by Connor Madsen | Dec 4, 2015 | Industry Intel
Greek Bank Cyber Attacks
Recently, several Greek banks were hit with a cyber attack that brought their systems to a halt for several hours. The hackers, claiming to be a group called the Armada Collective, demanded a bitcoin ransom be paid by Monday evening. The banks refused to pay, however, which caused the group to extend the deadline before unleashing another attack.
ModPOS on the Rise
As we enter the holiday season, a new point-of-sale malware is targeting major national retailers. The malware, named ModPOS, appears to be more advanced than previous POS infections, by using multiple different components to gather as much data as possible and encryption to hide it’s tracks. Fortunately for consumers, many retailers already use point-to-point encryption for payments, with many more expected to follow in the coming months.
Read More: http://www.latimes.com/business/la-fi-modpos-malware-20151125-story.html
Office of Personnel Management Hacked
In the past several months, it has become clear that Chinese hackers gained access to the U.S. Office of Personnel Management and exposed the data of over 20 million federal employees and their families. The Chinese government has stated that they captured the hackers responsible for the attacks, though these reports are still unconfirmed.
Read More: https://www.washingtonpost.com/world/national-security/chinese-government-has-arrested-hackers-suspected-of-breaching-opm-database/2015/12/02/0295b918-990c-11e5-8917-653b65c809eb_story.html
VTech Hack
With high tech toys becoming more prevalant, the risks of children becoming victims of cyber attacks increases as well. The latest breach comes from Hong Kong based toy company, VTech, whose servers were attacked and lead to the exposure of nearly 5 million customers’ data. The hacker, who has remained anonymous, was able to access nearly 200GB of pictures, chat logs between parents and children, and usernames/passwords for those accounts.
Read More: http://arstechnica.com/security/2015/11/hacked-toymaker-leaked-gigabytes-worth-of-kids-headshots-and-chat-logs/
Security in the Health Industry
For quite a while now, most healthcare facilities have lacked the infrastructure for increasing their data security, and simply allowing employees access to most data with a username/password. This has recently changed, and now many hospitals across the U.S. are adding two-factor authentication to their security protocols. This boost in security, along with additional training for employees will decrease the chances of a data breach in the future.

by Dan Para | Dec 2, 2015 | Industry Intel, Threat Lab
Any time a malware variant hits the news we get numerous requests for information. It is typically quite difficult to provide any information based on names that have been given to threats. A simple way to illustrate this is by using a service such as Virustotal and seeing what name other AV companies use for the same threat. I found a recent article about a new threat that contained a link to a write-up by an AV company including MD5 hashes for the file samples used for the write-up. Below are screen shots of the Virustotal results for one of those files.
The first thing I noticed was that there are numerous names that this is detected as, and they are rather inconsistent. Many of the names used are generic, and there are quite a few heuristic detections included in the results. Another thing I noticed was that the name of the malware from the article and the write-up for this file is nowhere to be found. The AV company whose write-up I got the sample from does detect the file, just not by the name that was in the write-up.
What this shows is that, even though this malware sample was found with a specific name, it is widely detected by generic and heuristic detections. The name that it is detected as becomes rather irrelevant. Identifying new malware and taking it apart to determine how it works and what it does is certainly important, but at the end of the day, simply detecting a file as malicious and removing it is what really matters.

by Nathan Wyman | Nov 25, 2015 | Home + Mobile
With the two most hectic shopping days of the year rapidly approaching, you may be preparing to nab a deal… but identity thieves are just as busy trying to nab your financial information. While you’re out looking for the best deals
online and in retail shops on Black Friday and Cyber Monday, keep these security tips in mind to protect your identity:
- Try to use a secure payment method whenever possible. This includes Paypal, prepaid limited use debit cards, and credit cards that are separate from your primary bank account. Using a debit card that is tied to your primary bank
account is the least secure form of payment, as a security breach poses the greatest financial risk.
- When you purchase something from a small independent business online, make sure that the checkout process is a “Secure Site”. Look for a yellow padlock in the browser bar as well as “HTTPS” at the beginning of the website (as compared to “HTTP” with no “S” at the end, which stands for “Secure”).
- Make sure that your operating system and security software are up to date. If you use Webroot SecureAnywhere, your software should automatically update itself whenever new versions are released. If you’re interested in using Webroot SecureAnywhere to protect your devices, CLICK HERE for a 14-Day Free Trial.
