by George Anderson | Dec 21, 2016 | Industry Intel, Threat Lab
Did we get you to click? That’s how the bad guys get you, too. One little click on the wrong link and your clients’ businesses could be up the proverbial creek.
Theft only comprises one aspect of the activities cybercriminals undertake, but it’s a sizeable chunk of their enterprise. What’s worth noting is what the thieves are stealing. The majority of cybercrime is focused on stealing data with the intent of selling it for profit to a third party, but what keeps one little malware family in the headlines is how differently it plays the game. In a recent conversation between Webroot Chief Technical Officer and rocket scientist Hal Lonas and Penton Technology Market Analyst Ryan Morris, we can see how ransomware is rewriting all the rules.
During the discussion, Lonas noted, “the bad guys used to want your data because it was valuable to them. If [they] could get your credit card number or your identity or a secret from your company, [they] could go sell that.”
When Morris asked what makes ransomware different, Lonas had this to say: “The interesting thing about ransomware is that criminals are now saying, ‘Your data is valuable not to me, the bad guy, but to you. How much is your data worth to you?’ They’re betting that you don’t have any backup and protection in place, so their angle is to take your data and hold it for ransom until you decide what the value is, and then you pay them.” So, while conventional security threats may steal information to sell down the line, what sets ransomware apart is that it seeks to extort money from the victimized company itself.
Morris responded that he’s heard about modern companies with robust security operations run by professional in-house InfoSec teams who, as recently as this year, have paid ransoms. “That blew my mind,” he stated. “I, perhaps naively, thought we’d solved these types of problems.”
Layered Security is the Game Changer in Fighting Ransomware
The question is: if even large businesses with high-powered, fully-staffed dedicated IT departments are having a hard time with these threats, what hope do smaller businesses and the managed service providers (MSPs) they trust to secure them have to fight back against ransomware?
Morris raised the questions, “How can we win the battle in the ransomware universe? What preventive steps should we take, and what ongoing measures should MSPs and end users implement to protect themselves from ransomware threats?”
Lonas cited these key strategies for a solid cybersecurity defense:
“Investing in backups and data security is of paramount importance. That’s hardly new advice. It applies to everything from business security to homeowner’s insurance. But, with a threat like ransomware on the loose, it’s more crucial than ever to make sure our data is securely backed up and that we can recover it quickly, easily and in its entirety. We also have to test the backups; spend a little extra time and money verifying that the recovery systems are going to work.
“From there, we need to make sure we have a multi-level security approach in place. We’ve talked about this for years—the layered security approach—to ensure that malware and other types of breaches don’t get through, and each new attack vector can mean a new layer. Sometimes this causes redundancy, but as long as the various layers work in harmony, they provide comprehensive security that can prevent breaches. Firewalls, next-generation firewalls, web filtering, proxies, VPNs… we have to ensure all of those protection layers are deployed.”
As he continued, Lonas made sure to emphasize the importance of endpoint security. “We have to have world-class endpoint security on all of our machines: the Windows machines, the Apple machines, and the mobile devices, including bring-your-own-device.” According to Lonas, every device that could conceivably connect to a network needs protection so that it doesn’t become the gateway for cybercriminals to infiltrate an organization.
The More Your Clients Know…
Finally, user education is critical. Lonas concluded his recommendations by stating that users need to be aware of the types of threats they’re going to face, the various kinds of phishing attacks, fake messages, emails, and even phone calls they might get from people claiming to be tech support personnel who just need a password to make a quick update. “Bad guys are always figuring out new ways to get to us,” he warns. “The combination of layered security that covers all potential threat vectors, solid backup and recovery strategies, and user education is the only way companies can protect themselves, their employees, and their customers from ransomware.” Existing Webroot MSPs can take advantage of the tools and content available in the ChannelEdge Toolkit and use it educate and inform their clients on threat protection and industry best practices.
