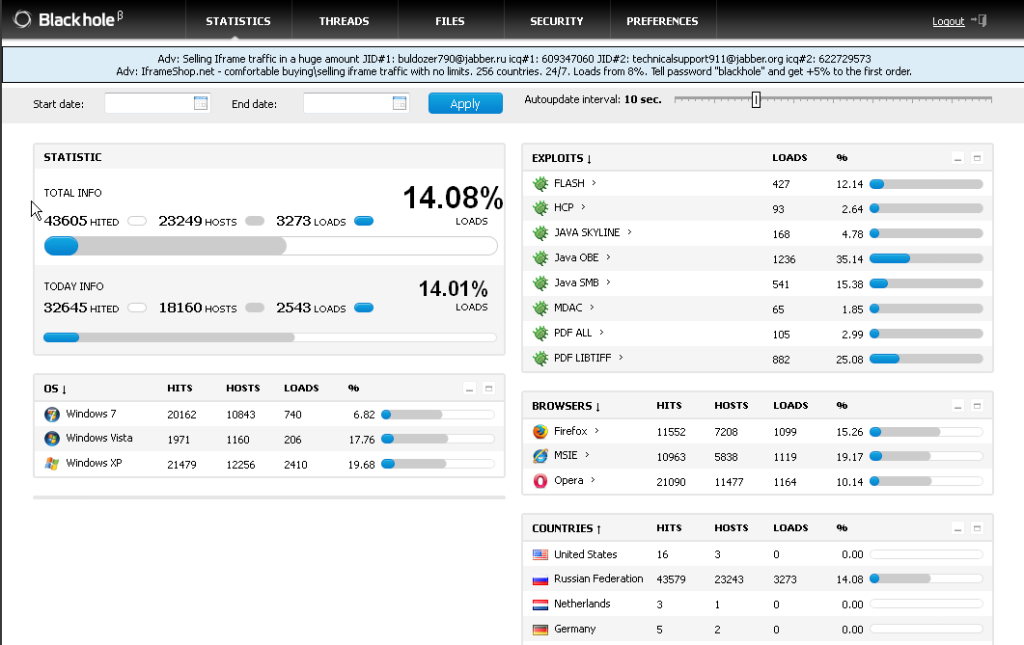
Several weeks back, I was presented with a group of snapshots from an active BlackHole Exploit Kit 1.2 Control Panel.
As with other toolkits I’ve seen in the wild, this one has all the makings of some real bad medicine. The authors have yet again gone to the trouble of making this toolkit incredibly easy to use and widely available for a price. Just a little unsavory web hosting in a country with few or no diplomatic relations and off to the races they go.
It appears this toolkit is configurable in both Russian and English, making one wonder its true origins.
I’ve slowly tracked URLs accompanying this toolkit and watched it dish out some very widely undetected malware, such as:
Information Stealing/Banking Trojans:
SpyEye
Zeus
Carberp
Mebroot Rootkit
Another more popular rootkit we’re seeing very widely on the Webroot realtime watch is: vSirefef.B/Zero-Access.
BlackHole toolkit preys on only two items in a user’s machine:
1) Unpatched operating system exploits
2) Internet browsers, add-in and plugin exploits such as Adobe and Java Software
Here are some of the known exploits the kit can execute on a victim’s machines.
Windows Operating Systems:
CVE-2010-1885 HCP (Microsoft Windows Help and Support Center in Windows XP and Windows Server 2003)
http://technet.microsoft.com/en-us/security/bulletin/MS10-042
CVE-2006-0003 IE MDAC
http://technet.microsoft.com/en-us/security/bulletin/ms06-014
Adobe Software:
CVE-2008-2992 Adobe Reader util.printf
CVE-2009-0927 Adobe Reader Collab GetIcon