- Don’t make online purchases while using public WiFi connections, such as restaurant or mall hotspots, because these networks are prime targets for identity thieves and hackers. Shop only from trusted wireless connections such as home and cellular networks.
- Never send sensitive information such as Social Security Numbers, passwords, bank account numbers, or credit card numbers through e-mail. This is not a secure way to send sensitive information and legitimate companies will ask you to use some form of secure site to transmit the necessary information.
- When using an ATM, inspect the card reader before swiping to ensure that it isn’t fake. Lately, identity thieves have been planting card skimmers over ATM card slots in order to trick people into providing their PIN and magnetic strip information, and this technique is on the rise.
- Watch cashiers for skimming, which is when your card is swiped once at the register and again through a hand-held scanner the size of a cigarette lighter. Most registers allow you to swipe your card yourself; if a cashier asks to swipe your card by hand and turns away or puts both hands out of your sight while holding your card, ask to see a manager.
- Review your credit card and bank statements to ensure that there are no unusual or fraudulent transactions. If you identify any suspicious activity, contact the appropriate financial institution immediately to address anny accounts that may have been compromised.
We hope that keeping these security tips in mind will allow you to shop with confidence and safety during the upcoming sales events.

by Connor Madsen | Nov 20, 2015 | Industry Intel
A lot happens in the security world, some big and some small, and many stories get lost in the mix. In an effort to keep our readers informed and updated, we present the Webroot ThreatBrief, highlighting 5 major security news stories of the week.
Encrypted messaging apps used for terrorist communication
In the wake of the recent terrorist attacks in Paris, authorities are looking more at encrypted messaging apps as likely communication means for terror organizations. Apps such as Telegram, offer end-to-end encryption for group chats, although the risk in using them is high. Along with the less-than-stellar encryption, the app also uploads your entire Contacts list to Telegram’s servers. In response to the blowback it had been receiving, Telegram has banned nearly 80 ISIS-related channels.
Read more: http://www.nytimes.com/2015/11/17/world/europe/encrypted-messaging-apps-face-new-scrutiny-over-possible-role-in-paris-attacks.html?_r=0
Response Plans for Cyber Attacks
As the risks of cyber attacks increase for businesses, it is becoming crucial to have a response plan in place, to avoid major loss of data. One of the best ways to reduce the chances of a cyber attack is to implement security training for all employees, as negligence is highly likely and the known cause of multiple past breaches. Additionally, it is good to regularly conduct security assessments to determine any vulnerabilities and to have a stronger understanding of what data is being stored and the best method for protecting it.
Read more: http://www.information-age.com/technology/security/123459644/6-critical-steps-responding-cyber-attack
DDoS attacks occurring in Britain
On Wednesday, reports came in showing a high volume of DDoS attacks occurring mainly in the UK, after the hacktivist group known as Anonymous declared war on ISIS. The DDoS attacks, which overwhelm network systems with data until they reach a failure point, are thought to have originated from ISIS hackers, though it is nearly impossible to tell for sure.
Read more: http://www.cnet.com/news/british-spy-unit-reportedly-hit-anonymous-with-ddos-attacks/
Smart TV Security Concerns
With the great leaps that technology has made over the last decade, the rise in Smart TVs with network access has brought the Internet right to your living room. Due to the increased use for both homes and businesses, consumers should be cautious when allowing the TV to access their local network, as it could be used maliciously to gain access to sensitive information. Additionally, the remote use of webcams and voice-activation features could be used maliciously, to gain entry to a business or personal area, and should be disabled unless in authorized use.
Read more: http://www.technewsworld.com/story/81691.html
Recurrence of Dyreza for Windows 10
In the last week or so, there have been cases of the banking trojan, Dyreza, being found in Windows 10 environments. The latest variant is capable of killing processes used in endpoint security software, using injection into known good processes to continue running. Unfortunately for consumers, this update seems to have arrived just in time for Black Friday/Cyber Monday, as many will be doing their online shopping for the holidays.