Get Ready, Get Set, Take Action
Adopt a next-generation endpoint security solution that uses advanced behavioral technology and real-time detection to keep users safe. Take a 30-day FREE trial of Webroot SecureAnywhere® Business Endpoint Protection—no risk, no obligation to buy. You don’t even have to uninstall existing security.

by LeVar Battle | Dec 16, 2016 | Home + Mobile
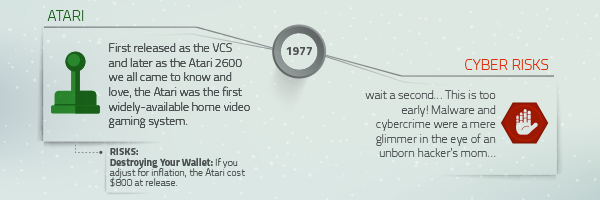
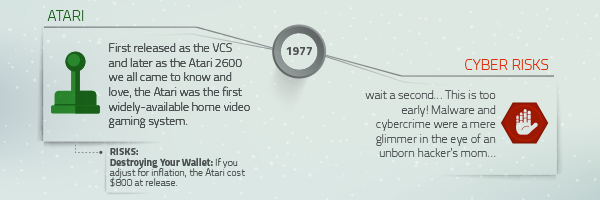
Who remembers the Atari 2600? Yeah, I don’t either. Just kidding. Maybe. It’s hard to think about the words tech and toys together before the 1990s. However, they were a thing. Kids of the late 70s reveled in the Atari 2600. It became a staple of pop culture—defining a generation of gaming young enthusiasts. But tech toys didn’t stop there.
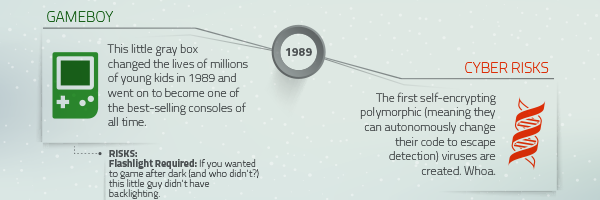
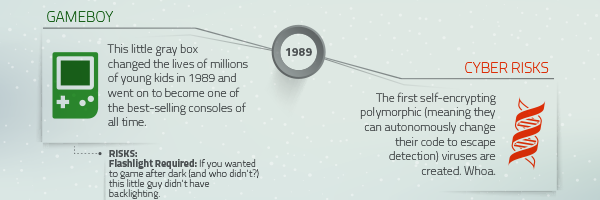
 Later was the introduction of Game Boy in 1989. The ability to leave your bedroom and actually play video games on the go? That was life-altering for, I dare to say, every teenage boy and girl. Although, for many, the 2000s were the formative years of tech toys. They saw the 90s as a blip on the radar of tech toys’ rise to the domination of Toyland. This group had a front row seat to watch Xbox Live parade onto the scene in all of its glory. The first successful home online gaming console even left this writer a little jealous. Where were you during my gaming days?
Later was the introduction of Game Boy in 1989. The ability to leave your bedroom and actually play video games on the go? That was life-altering for, I dare to say, every teenage boy and girl. Although, for many, the 2000s were the formative years of tech toys. They saw the 90s as a blip on the radar of tech toys’ rise to the domination of Toyland. This group had a front row seat to watch Xbox Live parade onto the scene in all of its glory. The first successful home online gaming console even left this writer a little jealous. Where were you during my gaming days?
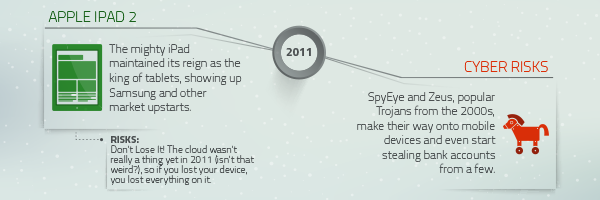
 The proliferation of tech toys over the years has only been eclipsed by the dangers surfacing from the bowels of cartridge graveyards around the world. I’m talking cybercriminals. They see the one thing that brings joy to so many sugar plum-dreaming cherubs during the holidays – tech toys – as a means to wreak havoc.