CVE-2007-5659 Adobe Reader CollectEmailInfo
Java Software:
CVE-2009-1671 Java buffer overflows in the Deployment Toolkit ActiveX control in deploytk.dll
CVE-2010-0840 Java trusted Methods Chaining Remote Code Execution Vulnerability
CVE-2010-0842 Java JRE MixerSequencer Invalid Array Index Remote Code Execution Vulnerability
CVE-2010-0886 Java Unspecified vulnerability in the Java Deployment Toolkit component in Oracle Java SE
CVE-2010-1423 Java argument injection vulnerability in the URI handler in Java NPAPI plugin
The basic view the bot controller has is of the statistics page, which should indicate why I listed some of the expoits this toolkit is using. Not surprisingly, for as young as the kit is, you can see that both the Java and Adobe softwares are exploited far more than any others.
I’m sure some think they are safe using a browser other than Internet Explorer but it appears from this image there isn’t alot of difference in how this toolkit has behaved between the three browsers it’s touched.
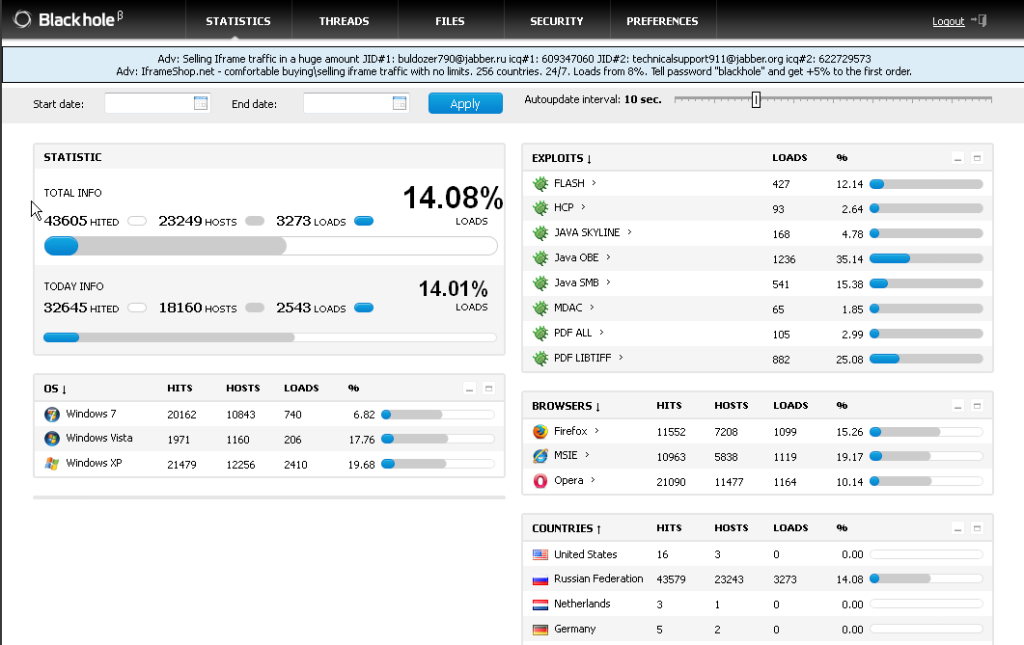
As the authors have made this toolkit easy to use, they have also made it easy to maintain a low detection rate on the binaries by using an antivirus scanning service which does not share any binaries collected with the AV industry.
The easy-to-read statistics page make it simple for the controller to view and monitor how well or poor the current bot is doing — how many operating systems it’s infected, what type of operating systems were infected, and in which countries they’re located.
(more…)