Read More: http://www.theinquirer.net/inquirer/news/2435483/banking-trojan-dyreza-is-targeting-windows-10-and-microsoft-edge-users

by Blog Staff | Nov 12, 2015 | Industry Intel, Threat Lab
Lots of blogs, articles and posts have been circulating recently about the increase in mac malware, mostly due to the publishing of Bit9’s report. I think it is wise to clarify what is really happening in the world of malware for Macs. Yes, there has been an increase in malware but what category do they fall under? What the consumers should be aware of and what they should be less concerned with.
Most recently a Mac ransomware proof of concept was announced and as expected the media lost their minds. I have had the opportunity to speak with the creator of the POC and also was able to look into what it does along with what it means for future malware. The author is a threat researcher/developer named Rafael Marques from Brazil. His POC has brought massive attention to the security needs of OS X and the lack of concern that most people feel about Macs. His motive was not to create a malware to use in public mass but to help educate people that Macs are not as safe as they think. I asked him why he decided to create this and his response was to inform people “about the myth that there is no malware for mac”. I couldn’t agree more with him, I recently wrote a blog about the history of mac malware along with another one on how adware is bypassing popular ad-blockers. Although the program he wrote can do as intended, it would need to bypass a few security features thus making it a little more difficult but not impossible. A quote from Cory Doctorow best sums it up, “never underestimate the determination of a kid who is time-rich and cash-poor.”
This is where the public typically gets lost in the industry terms. The proof of concept that he created is malware, but most of the encounters that we come across on macs are not this intense, these are instead PUAs (potentially unwanted application). PUAs are still considered malware for the most part, but they are not really looked at as something to be as concerned with. 2015 has really been the year of PUAs. Every day I go through samples that contain a majority of these PUAs, most of which are adware. These adware programs will try to hide a legit programs and run in the background just to get you to click on annoying pop-ups. VSearch, Genieo, IronCore, Bundlore, Wedownload… These are just a few that we come across every day.
While these programs don’t cause any real harm to the system they do help in showing consumers that Macs are not invincible. Adware is more like a testing ground for malware authors, they create these to figure out ways around security and users. Once an author is aware of how to bypass all the security measures, what’s to stop them from writing a more complex threat? Of course one could argue that my intentions are to get people to buy anti-virus, but I didn’t go into this career to sell a product, I choose my path to help build security and promote it to the world. I think it is very important that people began taking Mac security serious. The next time a ransomware for mac comes out, it may not have a researcher like Rafael creating it to bring awareness, it may have someone wanting to make money on your expense.

by Tyler Moffitt | Nov 5, 2015 | Industry Intel, Threat Lab
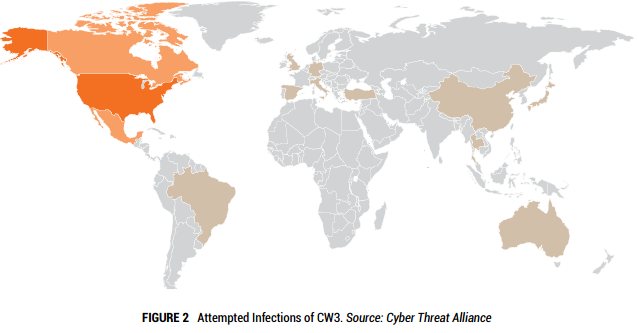
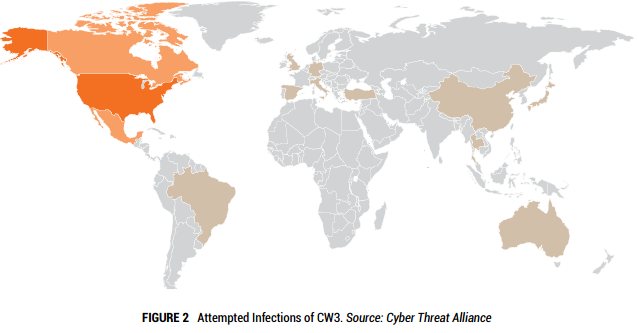
We know that Cryptowall 3.0 has been hugely successful for the cybercriminals netting them nearly $325 million in its debut year. With over 800 command and control URLs and over 400,000 attempted infections it is easily the most prolific threat of 2015.