The proliferation of tech toys over the years has only been eclipsed by the dangers surfacing from the bowels of cartridge graveyards around the world. I’m talking cybercriminals. They see the one thing that brings joy to so many sugar plum-dreaming cherubs during the holidays – tech toys – as a means to wreak havoc.
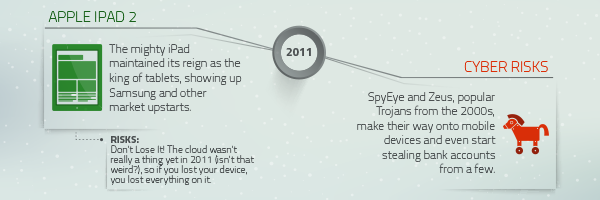 I’m not talking script kiddies in their parents’ basements. These aren’t the kids we grew up with then nor the kids growing up now. Dismiss the prevailing idea of what a hacker is. Don’t be mistaken; these cyber thieves are real and dangerous. They pose a threat to your personal security and the sanctity of all that is Christmas morning.
I’m not talking script kiddies in their parents’ basements. These aren’t the kids we grew up with then nor the kids growing up now. Dismiss the prevailing idea of what a hacker is. Don’t be mistaken; these cyber thieves are real and dangerous. They pose a threat to your personal security and the sanctity of all that is Christmas morning.

by Connor Madsen | Dec 16, 2016 | Industry Intel
Credit card fraud and email scams aren’t the only thing you have to worry about this holiday season. Criminals in the UK are stepping up their game by using radio frequencies to steal cars.
Ransomware Uses Credit Card Emails with Infected Attachments
A new ransomware variant of Cerber is using fake credit card reports to entice users into opening infected email attachments. By tricking users with fake fraudulent charges for items they never purchased, the malware authors hope the victim will open the malicious document to review and cancel the charge. Fortunately, the emails are poorly-worded and contain several spelling mistakes to make them easier to spot.
Another Yahoo Hack…
Many of you have heard of the fairly large hack that affected Yahoo users in the last few years, and have (hopefully) taken steps to protect yourselves from fraudulent activity. But Yahoo recently came forward to reveal a much larger hack that could affect over 1 billion users and their account information. Although Yahoo was able to identify the infiltration point, the information—both encrypted and unencrypted—had been compromised for at least a year before they discovered the breach.
Enterprising Car Thieves Use Radio Waves to Keep Doors From Locking
Criminals are jamming the radio signals that lock and unlock vehicles, leaving unattended cars open and ready to steal. While the majority of recent thefts have taken place in the UK, this could easily become a global concern. As vehicle technology continues to advance, it’s no surprise that car thieves are keeping up with the times.
Health Service Providers Stuck on Old OS
A recent study on UK National Health Service trusts found that over 90% of healthcare providers were running their networks on Windows XP. Microsoft themselves stopped supporting this outdated operating system over a year ago and, as such, it’s full of vulnerabilities. Unfortunately, many providers around the world use outdated software with known security issues, which can put sensitive patient information at risk.
Evernote Changes Tune After Privacy Concerns
In the past few days, Evernote, the popular note-taking app, announced they would begin allowing select employees to view snippets of user data to better enhance their machine learning algorithms. The program was launched as an opt-out, but the issue of privacy erupted almost immediately. After just one day’s worth of outcry, the company changed the policy to opt-in and sent an apology to their 200 million users.

by Blog Staff | Dec 13, 2016 | Managed Service Providers
Managed service providers are tasked with serving a broad range of markets, from construction to healthcare; accounting to legal; staffing firms to manufacturing; media and advertising to technology. But the day-to-day MSP challenges, even across so many diverse verticals, remain the same. Let’s break it down: modern technology changes fast and keeps gaining momentum, so how do you stay current and relevant? Providing quality goods and services gets complicated and pricey fast; how do you give your customers the value they expect without your own margins taking a hit? As the managed services sector continues to grow, how do you differentiate yourself from the competition?
