by Blog Staff | Feb 15, 2010 | Threat Lab












 Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.
Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.
This will be the 30th ceremony held in the 33 year history of the awards. As in previous years, the BRIT Trust (a charity run by BPI, the UK’s recording industry trade association) will donate profits from the ceremony, including the sale of a three-CD compilation, to various charities that benefit young people in the UK.
Unfortunately, at least two distinct threats face Web surfing Anglo-musicophiles: Bogus music download sites, which tease users with offers of “free downloads” of the compilation set, but then require users to register and pay a fee — none of which ends up in the hands of the BRIT Trust charity; And the purveyors of irritating fake alert messages, which invariably lead to rogue antivirus downloads, are also heavily pushing themselves to near the top rankings in some search results.
(more…)

by Blog Staff | Feb 10, 2010 | Threat Lab












 Sometimes, the early bird gets the worm — and not in a good way. People who file their tax returns early are being targeted by a phishing scam that comes with the promise of a big income tax refund.
Sometimes, the early bird gets the worm — and not in a good way. People who file their tax returns early are being targeted by a phishing scam that comes with the promise of a big income tax refund.
Unlike previous tax-themed scams, which have been based on the stick — fake warnings or penalties supposedly issued by the Internal Revenue Service and its UK counterpart the HMRC — these carrot Tax Refund Online Form frauds promising payouts appear to originate from different countries’ tax authorities, notably those of India and Canada.
We’ve come across a number of identical pages that have been cleverly designed to resemble the appearance of the Web sites of India’s Income Tax Department and the Canada Revenue Agency (CRA). The fake CRA “Tax refund online form” claims that the recipient will receive CAN$386 — a nontrivial sum — if they provide the necessary credit card information in the form. Wait, what?
The fake page supposedly from India (which inexplicably refers to the Indian Ministry of Finance as the IRS) tells prospective victims that they stand to gain a whopping 820.50 rupees for filling out a form with not only full credit card details but also a bank account and routing number, and debit card PIN, then waiting two to three business days for the information to be “processed” or, as we call it in this country, “stolen, used to commit fraudulent purchases, then discarded.”
And yes, you read that right — 820.50 rupees. For those unfamiliar with current rupee-to-dollar exchange rates, at a little over 46 rupees to the dollar, that’s a false promise you will receive…wait for it…nearly eighteen US dollars.
News flash, income tax filers: If you have been following the law and filing tax returns, and your respective government wants to issue you a refund, they already know where your bank accounts are.
(more…)

by Blog Staff | Feb 8, 2010 | Threat Lab












 February 9 marks Safer Internet Day, and around the world, people are trying to help their fellow netizens navigate an obstacle course of threats to their security and privacy. InSafe, the organization funded by the EU that sponsors the annual youth-targeted event, has themed the day around the concept “Think B4 U post.” As grammatically sloppy as that sounds, it’s actually good advice.
February 9 marks Safer Internet Day, and around the world, people are trying to help their fellow netizens navigate an obstacle course of threats to their security and privacy. InSafe, the organization funded by the EU that sponsors the annual youth-targeted event, has themed the day around the concept “Think B4 U post.” As grammatically sloppy as that sounds, it’s actually good advice.
Readers of this blog shouldn’t be surprised that myriad dangers threaten the safety of all Internet users: Keylogging software disguised as “updates” are everywhere; Fake security alerts pop up when you least expect them; Phishing Web pages are more cleverly designed than ever to steal your passwords; Spam is choking email; Worms stalk social networks; Even your mobile phone is at risk of malicious software designed to steal valuable information from you. The big question on everyone’s mind is: What do you do to protect yourself?
[vimeo 9266107]
The answer’s simple, really. You have to think before you act, and make sure you understand the consequences of whatever you do, write, post, or click online. Once you develop your Internet spidey senses, you’ll be able to spot something that’s out of place, or weird, or just dodgy before it catches you out.
Despite the increasingly clever tricks criminals employ, they still have to lie and cheat in order to steal. What follows are a few easy ways you can catch them out in their lie before it’s too late. We’ve also put together a short video that shows just how easy it is, once you’re in the right frame of mind.