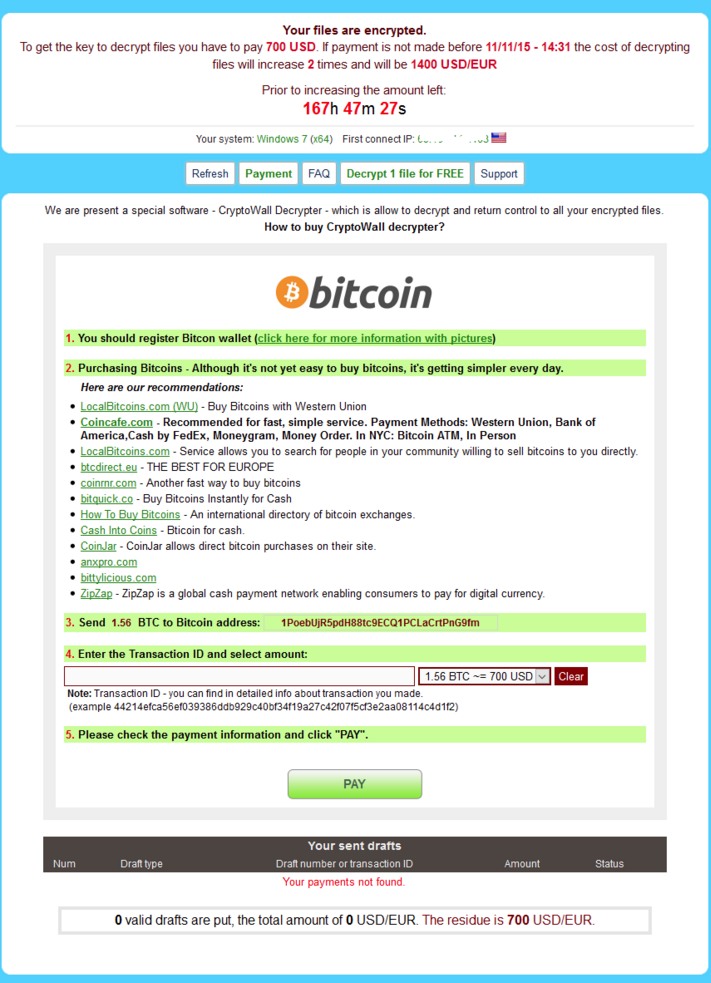
Here it is, what we’ve all been waiting for – the newest edition of Cryptowall. This ransomware comes out with new revisions almost as much as Apple does with iPhones. The bad news is that both will set you back $700.
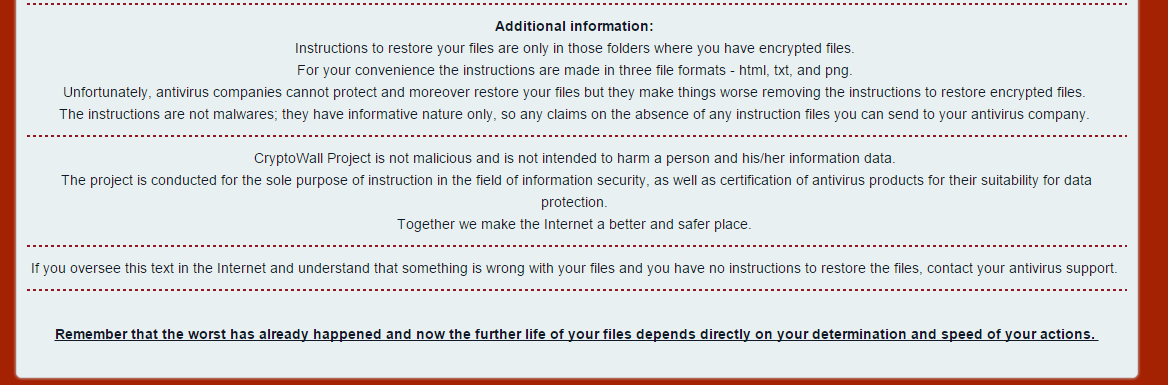
This is the locally saved html web page that it sends you to. If you don’t notice that, you’ll definitely notice that all your files have been encrypted and a new update is that the entire name of the file has been randomized so you no longer know which file is which. This is to create confusion on the severity of damage and increase the chance that you’ll pay out. As you can see from the first image they congratulate and welcome you to CryptoWall community – how nice. The rest of the instructions are pretty standard on informing you how install a layered tor browser and then connect to the darknet to pay them and get your files back. Notice the additional information they have at the bottom:
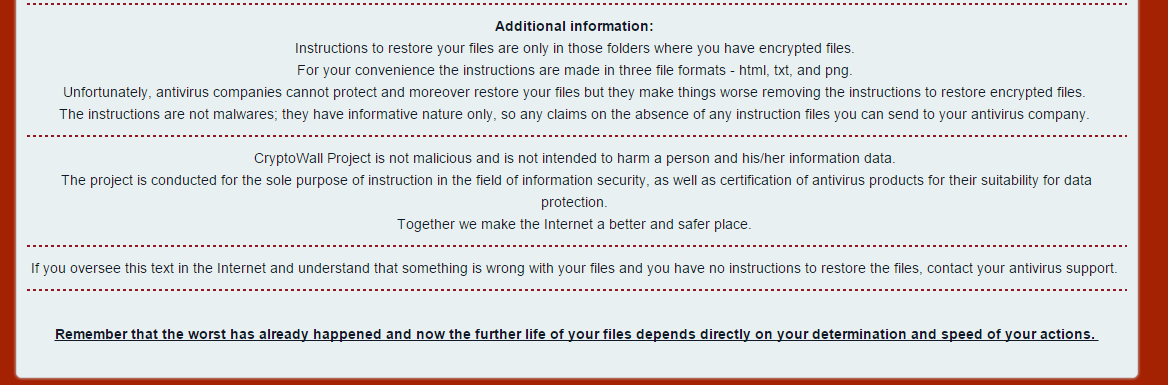
These guys actually claim that the CryptoWall is NOT malicious and not intended to harm your data “Together we make the Internet a better and safer place” – who are they fooling? Either way this is new and not seen on previous variants.
On to the payment website and and we can see they immediately want $700. It wasn’t even a year ago when the default payment was $300…
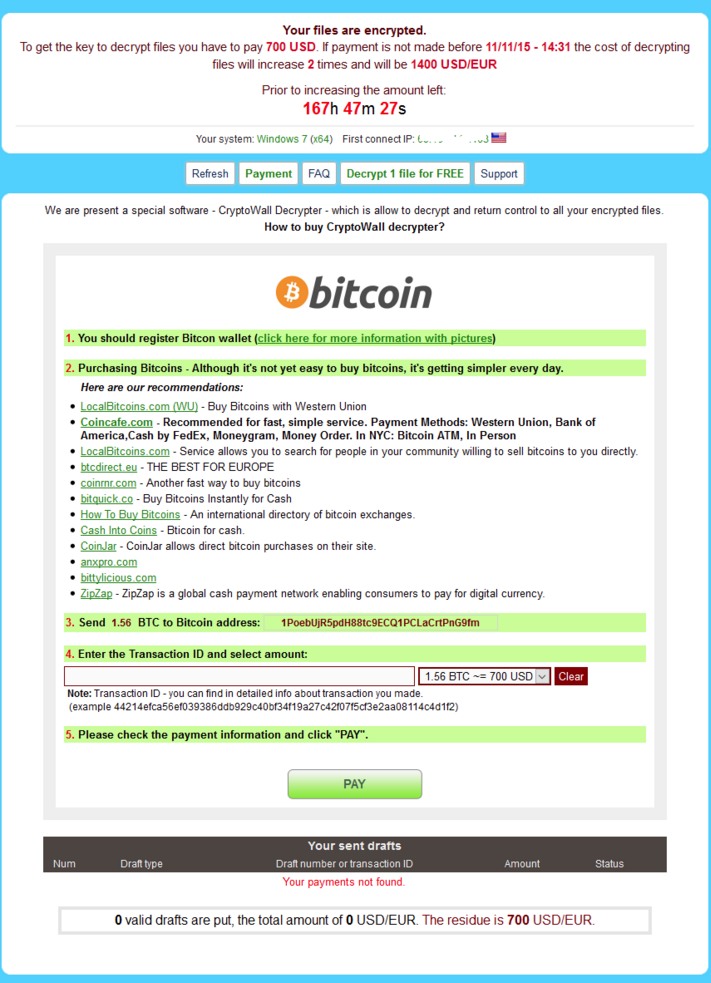
There are some new features like the a free decrypt which was first introduced by coinvault that we discovered a while back. It obviously has helped convince people that the decryption routine is fairly easy to get your files back and that the ransom is genuine and you will get your files back.