Let’s switch gears a little and talk about cybersecurity. It’s no surprise that MSPs often think of endpoint protection as a “necessary evil.” MSPs have to supply endpoint cybersecurity services that satisfy their clients’ demands, but most solutions involve time-consuming infection remediation, awful system performance, mountains of malware-related downtime, not to mention the resulting customer frustration.
Staying Relevant and Seizing Opportunity
Because SMBs typically lack the internal resources needed to effectively manage complex systems, cybersecurity is an ideal avenue for putting the managed services model to use. Faced with modern threats and the hassles of traditional endpoint protection products, most users feel overwhelmed by security awareness and management, so offering next-generation protection that’s easy to manage, won’t conflict with other software, and won’t slow users down as it keeps them safe is an excellent way to stay relevant and build customer loyalty.
The High Cost of Living
As you well know, providing services isn’t sustainable if your solutions don’t amplify your profitability. But you can drive down operational costs by selecting an endpoint cybersecurity vendor that uses a cloud-based architecture and requires no infrastructure investment, thereby enabling faster deployment and less intensive management. If the vendor offers highly responsive support, automatic remediation, and low resource usage, you can improve customer satisfaction while reducing time spent repairing systems—without having to skimp on quality.
Looking to the Future
When choosing a cybersecurity partnership, be sure to look for a vendor whose solutions foster predictable, recurring revenue to help quantify future revenue for business decisions, and who provides marketing resources and sales enablement to boost MSP margins. And keep your options open—find a partner who offers flexible billing to lower your overhead and enable easy scalability (and won’t lock you into a contract you’re unhappy with in the long run.) Finally, pick a partner with a strong reputation, so you can leverage their proven protection to increase your customer loyalty and generate more referrals.
Proving the Point
Ultimately, these tips are just hearsay. Until you can properly vet a solution in a real-world environment, it’s hard to determine what will and won’t work for your business. Try to find solutions you can trial easily, and look to industry experts and your peers for their experiences and advice.
Read this case study to find out how SWAT Systems, an MSP managing over 3,300 endpoints, drastically improved their customer satisfaction, reduced time spent remediating infections by 75%, and increased profitability an average of 10-20%—just by switching cybersecurity vendors.
Or, take a free, no-risk, no-conflict 30-day trial of Webroot SecureAnywhere Business Endpoint Protection with the Global Site Manager to see the solution SWAT Systems chose in action.

by Connor Madsen | Dec 9, 2016 | Industry Intel
Personal computers and devices aren’t the only targets for ransomware authors. Their methods have evolved to target government offices and profitable organizations, forcing them to rethink their cybersecurity mitigation plans.
Blackheart Records Data Left Exposed Online
Recently, it has been discovered that a large, unsecured database containing sensitive information on several prominent recording artists from Blackheart Records was left publicly available for an undetermined amount of time. The data that was found included passport scans, banking information, and other sensitive login information for Joan Jett and several of her bandmates. While the database has since been taken offline, the researchers state that there are still hundreds of servers and private machines that use Rsync as a backup, which leaves the server vulnerable.
GoldenEye Ransomware, New Petya Variant
In the past week, a new variant of the Petya ransomware has been discovered in the wild. Going by the name ‘GoldenEye‘, the variant runs the file encryption prior to gaining administrative privileges to modify the MBR (Master Boot Record), unlike Petya which would attempt the MBR modification first. While encrypting the hard drive, ‘GoldenEye’ displays a fake ChkDsk screen to placate the user until the process is complete. Currently, it’s main targets appear to be German-speaking users and is primarily spread through spam email campaigns.
Stegano Embeds Malicious Code in Banner Ads
In the past few months, researchers have been seeing a steady rise in the malicious ad campaign dubbed ‘Stegano’, which places malicious code into the parameters controlling transparency for pop-up banner ads. This recent campaign could potentially lead to millions of end-users becoming infected, as the altered ads have been found on many high-traffic news sites that typically have higher levels of security. Once the code ensures the system is running Internet Explorer, it begins redirecting the victim to sites hosting Adobe Flash exploits and attempts to infect and gather sensitive data. Fortunately for many users, several of the Flash exploits have already been resolved, which will lead to fewer infections.