by Blog Staff | Oct 25, 2011 | Industry Intel, Threat Lab
By Jacques Erasmus
 I’ve been having trouble sleeping lately, and last night I pinpointed why. October has presented me with a perfect storm of Internet security developments: I embarked on my first few weeks as chief information security officer for Webroot amidst the most significant consumer product launch the company has ever had.
I’ve been having trouble sleeping lately, and last night I pinpointed why. October has presented me with a perfect storm of Internet security developments: I embarked on my first few weeks as chief information security officer for Webroot amidst the most significant consumer product launch the company has ever had.
These activities alone would’ve been enough to keep corporate security top of mind 24/7, but their occurrence during Cyber Security Awareness Month further drove it home for me. So I thought perhaps it may be cathartic for me, and helpful for you, if I shared some of the risk scenarios I’ve been thinking about, and best practices for protecting yourself and your organization from them.
Scenario One: Network-based infections.
Many organizations have solid standards for securing all of the desktop and laptop computers their employees use to locally and remotely access the corporate network. But all it takes is one contractor with an infected laptop to connect to the corporate network and expose sensitive corporate and customer information to malware. Think of it from a physical security aspect: like strangers in the building, you’d want to prevent rogue access points. The way we’re protecting ourselves at Webroot is by using our SecureAnywhere anti-malware technology to interface with network access control devices to ensure they’re clean before connecting to the network.
Scenario Two: Web app vulnerabilities.
SQL injections enable criminals to harvest passwords, bank account numbers and other personal information you may use for online transactions on seemingly safe sites. Man in the middle attacks — in which an attacker intercepts a communication between a customer and the server it’s intended to reach – are made possible by poor coding standards or poor input validation on web forms. Gaps like these enable injectors to change the fields where you enter your validation information in order to facilitate the heist. To the user, the site URL also may appear dodgy. Developers, it’s critical that you employ secure coding standards for web applications.
Scenario Three: Targeted Attacks.
This last scenario is more like a billion rolled into one; IT administrators as well as individual web users should have a healthy dose of concern about targeted attacks. Malware authors can customize Trojans for the specific environment they want to attack and the specific data they plan to steal, such as source code, financial information and customer data.
Advanced persistent threats like this typically penetrate organizations via social engineering tactics like spoofed emails that are designed to look like they’re coming from a trusted source. Employees who receive one of these emails and do what the message asks them to do are unwittingly triggering an exploit; clicking a link or opening a PDF, flash or QuickTime file leads to a drive-by download.
Here’s a real-world example that will give you a good idea of why the targeted attack is the most dangerous risk scenario of them all:
Bank tellers at a financial institution we were working with received an email under the name of someone at the company they knew and trusted. The email claimed their CEO was going to appear on TV and they’d need to register for a certain website in order to view the show online at their desks. A few of the tellers clicked a link in the email and landed on a website which told them to install a tool to view videos.
It turns out the tool the tellers installed was actually the SpyEye Trojan, and the criminal had done his homework. He knew this bank had an international wire transfer interface; he also knew that in order to use the bank’s wire transfer interface, you need to be inside the bank’s network to initiate the transfers, and you’d need to infect more than one teller because the bank uses dual control to enable a wire transfer. So infecting two employees was the ideal entry point.
While the tellers were working, the criminal created a second online session and made three very sizeable transfers to three remote geographies. And since the crime happened late on a Friday, the financial institution was unprepared to stop the transfers, ultimately losing thousands and thousands of dollars.
The good news is a number of measures can thwart this kind of attack:
IT administrators, keep in mind the easiest point of entry for a cybercriminal is your weakest link: Your employees. Educate your employees on spotting a fake.
Web users, if you’re online at work or at home and aren’t sure if the URL in a suspicious email is dangerous, check it out on whois.net or DomainTools.com. If you’re sending emails or transacting online outside of the office, make sure the sites you’re using are https websites. Otherwise your password can be sniffed on an unsecured network.