by Blog Staff | Feb 5, 2010 | Threat Lab












 Spammers are the source of a flood of messages that appear to originate from various social networks, including Facebook and Myspace, as well as popular sites like iTunes.
Spammers are the source of a flood of messages that appear to originate from various social networks, including Facebook and Myspace, as well as popular sites like iTunes.
The spam messages usually just contain a link, and possibly a few words. Their subject matter falls into three general categories common to most contemporary spam: Pill vendors, Russian bride “vendors,” and drive-by download sites hosting Zbot password-stealer installers.
It’s not unusual for spammers to forge the return addresses, but the sheer volume of spam that has been forged so it appears to originate from MySpace, Facebook, or iTunes is notable.
(more…)

by Blog Staff | Jan 28, 2010 | Threat Lab












 Today is Data Privacy Day, which is supposed to remind us all that keeping our digital secrets a secret is important and necessary. To commemorate the event, I’d like to run down some of the most serious privacy threats any of us could face on a daily basis: How a malware infection puts your privacy at risk.
Today is Data Privacy Day, which is supposed to remind us all that keeping our digital secrets a secret is important and necessary. To commemorate the event, I’d like to run down some of the most serious privacy threats any of us could face on a daily basis: How a malware infection puts your privacy at risk.
For years, it’s been clear that the creators and distributors of malicious software are after one thing above all others — money. Whether they steal it (by installing a keylogger, or just phishing) or defraud you out of it (by coercing users to pay good money for a useless security application, or holding your computer itself hostage) cash is the name of the game.
But this isn’t pickpocketry — they’re not literally taking money out of your wallet. Somewhere along the way, the Bad Guys are using your private information to do that. Here are just a few ways they accomplish this task, by hook or crook. And more importantly, some tips that you can use to put a crimp in their plans.

by Blog Staff | Jan 27, 2010 | Threat Lab












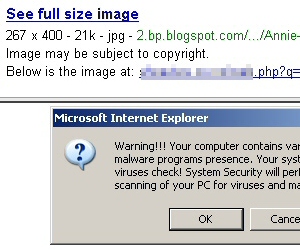 Searchers beware: Those photos of celebrities or funny cat pictures that turn up in your Google image search results might not be photos at all, but fake antivirus alerts. Evidence appears to indicate that a similar scam to one we blogged about last November may be working its way up the Google food chain into other forms of search results.
Searchers beware: Those photos of celebrities or funny cat pictures that turn up in your Google image search results might not be photos at all, but fake antivirus alerts. Evidence appears to indicate that a similar scam to one we blogged about last November may be working its way up the Google food chain into other forms of search results.
While searching for photos of Annie Wersching, an actress who recently joined the cast of the TV show 24, we stumbled into one of these javascript-enabled fakealert browser traps. Oddly enough, when you click one of these bogus linked pictures in the Image Search results frame, the original Google search frame remains at the top of the page. The fakealert runs in the lower part of the page, closing the Google search pane but retaining the Google URL in the browser’s Address Bar.
Throughout the day we’ve been looking for links such as these; Each malicious URL we found funnels the browser into the same fakealert, which itself leads to the same rogue antivirus product. Each time we revisited the site, we ended up with what was essentially the same equally nasty rogue antivirus application, sometimes in a different skin, sometimes with a different name. Early in the day we were pulling down something called Total Security. By the afternoon, the tool’s name had morphed to become Security Tool.
The rogue’s behavior on an infected system is obnoxious in the extreme. It hides the desktop by covering everything over with its own wallpaper, and blocks your ability to right-click the desktop, so it’s more difficult to revert the desktop’s appearance by changing your Display Properties settings. It also disables the scroll wheel on the mouse, then blames that behavior on a massive infection it claims has taken over your PC. It prohibits most Internet-capable applications, or even tools like the Task Manager, from running, in the guise of its “firewall” component. Of course, it’s all smoke and mirrors, an attempt to convince you to spend from $50 to $90 on completely ineffective, utterly useless former-Soviet snake oil.
(more…)