Pennsylvania Prosecutor’s Office Pays Ransom
While the Avalanche Network was being dismantled by cooperating government agencies last week, the prosecutor’s office in Pennsylvania was recovering from a cyber attack which demanded a $1,400 bitcoin ransom payment. The attack was linked to a 2015 employee breach, but the after effects are still being seen after they decided to pay the ransom. In the six-year span that the Avalanche group operated, they are credited with infecting over half a million computers across nearly 200 countries.
Indiana County Out $200,000 After Ransomware Attack
Recently, it was announced that Madison County, Indiana spent a total of $200,000 in the wake of a ransomware attack on several county offices. With a ransom of $21,000 being paid out to the attackers, the additional expenditures were to recover their infected systems and provide better long-term security, including a backup solution for their data. Even with a high ransom, it’s not surprising to see the costs continue to rise as the victims scramble to rebuild and begin the hard task of creating and implementing a cybersecurity mitigation plan.

by LeVar Battle | Dec 7, 2016 | Home + Mobile
Corny title aside, ‘tis officially the season for online shopping, and that means a drastic increase in phishing scams. In order to obtain sensitive information from specific organizations and people, these threats have become increasingly sophisticated and are carefully crafted. According to the latest Webroot Quarterly Threat Update, 84 percent of phishing sites exist for less than 24 hours, with an average life cycle of under 15 hours.
“In years past, these sites could endure for several weeks or months, giving organizations plenty of time to block the method of attack and prevent more victims from falling prey,” said Hal Lonas, chief technology officer at Webroot. “Now, phishing sites can appear and disappear in the span of a coffee break, leaving every organization, no matter its size, at an immediate and serious risk from phishing attacks.”
3 things you NEED to know about phishing
During 2016, Webroot has observed an average of over 400,000 phishing sites each month. To keep up with the incredibly short life cycles and sheer volume of phishing sites and URLs, you have to abandon old techniques that use static or crowdsourced blacklists of bad domains and URLs. There are over 13,000 new malicious sites per day, approximately 11,000 of which last 24 hours or less, rendering static lists obsolete within moments of being published.
Nearly all of today’s phishing URLs are hidden within benign domains. Since phishing attacks no longer use dedicated domains, URLs must be checked each time they are requested. At the speed of today’s attacks, a page that was totally benign just seconds ago may have since been compromised.
Google, PayPal, Yahoo, and Apple are heavily targeted for attacks. Cybercriminals know to impersonate sites that people trust and use regularly. Webroot took a closer look at the companies for which impersonation would likely cause the largest negative impact. Of these “high-risk” organizations, Google was impersonated in 21 percent of all phishing sites between January and September 2016, making it the most heavily targeted.
Emails to avoid
With the holiday season in full swing and the New Year fast approaching, hackers are up to their old tricks. According to Mike Trammell, senior director, office of the CISO, Webroot, we should all be wary of emails containing UPS, USPS, and FedEx shipping alerts; 401k/benefit enrollment notices; and miscellaneous tax documents from now through the end of January.
So far, we have seen the following email subjects related to phishing:
- FTC subpoena
- RE: insurance
- Shipping status changed for your parcel # XXXXXXXXX
Be on the lookout for these types of messages in your inbox, since they’re likely to be phishing attempts that could lead to credential harvesting, ransomware infections, and more.
Our holiday wish for you
With holiday gifting on the horizon, the scammers are out in force, so remember to be extra vigilant. Remind your families, friends, colleagues, and clients to use secure and reputable websites and to only click links from sources they trust. Particularly at this time of year, if a stranger contacts you or anyone you know, whether by phone or by email, remember that they might not be who they claim to be. Before giving them any information or money, try contacting them back through their publicly available contact information.