by Blog Staff | Oct 24, 2011 | Industry Intel, Threat Lab
By Michael Johnson
At Webroot we’ve been researching and chronicling developments with SpyEye since we first saw it in April 2010. This nasty Trojan is the successor to the Zeus Trojan, and it became essentially the main rootkit available for sale after the author of ZeuS left the underground market and sold ZeuS sources to the SpyEye team.
Over the last six months, through Webroot’s real-time watch technology and through my own adventures hunting malware proactively in my spare time, I’ve noticed an extreme escalation of SpyEye infections.
Last week I came across a URL for a password-protected site and at first didn’t think very much of it. But once I logged in, I realized I was on the administrator’s page of a SpyEye Panel, with what appeared to be full access. The administration panel was so easy to run, a fifth grader could do it.
At first glance, there were about 3,000 bots with approximately 600 active at the moment I was looking. The site was moved four days later which at that point, the number of bots was quickly approaching 10,000.
Now some of this is started to make sense. The authors of SpyEye have made it so simple to operate and in case of any trouble, apparently provide support promptly. Their selling points are working quite effectively and a lot of the wrong type of people are able to acquire the builders, Command and Control Servers for a small amount of money.
Taking a look at some of the screenshots, it doesn’t look very nice from any view.
(more…)

by Blog Staff | Oct 7, 2011 | Industry Intel
 .exe, PHP, HTML, and the list goes on. How many different kinds of files and code can potentially infect your PC? Webroot threat research analyst Nathan Collier explains a few of the the types of potentially dangerous files, other than the common executable (.exe) that can be found on a Windows PC and cause harm to it.
.exe, PHP, HTML, and the list goes on. How many different kinds of files and code can potentially infect your PC? Webroot threat research analyst Nathan Collier explains a few of the the types of potentially dangerous files, other than the common executable (.exe) that can be found on a Windows PC and cause harm to it.
[youtube=http://www.youtube.com/watch?v=CFH8VxP7gmY]
If you have a question you want answered by one of our threat experts send it to us! Comment below, tweets us (www.twitter.com/webroot), or email it to us (blog@webroot.com).

by Blog Staff | Oct 5, 2011 | Industry Intel, Threat Lab
A couple of days ago researchers for Android Police wrote about a security vulnerability in several HTC phones. The vulnerability lies with logging tools installed by HTC. These logging tools collect personal data like user accounts, email addresses, GPS info and SMS data. Having these tools logging users data is one thing but the fact that they are left unsecured and available to be exploited by a 3rd party app is a big blow to the device manufacturer. A 3rd party app would only need to request the INTERNET permission to gain access to the information collected by the tools. Why HTC has these tools in place hasn’t been answered, an answer they’ll have to provide to their customers at some point.
HTC’s public statement: “In our ongoing investigation into this recent claim, we have concluded that while this HTC software itself does no harm to customers data, there is a vulnerability that could potentially be exploited by a malicious third-party application. A third party malware app exploiting this or any other vulnerability would potentially be acting in violation of civil and criminal laws. So far, we have not learned of any customers being affected in this way and would like to prevent it by making sure all customers are aware of this potential vulnerability.”
The update will be sent over-the-air and users will receive a notification to install. No word on when the update will be available.
We all have a role to play in keeping our computing secure, but developers have a key role in that they need to ensure their applications are secure when it comes to customer’s data. This happens a lot, most recently with Skype, hopefully with more and more big name vendors being called out we’ll see developers tighten up their code.
Affected phones
EVO 4G
EVO 3D
Thunderbolt
EVO Sensation
MyTouch 4G slide
by Blog Staff | Sep 13, 2011 | Industry Intel, Threat Lab
By Marco Giuliani

In the past few weeks a Chinese security company called Qihoo 360 blogged about a new BIOS rootkit hitting Chinese computers. This turned to be a very interesting discovery as it appears to be the first real malware targeting system BIOS since a well-known proof of concept called IceLord in 2007. The malware is called Mebromi and contains a bit of everything: a BIOS rootkit specifically targeting Award BIOS, a MBR rootkit, a kernel mode rootkit, a PE file infector and a Trojan downloader. At this time, Mebromi is not designed to infect 64-bit operating system and it is not able to infect the system if run with limited privileges.
The infection starts with a small encrypted dropper that contains five crypted resource files: hook.rom, flash.dll, cbrom.exe, my.sys, bios.sys. The goal of these files will be presented later in this analysis.
The infection is clearly focused on Chinese users, because the dropper is carefully checking if the system it’s going to infect is protected by Chinese security software Rising Antivirus and Jiangmin KV Antivirus. To gain access to the BIOS, the infection first needs to get loaded in kernel mode so that it can handle with physical memory instead of virtual memory.
Many of you may recall the old CIH/Chernobyl infection, the infamous virus discovered in 1998 that was able to flash the motherboard BIOS, erasing it. Even CIH needed to gain kernel mode access to reach the BIOS, though at the time the virus was exploiting a privilege escalation bug in Windows 9x operating system which allowed it to overwrite the Interrupt Descriptor Table with its own payload from user mode, then triggering the overwritten interrupt handler and its malicious code is executed in kernel mode. Mebromi does not use such kind of privilege escalation trick anymore, it just needs to load its own kernel mode driver which will handle the BIOS infection. To do so, it uses two methods: it could either extract and load the flash.dll library which will load the bios.sys driver, or it stops the beep.sys service key, overwriting the beep.sys driver with its own bios.sys code, restart the service key and restore the original beep.sys code.
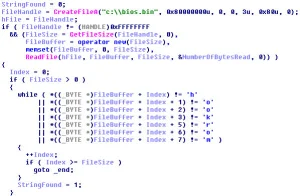
The bios.sys driver is the code which handle the BIOS infection. To read the BIOS code, it needs to map the physical memory located at physical memory address 0xF0000, this is where the BIOS ROM usually resides. Once read, the driver verifies if the BIOS ROM is Award BIOS, by checking the presence of the string: $@AWDFLA. If found, the driver tries to locate the SMI port that will be used by the rootkit to flash the BIOS ROM.