by Blog Staff | Jan 27, 2010 | Threat Lab












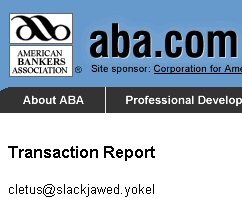
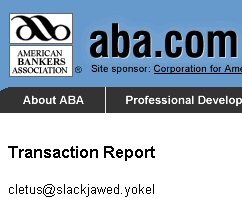 As the reign of nuisance by Trojan-Backdoor-Zbot continues, the latest scam invites victims to review a “transaction report” on a page supposedly on the Web site of the American Bankers Association, or ABA.
As the reign of nuisance by Trojan-Backdoor-Zbot continues, the latest scam invites victims to review a “transaction report” on a page supposedly on the Web site of the American Bankers Association, or ABA.
(I wouldn’t want to call it a reign of terror; that might give the Zbot authors an inflated sense of their own importance. Zbot is like a wasp buzzing around the picnic table, and deserves a good, sharp smack, preferably with a shoe.)
The “report” is, of course, an installer for this Trojan. The scam is virtually identical to ones we’ve seen where the scammer sets up Web sites in the guise of such notable organizations as the IRS, CDC, Visa, and other organizations, or software programs like AOL Instant Messenger and Microsoft Outlook, or Web sites such as Facebook.
As in the previous scams of this ilk, the URL that victims click includes the victim’s email address; That email address appears within the fake page, along with a bogus transaction ID and an outrageously large Amount of transaction — all information that’s designed to inspire a sense of panic and urgency in the victim, leading the victim to click the “generate transaction” link on the page and infect a computer with the Trojan.
(more…)

by Blog Staff | Jan 25, 2010 | Threat Lab












 A payload file installed along with some variants of the rogue Internet Security 2010 “antivirus” program modifies victims’ networking settings within Windows, inserting itself into the network stack and preventing victims from visiting some of the Web’s most popular Web sites. More than 40 sites have been targeted, including: Microsoft’s live.com and Bing search engine; social networking giants Facebook, Twitter, MySpace, Bebo, LinkedIn, and YouTube; news organizations including Fox News, The New York Times, the Washington Post, and the UK’s Guardian and BBC news sites; and blogs hosted by blogger.com, livejournal.com, and wordpress.com.
A payload file installed along with some variants of the rogue Internet Security 2010 “antivirus” program modifies victims’ networking settings within Windows, inserting itself into the network stack and preventing victims from visiting some of the Web’s most popular Web sites. More than 40 sites have been targeted, including: Microsoft’s live.com and Bing search engine; social networking giants Facebook, Twitter, MySpace, Bebo, LinkedIn, and YouTube; news organizations including Fox News, The New York Times, the Washington Post, and the UK’s Guardian and BBC news sites; and blogs hosted by blogger.com, livejournal.com, and wordpress.com.
The payload modifies the Layered Service Provider (LSP) so that calls to those Web sites pass through the malicious file, which displays a warning message in the browser instead of the blocked Web site. The message says:
This web site is restricted based on your security preferences
and
Your system is infected. Please activate your antivirus software.
We’ve seen an increase in the number of spies that bollix the LSP chain lately. In cases where this happens, if you simply remove the malicious file that is referenced in the LSP, the computer remains unable to connect to the Internet afterwards. To fully repair the PC, you’ll need to fix that broken chain.
Fortunately, the fix for this spy — which we’re calling Trojan-Annoyinator — is fairly easy. Users of Webroot’s products can simply sweep, and the spy along with its LSP modifications will be removed upon reboot. If you don’t have one of Webroot’s antimalware product installed, you can go through the process manually, which isn’t difficult for someone familiar with Windows tools such as Regedit. The only problem might be getting to Microsoft’s Web site (where the instructions are posted) from an infected computer.
(more…)