From everyone at Webroot, we hope you have a secure and joyous season, and a happy new year!

by Connor Madsen | Dec 2, 2016 | Industry Intel
Between a handful of high profile network hacks and the steady stream of ransomware attacks, the last week of November didn’t pull any punches in the constant sparring match that is cybersecurity. In the wake of headlines about a US Navy breach, large scale network outages across Germany, and more, internet users across the globe must stay watchful and wary of their next click.
US Navy Sees Massive System Compromise
Officials in the US Navy have been notified of a security breach stemming from a Hewlett Packard Enterprise contractor whose laptop had been compromised. Currently, the Navy is contacting those who may be a part of the nearly 140,000 names and social security numbers that were affected, though it is still unclear on exactly how the breach occurred. With the steady rise in cyberattacks, the stress on IT departments of all sizes is mounting to defend against future attacks.
Tech Support Scammers Using Ransomware to Boost Income
Researchers have discovered an unsettling evolution to the traditional cold-calling tech support scams: executing ransomware on their victims’ computers to ensure payment for their “cleaning services”. While typical scammers will attempt nearly anything to get personal information, the use of ransomware takes the threat one step further by maliciously forcing payment regardless of any services rendered. Even worse for victims of VindowsLocker—as the ransomware is dubbed–the authors failed to properly setup the ransom transactions and thus, users may be unable to regain their files even if the ransom is paid.
UK National Lottery User Accounts Hacked
Major website hacks are occurring regularly due to reused login credentials, and it’s still a shock when a large site operator has to begin notifying tens of thousands of users about a possible data breach. Now we’re adding the UK National Lottery to the list. Only a small fraction of the National Lottery’s users were compromised, but Camelot, the operator for the lottery, has been forcing password resets for any potentially compromised individuals. While password re-use is the likely cause of the breach, it is still uncertain why the Lottery didn’t offer any additional authentication prior to the user accounts that were taken over.
San Francisco Train System Brought Down By Ransomware
In recent days, it has been discovered that the San Francisco Municipal Transit Agency was taken offline with only a poorly worded ransom message displaying for customers and employees alike. The attack led to the SFMTA providing free rides to customers while the issue was being resolved. In a surprising stance, the excessive ransom demanded–100 bitcoins totaling over $70,000 USD—was not paid to the attackers. For many public utilities and services, having the capability to promptly return to normal functions after such an attack is extremely important, and fortunately the SFMTA have announced that no customer information was compromised.
German Telecom Provider Hit with Mirai Variant
There is no doubt the world is now more attentive after the last Mirai botnet attack that took down several prominent sites. Yet, a similar variant has been deployed keeping DSL customers in Germany disconnected. Recently, nearly 900,000 telecom customers have been unable to access anything reliant on their DSL routers, which have been under attack for several days. By scanning for commonly open ports on routers, the attackers are able to remotely execute code resulting in a widespread DDoS attack.

by LeVar Battle | Nov 30, 2016 | Home + Mobile
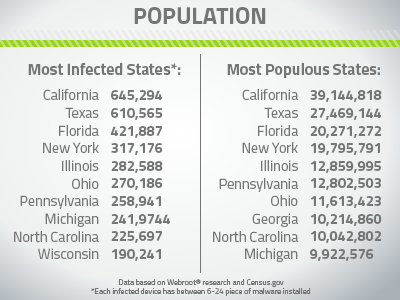
The sheer number of cyberattacks lately led us to this question: which states are at the greatest risk of a cyberattack? Naturally, we took it a step further. We looked into data on population and population density in an effort to find correlations.
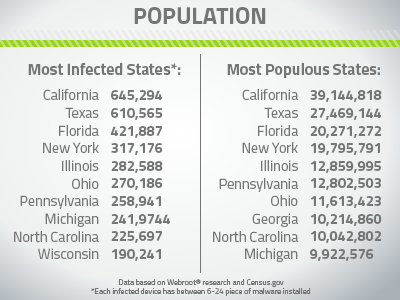
Which are the most infected states?