We’re currently reversing the sample and will have a more in-depth writeup of its infiltration, payload obfuscation, injection, and file encryption next week.
MD5 analyzed: E73806E3F41F61E7C7A364625CD58F65
Additional MD5 seen:
63358929C0628C869627223E910A21BF
5C88FCF39881B9B49DBD4BD3411E1CCF
32ACFA356104A9CE2403798851512654
CE38545D82858C7A7414B4BD660364A9
5384F752E3A2B59FAD9D0F143CE0215A
CF6D69E47B81FA744052DA33917D40F3
53C82D574E054F02B3163271262E0E74
A891CED376809CF05EFE4BB02EB2CBF3
5384F752E3A2B59FAD9D0F143CE0215A
Webroot will catch this specific variant in real time before any encryption takes place. We’re always on the lookout for more, but just in case of new zero day variants, remember that with encrypting ransomware the best protection is going to be a good backup solution. This can be either through the cloud or offline external storage. Keeping it up to date is key so as not to lose productivity. Webroot has backup features built into our consumer product that allow you to have directories constantly synced to the cloud. If you were to get infected by a zero day variant of encrypting ransomware you can just restore your files back as we save a snapshot history for each of your files up to ten previous copies. Please see our community post on best practices for securing your environment against encrypting ransomware.

by Grayson Milbourne | Oct 30, 2015 | Industry Intel, Threat Lab
As National Cyber Security Awareness month is coming to an end, the 2016 presidential election cycle is building momentum and increasingly becoming our nation’s primary focus. Love it or hate it, the presidential elections also create an ideal environment for thieves and cybercriminals alike. Preying on the media’s attention to buzzworthy news, hackers are busy preparing scams to exploit the attention and distraction it inevitability causes.
While the election night is still over a year away, there will certainly be a plethora of media attention given to the event. From social media’s nonstop discovery of breaking news stories to the saturation of TV with campaign ads, the election will become more front and center in our everyday lives. And in this flurry of information are many threats and scams.
While I cannot predict the specific events of the future, I can certainly look at the past to identify trends that still occur today. One such trend and tactic is to use large media events and topics as bait to lure people towards less trustworthy websites, or, in the case of an election year, to fake campaign donation websites. There are many examples from the past, from the death of Osama Bin Laden to the tragic disappearance of MH370, fake websites and social media scams were quick to follow.
So how do you stay protected?
In the wake of a big news story, make sure to be on high alert and question your curiosity when reading up on the event online or through social media. Don’t just click without thinking, consider the source of the link you’re about to click and the destination of that website. Using security technology is also helpful when browsing the web. Aside from using WSA, I also recommend using Chrome with a responsible ad-blocking extension. This combination will keep you defended from online attacks in the event you stumble across a malicious website.
Another tactic that has grown considerably in the past year is the use of telephone-based scams. While these attacks often target banking customers, the presidential election cycle creates a perfect opportunity for attacks where scammers will pose as a campaign representative requesting donations. While this isn’t technically cybercrime per se, these attacks often attempt to gain enough information to lead to further compromises in the cybercrime space.
So how can I tell if the caller is a scammer?
As a rule of thumb, I would not provide any personal information, email address, phone number, etc. to anyone who cold calls, no matter who they claim to be. That said, the election cycle creates a temporary exception in where you might not be surprised to receive a call requesting campaign financial support. Phone scammers can be very convincing and have answers to many initial security concerns. The person might suggest sending you an email with more information about the cause they are campaigning for, which will then be used to further the scam along. A good way to handle such callers is being firm in that you don’t give out such information, and request to be removed from their calling list. If you want to donate, call or visit the foundations website directly. You can also improve telephone-based security on a smartphone by using a phone ID app such as TrueCaller. Such a service can provide you with community-based information about an incoming call.
Ultimately, these are just two examples of threats that will use the 2016 presidential election to their advantage. As the election nears, the number of such attacks will increase and so must your security awareness. While National Cybersecurity Awareness Month has wound down, the lessons taught and learned will continue to be important in order to stay in front of the adapting threat environment.

by Tyler Moffitt | Oct 28, 2015 | Industry Intel
We all know cryptolocker and we all know the toll it’s taken on many individuals and companies. While the original cryptolocker has been shut down since FBI operation Tovar it has not stalled the many variants of encrypting ransomware from becoming a plague to the user (looking at you cryptowall). The “business model” just isn’t going away and is only seeing improvements as time goes on.