by Blog Staff | Jan 21, 2010 | Threat Lab












 The Zbot keylogger campaign-of-the-month targets users of AOL Instant Messenger (AIM) with a message that claims to be an update notification for users of the instant messaging client application. Users unfortunate enough to click through the link in the email message to download what they think is something called “aimupdate_7.1.6.475.exe” will be in for a rude awakening.
The Zbot keylogger campaign-of-the-month targets users of AOL Instant Messenger (AIM) with a message that claims to be an update notification for users of the instant messaging client application. Users unfortunate enough to click through the link in the email message to download what they think is something called “aimupdate_7.1.6.475.exe” will be in for a rude awakening.
The malicious page delivers its payload whether or not a victim clicks the link to get executable file: It opens an iframe to a site that attempts to use vulnerable versions of Adobe Reader to push the Zbot keylogger down to the victim’s computer, then execute it, within a few moments of the page loading.
The address of the iframed page resides in a particularly sketchy corner of the net. The network the IP address is part of, known as AS50369, goes by the name VISHCLUB-as Kanyovskiy Andriy Yuriyovich. Sure sounds a lot like someone’s name for their phishing gang. The same network has been in use for the past week delivering payloads on well-worn Outlook Web Access and HMRC Zbot download pages.
Seriously, though: Vishclub? Is that the best the Russian hackers can come up with? It sounds like what you’d call a fisherman’s smoking lounge on the Baltic coast, where thick clouds of cheap tobacco is the only thing that can overpower the putrid stench of rotting seafood.
The fake page has the outward appearance of a page hosted by AOL, but it clearly isn’t the real deal. Once you take a closer look, the site and its social engineering tricks begin to smell a bit like day-old fishwrap, as well.
(more…)

by Blog Staff | Jan 20, 2010 | Threat Lab












 A new variant of the Koobface social networking worm is sending social networkers links that lead to fake videos supposedly posted by the beloved cartoon antihero Spongebob Squarepants. The fake videos only display a popup message labeled “Adobe Flash Player Update” that says “This content requires Adobe Flash Player 10.37. Would you like to install it now?” Clicking anywhere on the page downloads the Koobface installer to the victim’s PC.
A new variant of the Koobface social networking worm is sending social networkers links that lead to fake videos supposedly posted by the beloved cartoon antihero Spongebob Squarepants. The fake videos only display a popup message labeled “Adobe Flash Player Update” that says “This content requires Adobe Flash Player 10.37. Would you like to install it now?” Clicking anywhere on the page downloads the Koobface installer to the victim’s PC.
The technique isn’t new, but this is the first sign that the crew behind Koobface is switching from ‘holiday mode’ (when they sent around links to videos that were supposedly posted by Santa Claus) to ‘post-holiday mode.’
 In other ways, the worm features a few small tweaks: Its Captcha tool, which attempts to convince infected users to enter the text of a captcha into a dialog box, has been modified to read and properly display the new ReCaptcha format used by some social network sites. The new format randomly places black circles ‘behind’ the text, and inverts the text of the captcha phrase where the text and black circles intersect.
In other ways, the worm features a few small tweaks: Its Captcha tool, which attempts to convince infected users to enter the text of a captcha into a dialog box, has been modified to read and properly display the new ReCaptcha format used by some social network sites. The new format randomly places black circles ‘behind’ the text, and inverts the text of the captcha phrase where the text and black circles intersect.
(more…)

 Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.
Music fans may already be aware that next Tuesday the British music industry will honor the top acts of the year at a ceremony known simply as The BRITs. What they may not know is that common Internet criminals have begun to target people searching for information about the artists and the music connected with the awards for attack.