Opening up our list in the top three spots are California, Texas, and Florida. These three states were both the top three most populated and the top three most infected. This immediately led us to some questions: is the only correlation between states and the number of infections population? Based on these top three, that might be a safe guess.
Pulling up the rear of the top 10 are North Carolina and Wisconsin. North Carolina held strong at #9 for the Census’ most populated state and as Webroot’s 9th most infected state. The only major difference we noted is the fact that Wisconsin made it onto the list of the most infected states, while Georgia, 8th for most populous, doesn’t even rank.
Wait a second, Georgia doesn’t even rank? For the record, Wisconsin is the 21st most populous state, which puts them way outside the range of the top 10. What’s even more surprising about this discrepancy is that Georgia’s population is at 10,214,860 and Wisconsin’s is about half that at 5,771,337.
So, I think that safely puts our “more people equals more infections” theory to bed.
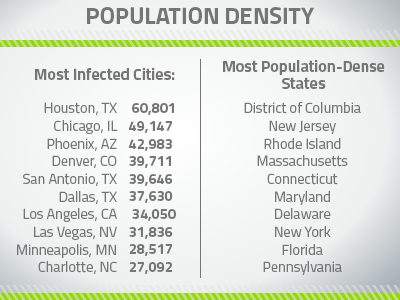
How do the most infected cities stack up?
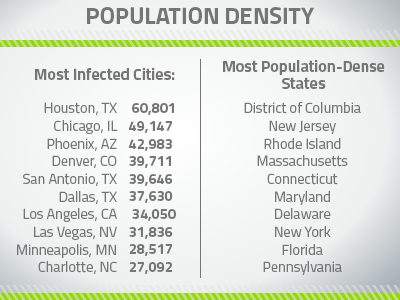
The most infected cities in the U.S. compared to a list of the most populous cities proved even more surprising. Since we noticed that there wasn’t a strong correlation at the state level, we wondered about the city level instead, and took a side-by-side analysis of the most infected cities and most population dense areas of the U.S.
The first thing we noticed in the above is how little correlation there seems to be between population density and the number of infected devices in the city, which we expected would have some impact. In fact, a quick glance at the list shows that none of the most infected cities are in any of the most population-dense states.
Additionally, even though Texas is 2nd on our list of most-infected states, it has its infections more localized in its larger cities. As a point of comparison, consider that NYC is one of the most population-dense cities in the U.S., but it conversely doesn’t even make it into the top ten for the number of infected devices.
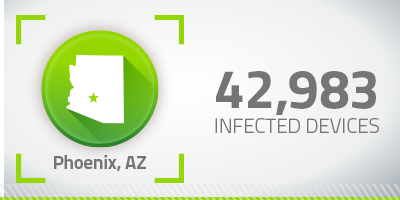
Another example of an apparent contradiction to our hypothesis is that Arizona, which doesn’t even make it into the top ten for most infected devices or for population, but look how many infected devices reside in Phoenix:
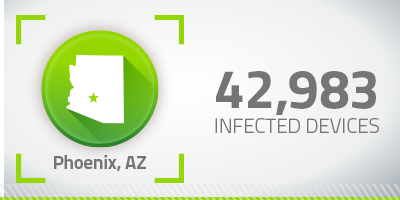
Although Phoenix is right behind Chicago and Houston in the number of infected devices, it’s a significantly smaller city. The same goes for Denver. Even though Colorado is at #23 for population and infected devices, Denver itself nonetheless makes its way into our top ten. Maybe Webroot users have some hometown pride?
Cybercriminals have no geographical bias. Whether you live in a big city or small town, east or west coast, you’re susceptible to being a victim of cybercrime. Protect yourself with award-winning security.