If the BIOS ROM matches the string, the rootkit saves a copy of the BIOS to the file C:bios.bin and pass the next step to the user mode component of the infection. The dropper extracts two files: cbrom.exe and hook.rom. Cbrom.exe is a legitimate tool developed by Phoenix Technologies, used to modify the Award/Phoenix BIOS ROM binaries. Hook.rom is the rootkit ISA BIOS ROM that is added to the BIOS binary, containing the rootkit infection. The dropper executes cbrom.exe with the /isa switch parameter, passing the hook.rom file. Before actually injecting the malicious ISA ROM, the dropper checks the BIOS ROM code looking for the “hook rom” string, used as a marker of the infection. If found, it means that the BIOS is already infected and it doesn’t need to be infected again.
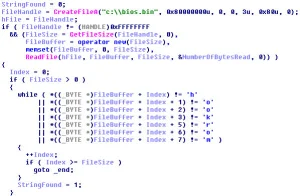
After that the bios.bin file has been modified, the bios.sys driver send to the BIOS SMI port the command 0x29, used to erase the BIOS flash, and then the command 0x2F used to write the new BIOS ROM code to the BIOS ROM.
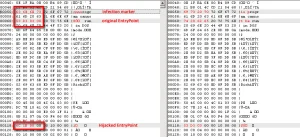
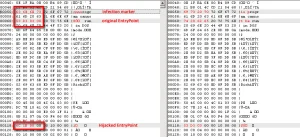
The BIOS is now infected, and the dropper goes to its next step: infecting the Master Boot Record. The infection is 14 sectors long and the original MBR is stored to the sector 7. To avoid potential startup issues, the infected MBR stores a copy of the original MBR’s partition table. Finally the dropper extracts the my.sys driver on the root of the C: drive. My.sys is a kernel mode rootkit that hijacks disk.sys’s IRP major functions, by redirecting the IRP_MJ_READ/WRITE and IRP_MJ_DEVICE_CONTROL native functions. It is used to hide the infection on the disk. Even if the BIOS infection doesn’t succeed, the rootkit does infect the MBR.
At the next system startup, after the BIOS POST phase, the malicious code injected inside it prepares the full MBR infection (all the first 14 sectors are stored inside the malicious BIOS rom, 7168 bytes in total) and checks the MBR code of the hard drive looking if the infection is already present. To do it, the BIOS malicious code checks for the presence of the string “int1” at the offset 0x92. If the string is not found, the BIOS malicious rom will overwrite all the first 14 sectors of the hard drive, thus restoring the MBR infection.