Recently in a blog post it was suggested by the FBI to just pay the ransom. With encryption being so sophisticated and the key never stored on the machine I can honestly say that I agree. If you really need the data that was encrypted and your current backup solution doesn’t suffice for the data you’ve lost there is literally nothing you can do to get that data back other than pay the ransom. It’s a sad state of affairs, but this is where we’re at – proactive backup solutions beforehand or bust. Sure there are tools like Shadow explorer that will work if you’re hit with something that’s not killing the Volume Shadow Service (VSS), but that is an elementary error and most encrypting ransomware campaigns are packing the best payloads that make no mistakes. If you have no recent air gap backup or cloud syncing backup that lets you keep old copies, you really have no options other than starting from scratch again and “sticking it to the hackers” but really only individual consumers have the financial freedom to make that choice. Most scenarios where I know victims paid the ransom are because it was a huge hit to their businesses productivity.
For example, let’s say a small business that works as a reseller ships out thousands of products a day and their label printing machine was hit with cryptowall. They aren’t able to print any of the custom saved labels that use on a daily basis and it’s catastrophic to their business for a couple days. The $300 – $500 ransom really is nothing in comparative to the thousands of orders that they couldn’t ship until they get those shipping labels. Most of the time they spend deciding if they should pay isn’t because it’s too much money, or they “shouldn’t support terrorists” but the concern that they wouldn’t get their files back and would be effectively scammed again. In the end, after failed searches for backups and having this huge await shipment line, they just decide it’s worth it to risk throwing the money away and pay the ransom. They get their files back pretty quickly and now can resume shipping.
Most stories are similar to this and when I’ve asked them how paying the ransom went they’ve said that if they knew it would be that easy to get their files back, they would have paid sooner. This is where we are at – criminals putting a gun to our files and demanding payment. It’s worked great the past couple years since it started and it’s only getting better; I see no end sight to this.
Looking forward is even more troubling since once the bad guys start figuring out who can afford more of ransom is when things start getting real hairy. Sure $500 is nothing to resume business as usual, but what if it was a $50k ransom? There would be entirely different discussions internally before deciding to pay.

by David Kennerley | Oct 28, 2015 | Industry Intel, Threat Lab
Recently I was asked to give my thoughts on mobile malware. I was asked this in relation to a number of reports released earlier in the year that were in my view misinterpreted. At the time many experts claimed mobile malware had been a much-exaggerated threat, based on such a large proportion of unwanted mobile apps/programs were seen to be adware.
Personally, I think it’s better to discuss mobile threats, mobile threats are more than just mobile malware. Many legitimate Apps have been seen over the last few years to be open to serious data leakage and only recently we have seen the discovery of Android’s “Stagefright” vulnerability – pegged as the “worst Android bug to date”. Receiving a simple MMS message with crafted exploit code, and without any interact from the victim, a hacker is able to do anything from stealing private communications to possible taking control of the device itself.
Read more: https://goo.gl/xCvGa6
In September, we saw “XcodeGhost”, this highlights the Apple App Store isn’t immune to serving up compromised apps. The Xcode development tools are used by iOS app makers. The original package was copied, modified, and then re-distributed for download. Apps built using the modified version were injected with malicious code, then published to the App Store.
Read more: http://goo.gl/VYEBgk
Mobile malware is a problem and is getting bigger with the ever increasing growth of the mobile market. There is concern that enterprise decision makers may misinterpret such reports and may not take mobile security as seriously as they should. Enterprises should be very concerned about mobile threats, this includes, mobile malware, mobile vulnerabilities and mobile data loss.
Mobile adware itself is a huge problem and needs to be addressed. Adware can collect personal information from the device it’s installed on, often without consent, including many pieces of PPI. Enterprises allowing such devices to connect to the private network should be seriously concerned, information is power, and company secrets are a secret for a reason.
The recent case of “Gunpoder” also highlights a new strategy malware writers are using. The game emulator app looks and behaves like adware, all while stealing PPI from the infected Android device. Many AV companies classified this malicious app as adware and many users thinking that adware was ‘more annoying than dangerous’ allowed the app to run.