by Kelvin Murray | Nov 23, 2016 | Industry Intel, Threat Lab
For many years now, Microsoft has offered a system with Windows that allows you to take control of another machine. This has been invaluable for system admins that need to control servers and other Windows machines, without having to run around from office to office or site to site. Easy takeover of machines does come with risks. The protocol known as Remote Desktop Protocol (RDP) and the Remote Desktop Connection software that relies on it are often victims of simple attacks. These attacks have been on the rise in recent years and are extremely popular at the moment, as they are enticing for cyber criminals that seek to compromise the admins and machines that control whole organizations.
How is Remote Desktop Protocol a security risk?
RDP often uses a particular port that is easy to locate in a scan. And unfortunately, the default account username for an admin is often Administrator. While it’s no secret that having a poor password policy is not ideal for server security, it’s worth reiterating here it can mean that hackers can try huge amounts of passwords before anyone is alerted or an account is locked out.
Once an intruder gets admin access, they can deliver specialized malware or remote access tools that can often be almost impossible for any security solution to detect. With admin privileges and route access to the desktop, maximum damage can be done. This stresses the importance of endpoint protection, as well as policies, monitoring, logging, backups and incident response.
How to protect & secure your organization from Remote Desktop attacks
Preventing such brute force attacks isn’t as complicated as it may seem. You can employ a few easy actions to keep your organization safe:
Prevent scanning for an open port
- Change default RDP port from 3389 to another unused port
- Block RDP (port 3389) via firewall
- Restrict RDP to a whitelisted IP range
Prevent attackers from gaining access if RDP is enabled
- Create a Group Policy Object (GPO) to enforce strong password policy (GPOs are important and should be common practice for your organization)
Optional
- Require two-factor authentication
Getting to the bottom of suspicious activity is vitally important and our team is here to help. Contact us today or learn more about our full suite of business cybersecurity solutions.

by Connor Madsen | Nov 18, 2016 | Industry Intel
Alarming Number of Sites Still Using SHA-1 Certificates
The January deadline for switching over to SHA-2 rapidly approaching. For the vendors that are still lagging behind, they will begin to see browser warnings to their customers stating the site is untrustworthy for processing sensitive information. Surprisingly, 1/3 of all worldwide sites are still using the insecure algorithm. Unfortunately for many of these vendors, switching to SHA-2 could take quite a bit of work, as they have to locate and identify their current SHA-1 certificates before the migration can start.
PoisonTap Tool Navigates Around Password-Protected Computers
Recently, a new tool has been making its name by allowing an attacker to gain access to a computer, even while locked, by simply plugging in a malicious USB. The tool, dubbed PoisonTap, gains access to any unencrypted internet traffic and captures cookies used to login to sensitive accounts. Once the information is captured, the tool installs a backdoor to allow the attacker further access to the computer, then transfers all data back to the attacker’s server.
Ransomware Steps Up Blackmailing Methods
Ransomware is still on a steady path of destruction, and one variant has gone the extra step to better ensure the ransom gets paid. By scanning the system for any trace of child exploitation or pirated content, the ransomware is able to display a directed warning message about any files found that it could then expose to the public. By threatening the user with releasing any incriminating files, the attackers hope for a higher number of victims paying the ransom, as it now holds leverage against the payment.
Adult Friend Finder Hack, Possibly Largest Ever
Recently, the adult dating site Adult Friend Finder, and its network of other sites, has fallen victim to one of the biggest data hacks on record. With nearly 412 million users accounts compromised, the network’s security is coming under scrutiny as nearly a third of the passwords found were stored as plain text files or relied on the long-outdated SHA-1 algorithm. Even more worrying, many of the passwords appear to be extremely simple words or number sequences that are likely being re-used alongside the same email address for other websites.
Corporation Chains Hit with Customer Service Malware Attack
In the past few weeks, many vendors have complained about receiving fake customer service emails that contain malicious attachments. These attacks begin by impersonating a customer trying to provide sensitive information via email, and coercing the company representative into opening said attachment. Once opened, the malware begins downloading additional tools for collecting and transferring sensitive information back to the attackers. This method of stealing consumer data is not new, but the approach of remaining on the phone for the duration of the attack is something few researchers have seen before.