The system startup procedure continues and the control now passes to the malicious master boot record. Here the malicious payload analyzes the original MBR partition table and looks for the active partition, checking if it’s using a NTFS or FAT32 file system. The malicious MBR code contains indeed NTFS/FAT32 parser routines, used to get inside the file system to look for winlogon.exe or wininit.exe file. When found, the malicious code contains a file infection payload, able to inject malicious code inside the specified file and hijack the entry point of it. Before infecting the file, the MBR malicious code checks if it is already infected, by looking for the string “cnns” at the offset 0x50 from the beginning of the PE file. This is the infection marker. If the string is not found, the infection stores a crypted payload – about 600 bytes of code – inside winlogon.exe or wininit.exe and hijacks the PE entry point to the beginning of it, saving the original entry point at the offset 0x60.
The job of the MBR infection ends here, waiting for the Windows startup which will load the patched executable. When loaded, the payload self-decrypt its malicious code and loads in memory the my.sys driver. Then it tries to download an additional infection from the (now unavailable) URL address: http://dh.3515.info:806/test/91/calc[removed].
The concept behind Mebromi is not new. In fact we must recall the IceLord BIOS rootkit published in 2007, a public proof of concept able to target Award BIOS rom, using an approach very similar to the Mebromi one – or should we say that Mebromi is more than just inspired by the IceLord rootkit?
Storing the malicious code inside the BIOS ROM could actually become more than just a problem for security software, giving the fact that even if an antivirus detect and clean the MBR infection, it will be restored at the next system startup when the malicious BIOS payload would overwrite the MBR code again. Developing an antivirus utility able to clean the BIOS code is a challenge, because it needs to be totally error-proof, to avoid rendering the system unbootable at all. The job of handling with such specific system codes should be left to the developers of the specific motherboard model, who release BIOS updates along with specific tool to update the BIOS code.
On the other hand, although this kind of infection is potentially one of the most persistent infections known out there in the wild, it will hardly become a major threat because of the level of complexity needed to achieve the goal. While a kernel mode infection or a MBR infection could still work in a generic way among all the PC out there – and they still have a huge available free space to play with, a BIOS-based rootkit needs to be fully compatible with all major BIOS rom out there, it should be able to infect all the different releases of Award, Phoenix, AMI BIOS’s out there; a level of complexity that is simply unasked for writing a good persistent infection (e.g. TDL rootkit, various Rustock releases, ZeroAccess rootkit among all). In fact, why is Mebromi only targetting Award BIOS rom? Perhaps because there was already a known proof of concept that is 5 years old targeting Award BIOS ROM available online.
Are BIOS rootkits a real threat? Yes, we can consider Mebromi the first real BIOS rootkit incident discovered in the wild – let’s consider IceLord BIOS rootkit more a proof of concept. Should we be concerned about BIOS rootkits? Well, while we try to discover whether our PC is infected by an unknown and super-stealth BIOS rootkit, let’s try and look if there is a more “humble” kernel mode rootkit which is already infecting our PC, allowing a remote attacker to silently own our system.

by Blog Staff | Aug 31, 2011 | Industry Intel, Threat Lab












 The past couple of days have been very busy for a lot of people, following the announcement by Microsoft that they had discovered a new network worm called Morto. After reading the refreshingly thorough writeup about Morto from both Microsoft and our partner Sophos, we were surprised to find that a few of our customers had been infected — and cleaned up — beginning with some poor schlub in South Africa as early as July 23rd, but the worm kicked into high gear last Thursday and began to propagate rapidly.
The past couple of days have been very busy for a lot of people, following the announcement by Microsoft that they had discovered a new network worm called Morto. After reading the refreshingly thorough writeup about Morto from both Microsoft and our partner Sophos, we were surprised to find that a few of our customers had been infected — and cleaned up — beginning with some poor schlub in South Africa as early as July 23rd, but the worm kicked into high gear last Thursday and began to propagate rapidly.
But, as much as the technical details in these posts are useful for researchers and analysts, they don’t really get to the heart of how a user of an infected computer would be affected by the worm. So, after spending a bit of time infecting some of my own machines these past couple days, I wanted to share my hands-on experience with you.
Bottom line, the worm was written to spread to (and infect) the computers run by people who don’t take security seriously: It copies itself to other computers by trying to Remote Desktop into those computers using a list of what can only be described as completely moronic passwords (the full list is on Microsoft’s technical writeup about the worm). The repurcussions are that people (or companies) who use poor quality, easily guessed passwords have been (or are going to get) spanked by Morto, and then they’ll be really irritated at the (reversible but obnoxious) changes the worm makes to the behavior of the infected computer.
(more…)