Read more: http://goo.gl/Wm6Oyz
Cyberattacks are more prolific than ever, and businesses are clearly struggling in the battle of keeping their employee and customer data safe. Cybercriminals look for the simplest method to achieve their objective, if that’s through a mobile device and an uneducated user, then so be it. Mobile infiltration is often a precursor to further attacks.
Ignoring mobile malware and security, at any level, could have huge repercussions on a business’ reputation and customer loyalty as well as financially – it’s important not to leave the front door open.
So what can we do?
With all security implementations, striking the balance between mobile security and productivity is an on-going challenge. At present I would suggest it’s weighted towards productivity. Productive employees are great, but at the same time the company’s assets have to be properly secured. Therefore the fight against mobile malware needs to be appropriately evaluated in terms of personnel and monetary resources.
Mobile security is just another problem that arrived on the doorstep of the security and/or IT team, and on many occasions without any extra budget allocation. Like with many facets of cybersecurity it only becomes a priority after the inadequate defences are breached and company stakeholders want answers.
Companies need a mobile security strategy. They also need to follow best practices and keep abreast of industry information and security bulletins. Any strategy must consider corporate devices and BYODs. Organisations need to keep on top of patch management and understand what technologies best address their security needs, these may include centralised app management and app reputation technologies and in case of device loss – consider encryption and remote wiping.
Like with any device on a network, threat protection should be installed and kept up to date. Webroot offers mobile security apps for both Android and iPhone. The corporate network can be protected further by directing mobile traffic through special gateways with customised firewalls and security controls. Mobile devices should be configured to avoid unsecured wireless networks.
It goes without saying that devices need strong authentication and password controls.
Remember, mobile security and security in general is a continuous practice. It’s essential to implement a comprehensive mobile security strategy, then check how well training and policies are being interpreted and implemented with regular mobile security audits and tests. Communication between the organisation and its employees is vital – the risks and potential consequences need to be understood by employees through continued user education. At the same time organisations need to understand and respect the now slightly blurred boundary between business and personal.
Cybercriminals only need to find one hole in the defence, whereas security professionals have to secure all possible points of entry. It’s a battle we may lose from time to time, but we have a responsibility to make it as hard as possible for our adversaries.

by Nathan Wyman | Oct 26, 2015 | Industry Intel, Threat Lab
As the 12th annual National Cyber Security Awareness Month enters its final week, we’ll look at the future of technology and the potential vulnerabilities that come with it. As President Barack Obama has stated, “Cyber threats pose one of the gravest national security dangers the United States faces,” and that is why we all need to be mindful of the “smart world” we now live in. It is our shared responsibility to be aware of the importance of cyber-security as the number of Internet-connected devices around us increase. Surveys show that in 2014, 47% of adults in the United States had their personal information exposed by hackers.
Our phones, tablets, and personal computers are the most obvious devices that need protection, but what about the “Internet-Of-Things” devices? From vehicles to watches to kitchen appliances, more and more of our household objects are becoming “Smart” items, and each device stores and transmits private personal data. Health monitors, baby monitors, coffee makers, home environmental controls; whatever the device, if it connects to the internet, it can potentially be exploited by a determined hacker.
This is something that all device manufacturers need to keep in mind, since most consumers won’t usually have the ability to install security software on these devices themselves. But there are a few security tips that we should all keep in mind:
1. Protect your network. This means changing the default Administrator password on your router, using strong (WPA2) wireless network encryption, and changing your WiFi password occasionally. See our “Tips for Improving Router Security” blog post for more information.
2. Protect the devices you can. Whether you use a PC, Mac, or Android device, you will need an antivirus application to protect you against malware. If your network is breached, having devices that are well protected will sometimes deter a hacker who is looking for easy targets. Webroot provides this defense with cloud-based malware detection that automatically stays up to date.
3. Don’t be an early-adopter. When a cool new device comes out, it’s tempting to be among the first to have it… but the first versions of any “smart” products are the most prone to security flaws. By waiting until a second generation device or a first software update for the device, you may reduce your risk of using an insecure product.
While the technology of the future becomes increasingly Internet-connected, it is our shared responsibility to remain vigilant about security and ensure that it is incorporated at every point of access.
For more information about this month’s themes and events, see the Official Department of Homeland Security National Cyber Security Awareness Month page.