by Blog Staff | Aug 25, 2011 | Industry Intel, Threat Lab












 An unusual family of Trojans, apparently of Chinese origin, engages in rootkit-like behavior which seems designed not to hide the presence of the malware on an infected system, but to misdirect or confuse a technical person who might be using system analysis tools on an infected computer.
An unusual family of Trojans, apparently of Chinese origin, engages in rootkit-like behavior which seems designed not to hide the presence of the malware on an infected system, but to misdirect or confuse a technical person who might be using system analysis tools on an infected computer.
The Trojans all originated from a server operated by a free Web host in China, and each sample we tested sent profiling data about the infected system to a command-and-control server located on yet another free Web host, also located in China. It appears to have capabilities to receive instructions to download other components, and it scans the system for antivirus products commonly available in China, including products made by Qihoo 360, China’s largest homegrown antivirus company.
But the most interesting aspect of the Trojans was how it managed to fool most of the free tools someone might use to monitor running programs. The Trojan shows up in the list of active programs, but when that list includes a full path to the running executable, that path points at a nonexistent file supposedly in another location. (more…)

by Blog Staff | Aug 17, 2011 | Industry Intel, Threat Lab













FireEye’s Lanstein and Wolf speak at Black Hat
I’ve worked in the security industry for nearly five years, and it was apparent early on that the most successful people in this field bring to their work a passion and a commitment to protecting not only one’s customers, but to providing a certain level of information about security threats to the world at-large, so even your non-customers can help or protect themselves.
It can be hard to know where to stop once you get on a roll. Malware infections frequently lead to unexplored, interesting backwaters on the Internet. And, sometimes, those backwaters are where the criminals run those operations. When I stumble upon a criminal network or a botnet controller, it simply doesn’t feel like I’ve done enough when I merely add signatures which block or remediate infections and communications with a command-and-control server from Webroot customers. If malicious behavior depends on one or more Internet sites that send instructions, my (and many others’) initial reaction is we need to shut that down, permanently. But sometimes, a too-rapid reaction can blow back in your face.
Obviously, that was also the case when Alex Lanstein and Julia Wolf of internet security firm FireEye stumbled upon the Rustock botnet. At one time, before law enforcement in several countries swooped in on the data centers hosting the botnet’s command-and-control (CnC) infrastructure in a coordinated raid earlier this year, the massive network of Rustock-infected computers was responsible for about half of spam flooding the ‘net. The researchers’ instincts to engineer a takedown of the botnet sounded very familiar, but their initial attempts to do so backfired, and may have even spurred the malware developers to change their game, and may have made it more difficult, eventually, to eliminate the CnC altogether.
(more…)

by Blog Staff | Aug 9, 2011 | Industry Intel, Threat Lab












 A serious, targeted threat from customized malware that steals credit card magnetic strip track data could literally bankrupt your business. That’s the message two security researchers from Trustwave gave at their talk during the Defcon computer security conference Saturday.
A serious, targeted threat from customized malware that steals credit card magnetic strip track data could literally bankrupt your business. That’s the message two security researchers from Trustwave gave at their talk during the Defcon computer security conference Saturday.
The researchers, Jibran Ilyas and Nicholas Percoco of Trustwave Spider Labs, respond to calls for help when businesses find malware in critical systems. When banks field reports of credit card fraud, they try to find the earliest common location or business where all the victims used their card. When they do, the bank calls the business, who then call in the researchers.
In their talk, Malware Freak Show 3, the researchers reported on several types of malware all of which are designed to steal the so-called Track 1 data — the information encoded on the magnetic strip on the back of the card — when a salesperson or waiter swipes the credit card attached to the cash register.
The malware may reside on the register (a device that, in many cases, is simply a custom-configured Windows computer) or on a server in the back room of the business that’s used to process credit card transactions. Once the malware has the Track 1 data, it transmits the string of numbers to remote locations, where the data can be used to produce fake, but functional, physical credit cards. The thieves can then sell or use the cards to purchase valuable merchandise.
(more…)